
Update BIOS in Dell: 4 Vulnerabilities to Hack Computers
There is no such thing as perfect software. All are susceptible to being hacked at some point when a vulnerability is discovered, so it is […]

There is no such thing as perfect software. All are susceptible to being hacked at some point when a vulnerability is discovered, so it is […]
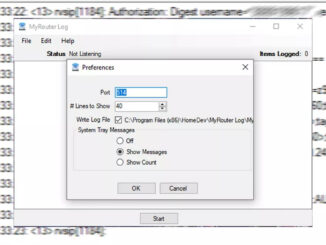
All routers have a system of records or logs where all the activity of our equipment is stored, in order to detect possible problems or […]

Antiviruses are becoming more and more secure, and it is usually rare to get infected by a virus if we have all the security updates […]

One of the biggest problems that users face on the Internet, or when using devices in general, is the loss of data. Losing all the […]

The popular manufacturer of network devices Zyxel has released a security advisory stating that cybercriminals are carrying out attacks on its firewalls and VPNs, with […]

It will sound too alarmist, but it is quite a serious issue since it involves the total loss of data that may have been stored […]

Encrypting data on hard drives or SSDs, partitions and files is essential today. Currently we have the possibility to encrypt the data of a NAS […]

We are increasingly aware that we need to keep our privacy safe. One of the simplest and most effective ways would be to use a […]

The use of Linux as the operating system of our team or server is, in itself, a symbol of security. Using Linux passwords is the […]

We always say that it is very important to keep our equipment and programs up to date correctly. In this article we are going to […]

NAS servers allow us to create our own private cloud at home, currently NAS operating systems allow us to activate a large number of services […]

Hackers often adapt to the circumstances in order to attack users and make a profit. There is no doubt that remote work has grown a […]

Phone scams seem to sprout like mushrooms and it seems really difficult to end them until there is a firm determination to do so. Alerts […]

The Ministry of Labor has suffered two hacks in three months. After not being able to fully recover on their own, they have finally had to turn to private […]

One of the alternatives we have to surf the net is Tor . It is a browser based mainly on privacy and security that allows […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise