
How to Do a Google Search in Complete Privacy
Privacy is a very important factor for users. Our online data has great value and is sought by many marketing companies looking to include us […]

Privacy is a very important factor for users. Our online data has great value and is sought by many marketing companies looking to include us […]

Social networks are platforms widely used by users on the Internet. They offer us a wide range of possibilities, such as being in permanent contact […]
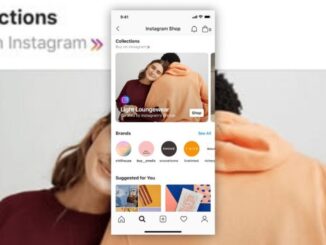
When you have an application capable of generating so much traffic on a daily basis, attracting millions of users who consume content on a recurring […]

One of the most popular questions on the internet these days is this. How much money do influencers earn? This profession has been exploited in […]

Working remotely has become very common in recent times. Many users have started working from home due to the pandemic and that also adds certain […]

The world of virtual reality is evolving. From the sensory reality dating to the new DNA matching technology, researchers have continued to find ways of […]

With the arrival of iOS 14, privacy-related news has been included, which is revealing some problems in third-party applications. With the new notice that appears […]

When browsing the Internet we can come across multiple pages that are dangerous. Many sites are designed to steal information and data from visitors. Some […]

Everyone knows that the least-visited place in the digital world is the second page of Google search results. That’s why people work so hard to improve […]

Internet speed is one of our main concerns and it bothers us that it goes too slow, that we have to wait, that the pages […]

The username and password are part of the access credentials for multiple applications, services and resources of all kinds. Just setting weak passwords can even […]

Internet services, the pages we visit on a daily basis, network protocols, change periodically, are updated and improved. This allows us to navigate more safely, […]

Privacy has become a very important factor for users. When browsing the Internet our personal information may be compromised for multiple reasons. It is a […]

Buying on Amazon has become a regular thing that makes life easier for us: its wide catalog offers us practically everything, from pens to laundry […]

In this article, we will go through a list of top 10 Stranger Chat Apps available on both the platforms viz. iOS and Android. Moreover, […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise