None of the products we use on a daily basis is 100% safe. The key to making a device as secure as possible is that the company updates it, and that there are update mechanisms built into it . Not even the best-selling devices on the market are free from these flaws, and now one of Amazon’s most popular routers for fiber connections can be hacked in multiple ways.
We are talking about the TP-Link Archer C50 , a neutral router of which tens of thousands of units have been sold in Spain, and which has just over 8,900 reviews in the store. TP-Link is the world’s largest router manufacturer, selling 150 million units each year with a 42% market share. Therefore, it is not surprising that their products are among the best sellers in stores like Amazon.

TP-Link neglects the security of your router
In the UK, the router is an “Amazon’s Choice” product, so it ranks among the store’s best sellers despite having multiple vulnerabilities that make it susceptible to hacking. This has been alerted by Cyber News after having done an extensive security analysis of the Archer C50 .
This model has AC1200 WiFi , with speeds of up to 867 Mbps in 5 GHz , and 300 Mbps in 2.4 GHz , with Gigabit Ethernet ports, and a reasonable price of 29 euros. It is ideal to use the router as a repeater if we do not want to stop using a fiber router from our operator at home to keep the phone.
This router comes with an outdated firmware version by default that has dozens of vulnerabilities. WPS is enabled by default, session tokens are not deleted on the server, credentials and backups are protected with insecure encryption, and the web interface is buggy. Among the failures of the web we find mismatched characters, bad practice in cookies, private IP filtering, weak HTTPS encryption, and susceptibility to clickjacking.

Some of these bugs are patched in the latest version of the router . However, there are two problems: that the routers do not come with that version installed, and that the patches implemented do not completely patch the vulnerabilities. For example, the entire backend of the router is poorly protected, which means that if someone finds an entry point, they can take advantage of all the previous failures.
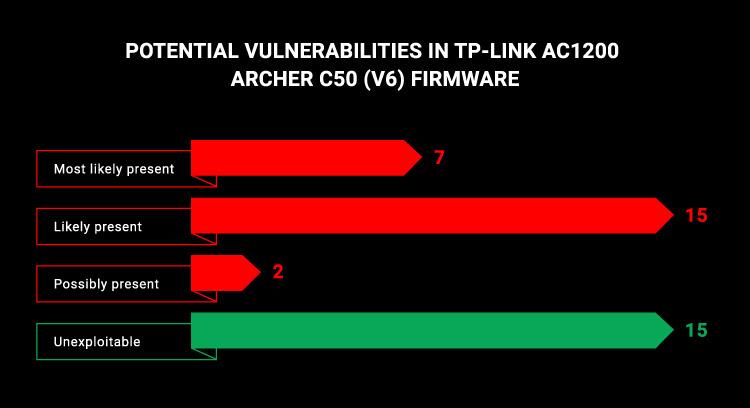
The included firmware has 39 vulnerabilities
In the router’s default firmware, the researchers found 39 known vulnerabilities, listed with their corresponding CVE code. Of these, 24 are likely to be present , and 7 are almost certainly present . Among them we find one of Use-after-free, which allows DDoS attacks against the router, or PPPoL2TP , which allows obtaining privileges on the network by taking advantage of the differences in the data structure between the router sockets. The one of cURL allows to obtain sensitive information and credentials of the own router to take control of the device.
To that we must add all the bugs and vulnerabilities of the web interface , and a critical vulnerability from 2019 that is only partially patched in the firmware by default. With it, a hacker can intercept router traffic and obtain the router’s password, the WPS key to pair with the device, and the network’s SSID.
Cyber News contacted TP-Link on July 18, and the company states that it will urge users to install the firmware update on the router, as well as display an alert on the web interface and in the app. for the device to be updated. However, they have not said that they will include newer firmware in the routers they sell, which is one of the dangers of buying them. Telecommuting has led to hackers attacking more and more vulnerable homes and routers to obtain sensitive information.
The firmware is installed manually , and it is necessary to download it from the official website . To do this, we have to go to this link and follow the instructions. The latest version available is C50 (EU) _V6_210111 from February 4, 2021.