
Is a file safe? Tips to check it
Every time we use our devices and connect to the network, we are exposed to many security threats. There are many types of malware, such […]

Every time we use our devices and connect to the network, we are exposed to many security threats. There are many types of malware, such […]

In many cases it is convenient to carry out some changes in the Internet configuration. We do this to improve speed, gain stability and have […]
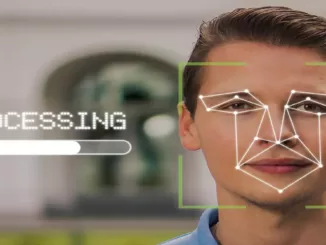
Today we have various methods to use biometric authentication. Some of the most used today are facial recognition, fingerprint and iris recognition. However, there are […]

This Tuesday Microsoft warned of a new Zero Day attack that affects Internet Explorer by taking advantage of Microsoft Office documents . At the moment […]

Low code platforms are an increasingly popular option for continuous enterprise software delivery, but they also pose new security challenges. Low code platforms are programs that developers […]

Surely by now we have all heard of Windows 11, Microsoft’s new operating system that will succeed the current Windows 10. If all goes well, […]

The dangers that we constantly have to face with our mobile device are numerous. Not only by browsing the Internet, since we could infect our […]

We present a complete analysis of a professional alarm to protect your home. Ajax Systems is one of the best manufacturers of professional alarms, both […]

When browsing the Internet, we leave a digital trail that reveals information about us. On some occasions, we want our public IP address to remain […]

Maintaining privacy and security when we use any account on the Internet is essential. There are many factors that can influence in one way or […]

Nowadays, there are many people who are in charge of carrying out scams to try to steal our personal or financial data . There are […]

Currently there are many platforms to communicate safely over the Internet. In messaging, the most secure by far is Signal, which does not even save […]

In some situation we may have had to block access to some websites. This task can be performed by software, such as by using some […]

Currently the vast majority of devices connect to the Internet via Wi-Fi or network cable. Generally the most used and because it facilitates mobility is […]

The way of working is constantly evolving. In that sense, some 15 or 20 years ago it was very common to transport and use reports, […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise