With privacy and Internet security in the spotlight for a few years, more and more people hear about the Tor network. Many users are unaware of what it is, what it is for and what you can find in it. Today we will explain all the keys regarding the Tor network, and how we can enter it.
Tor’s story
Although an alpha version with the Tor network operated was announced in 2002, it was not until the following year, in 2003, when it was created by Roger Dingledine, Nick Mathewson and Paul Syverson as an evolution of the Onion Routing project, developed by the Naval Research laboratory of the United States.
Initially, this evolution was funded by the United States Naval Research Laboratory, but, at the end of 2004 until November 2005, it became sponsored by the Electronic Frontier Foundation, which is the civil liberties defense organization in the digital world.
Currently, the Tor project is managed by The Tor Project which is a non-profit organization oriented to research and education, and is funded by different organizations. Currently the Tor project is made up of a team that is led by Roger Dingledine, one of its creators.
As prizes in its history, Tor received from the Free Software Foundation the prize for social benefit projects of the year 2010 for allowing approximately 36 million people worldwide, using free software, to have experienced freedom of access and Internet expression while maintaining your privacy and anonymity. His network has proved crucial in the dissident movements of Iran and Egypt.
What is the Tor network and how it works
The Tor network, or also known as ” The Onion Router ” or ” The Onion Router, ” is a project that aims to provide the best security and privacy when we browse the Internet.
It is a distributed network in which the routing of the transmitted packets does not reveal its identity on the Internet, that is, it does not reveal its IP address. Of course, it is able to maintain the integrity and also the confidentiality of the transmitted packets.
We have to keep in mind that Tor is a parallel network and completely free. It has been developed to skip the control measures that some governments exert towards users. To achieve the anonymity and secrecy of the information that is consulted, or that is transmitted through the Tor network, we have intermediate nodes and exit nodes.
However, you should keep in mind that 100% Internet anonymity does not exist, and even within the Tor network we will always leave a trail.
Although it is a distributed network, we must take into account that it is not a P2P network, since we have the users of the network, the users that route the Tor network traffic, and finally, some users that do the service function Directory to navigate Tor.
One of the main objectives of the Tor network developers is to ensure that whoever uses the Internet has their identity protected, that is, the traffic sent by a user cannot be tracked in any way, so that they cannot reach it, or less, that its tracking is really difficult.
At present, the Tor network is mostly used by many users to guarantee their privacy on the web pages they consult.
Although the Tor network is not specially designed for it, it was discovered that using its network it is much more difficult for programs or countries that monitor and block access to certain content to achieve it, and, therefore, the user can access and not be detected.
For this reason, the Tor network is widely used in countries or places where communications are extremely guarded and where people trying to access this type of information are persecuted.
Anonymous routing does not guarantee that if you connect to a website, it cannot know where the connection comes from.
This happens because higher level protocols can transmit information about the identity, that is, the Tor network works by encrypting all the information at the entrance (user browser) and decrypts it at the exit (server where the web is hosted), so, whoever has an outgoing router of the Tor network, can see all the decrypted information so that, although he cannot know the sender, he can access the information. This is one of the weaknesses used by those who try to identify Tor network traffic.

An example is in Dan Egerstad, an expert in computer security, who created a server on the Tor network and controlled all the information that came through it to the Internet.
Thanks to that, he got passwords from important companies, embassies around the world and other institutions. To try to solve this great failure of the Tor network, and make sure that nobody can access the information that is being sent, it is advisable to use HTTPS, since it uses the secure TLS protocol.
The Tor network consists of a series of nodes that communicate using the TLS protocol. These nodes can be
- OR nodes: These nodes function as routers, and in some cases, also, as DNS. The OR nodes maintain a TLS connection with each of the other ORs.
- OP nodes : When we run the Tor web browser, they perform the function of the OP node and its function is to obtain the information from the directory service, establish random circuits through the network, and manage user application connections.
Directory Service
The directory service is a database that associates a series of information with each OR. This information is accessible to all other ORs and end users. It is used to have a knowledge of the network, that is, if you have few directory servers you run the risk of reaching a point whose failure can cause the complete system to fail, this could be a simple way to destroy the Tor network . The ORs are divided into main ORs that are directory authorities and then there are the secondary ones that are responsible for cache and backup.
Meeting points
The meeting points are intermediate places to send packages, and when they arrive there, be sent to their destination. That is, each end of the communication sends its messages to that meeting point, and from there they are sent where appropriate using circuits that hide the location of the destination.
Why use the Tor network
There are many reasons why one can use the Tor network, some legal, some il-legal. But the main advantages could be classified into the following categories:
- Block trackers : it has all occurred to us that, when searching for any product on the network, a few hours later we appear advertising about that product or related products. That is why one of the reasons for using a Tor browser, is that each website that you consult is isolated, in this way, third-party crawlers and advertising generators cannot “follow you” and, therefore, do not They can show you advertising about your web queries. Another advantage is that cookies, browsing history and web cache are not saved in Tor browsers.
- Surveillance : if someone infiltrates our local home network, you can know, see, and even check all our activity we do online, whatever. That is why using the Tor network guarantees that, if someone has infiltrated our network, they will not be able to know what we are doing on the Internet.
- Identification : when we navigate with a browser of current use, without realizing it we are generating and leaving a unique trail that can allow us to identify ourselves and know everything we are doing. This is due to the use of supercookies, cookies and of course, our public IP address. On the other hand, if we use a Tor web browser, this cannot be done, or at least, it will be much more difficult than if we did not use it.
- Security : The Tor network and its browsers work by encrypting several times all the packets that we transmit and receive when we are browsing, passing through several Tor nodes by adding several layers of security. Thanks to this, security and privacy is almost guaranteed, although we must keep in mind that everything leaves a trace and 100% security does not exist.
- Freedom : without a doubt, one of the most important reasons for using the Tor network is to be able to access all the information without censorship. Many countries governments are currently trying to hide certain information from their citizens, limiting access to different websites or portals on the Internet.
Many users will be wondering, why you should use the Tor network if you have nothing to hide. And the answer, as we have indicated above, is very simple: it has all happened to us once that searching for any product on the Internet, afterwards they did not stop sending us announcements about what we had consulted, sometimes they take hours to show us ads, and on other occasions some days. This is that many users take it as nonsense, one day it can turn against you, since you can consult something that you do not want to know, for example, a gift to a family member, and that because of the trackers fault you know what you have been searching
Using a Tor browser, you avoid, as we have said before, that third-party trackers collect your browsing data so that companies later show you advertising. Also, if you live in a country where your government hides information from you, using the Tor network, you can skip the blockages that apply to access that information.
How can I use the Tor network
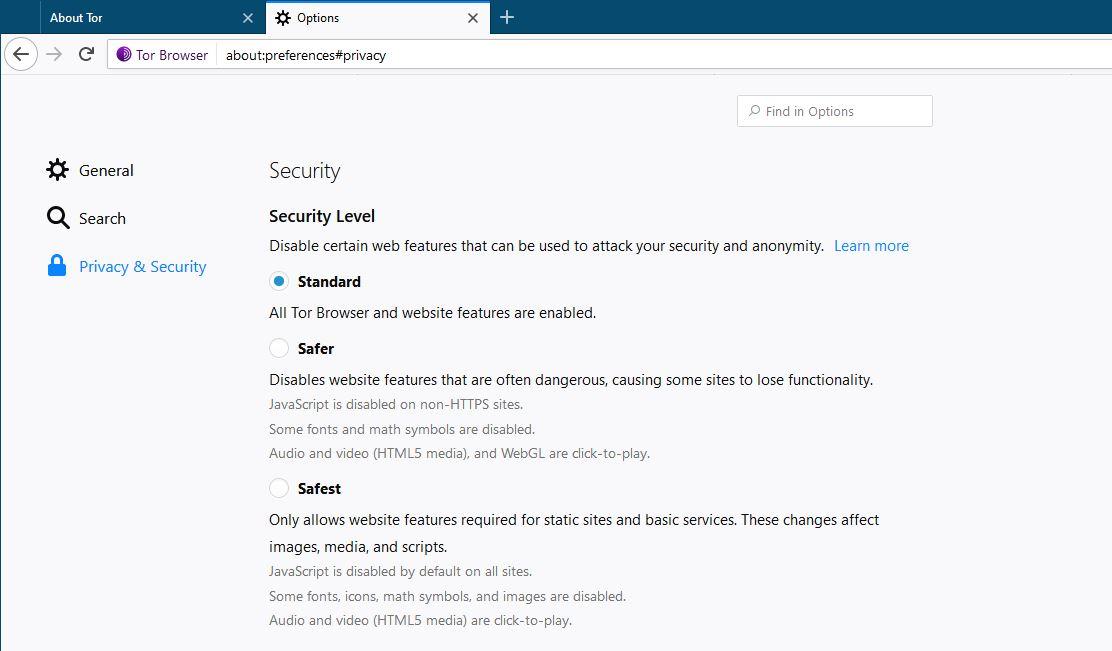
The easiest way to use the Tor network is to download a Tor web browser. One of the most famous browsers is Tor Browser, which you can download from the official website . However, there are many more browsers that you can use, but that depend on extensions or enter a code to activate the option of browsing the Tor network, such as Mozilla Firefox, Brave, etc. Our advice is that you use Tor Browser, by already coming prepared to navigate without having to do anything else.
One thing that we have to be clear about the Tor network is that there are no content search engines, as with Google or Bing, and that we must enter the website link we want to go. A simple way to start would be to consult The Hidden Wiki , from a Tor browser.
In case you want to have as much security and privacy as possible, we recommend you download the Tails operating system , an operating system designed specifically to be as anonymous as possible on the Internet, and that is completely free.
Controversies of the Tor network
While the Tor network has its very positive points, such as being able to be more anonymous (we will never be 100% anonymous) on the Internet, avoid trackers, and even evade censorship imposed by a particular country.
There are terrible aspects, such as hidden websites for drug sales, hired killers, private leaks, or anything we can imagine. This Tor network is also used to communicate between terrorist groups, sects and much more, so it is continuously monitored by the Police, in order to unmask and stop them.
Although, the Tor network can be a great solution for some countries when their governments hide information from their citizens, and to be able to access shared knowledge, or the privacy of our communications, users who decide to use it must keep in mind that in this network you can find anything, and you have to navigate carefully and under your responsibility to know where you enter.