Nowadays, many users wonder what are the tools that hackers use to search for different vulnerabilities in devices that are connected to the Internet. Normally, each one uses specific tools, but there are search engines that are specifically designed for security researchers.
And, although many users think that a “hacker” is a hacker, the reality is quite the opposite, since most are dedicated to investigate and find security flaws so that later, the affected companies and even themselves can Offer a solution in this regard. Several of the tools they use to see the attacks that occur are the following search engines:
Censys
Censys is a payment tool where we can see the attacks that different computer systems and applications are suffering in real time. Censys also has a free domain search engine where you can access and view different information about the domains, such as what ports and protocols they use, and which certificate is valid. In addition, it has a certificate search engine where we can see if it is valid and which key is the last valid one.
It also has an IPv4 address search engine where we can find different relevant information, in addition to the approximate location of the IP address. Finally, one of the very interesting payment options is to be able to see how a security flaw detected has been resolved. If you want more information you can enter the official Censys.io website where you have all the details about this tool.
Shodan
Shodan is a free web service that allows us to see which devices have access to the Internet, and if they have any security flaws. This service is ideal, for example, to see if there are webcams, Smart TV, air conditioning, alarms and other digital home devices connected to the Internet and vulnerable to different types of attacks.
Shodan is one of the most popular and used search engines, since it provides us with a great deal of information, and allows us to see in detail if there is any type of security failure in our device, or what information it has about our public IP address.
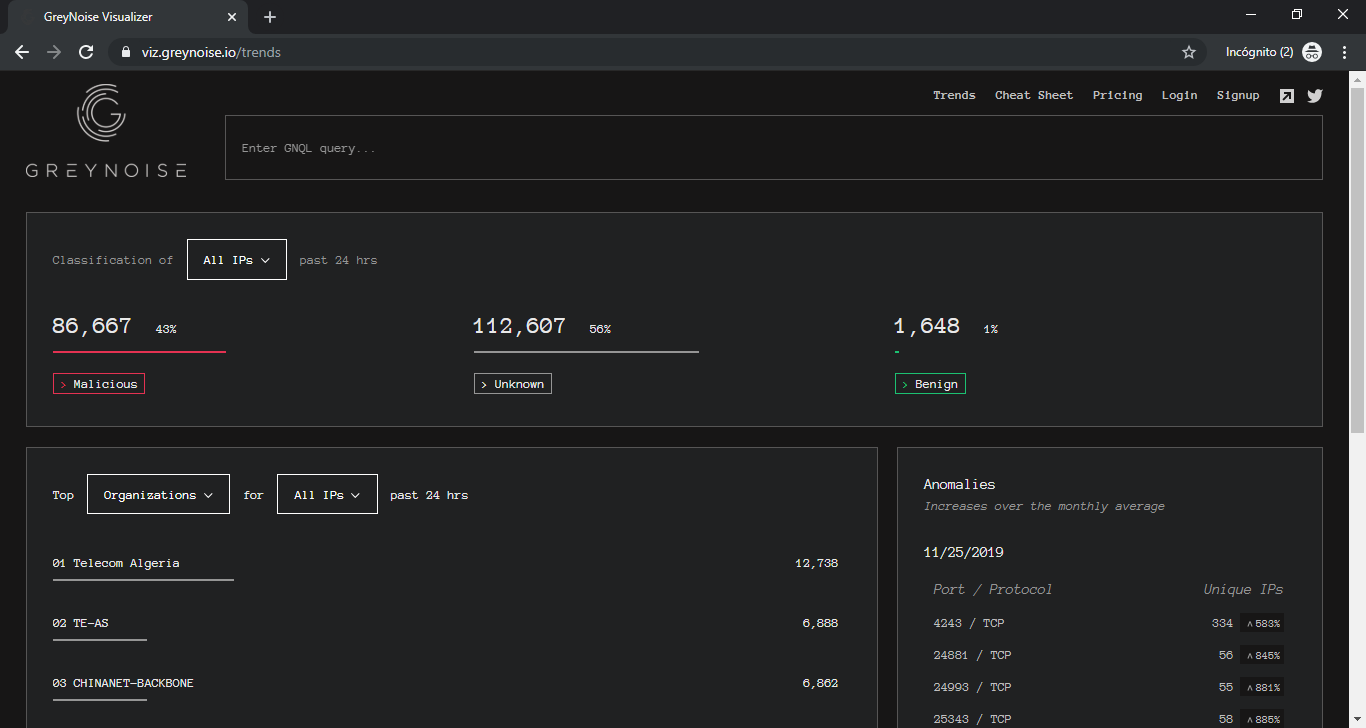
Greynose
Greynose has a search engine where we can enter an IP address and also perform a word search. According to what we have introduced, it will show us information about attacks, malicious websites or bugs that it finds. It also has a section on the lower right side of the search bar, called “explore trends” where we can see different statistics updated in real time, such as anomalies detected in different ports, malicious attacks, etc. To access this functionality you can do it from the following link .
All this is free, but if we want more accurate information such as IP lookup, more advanced queries, or support, we must buy the payment option for companies that is worth $ 2,999 per month.
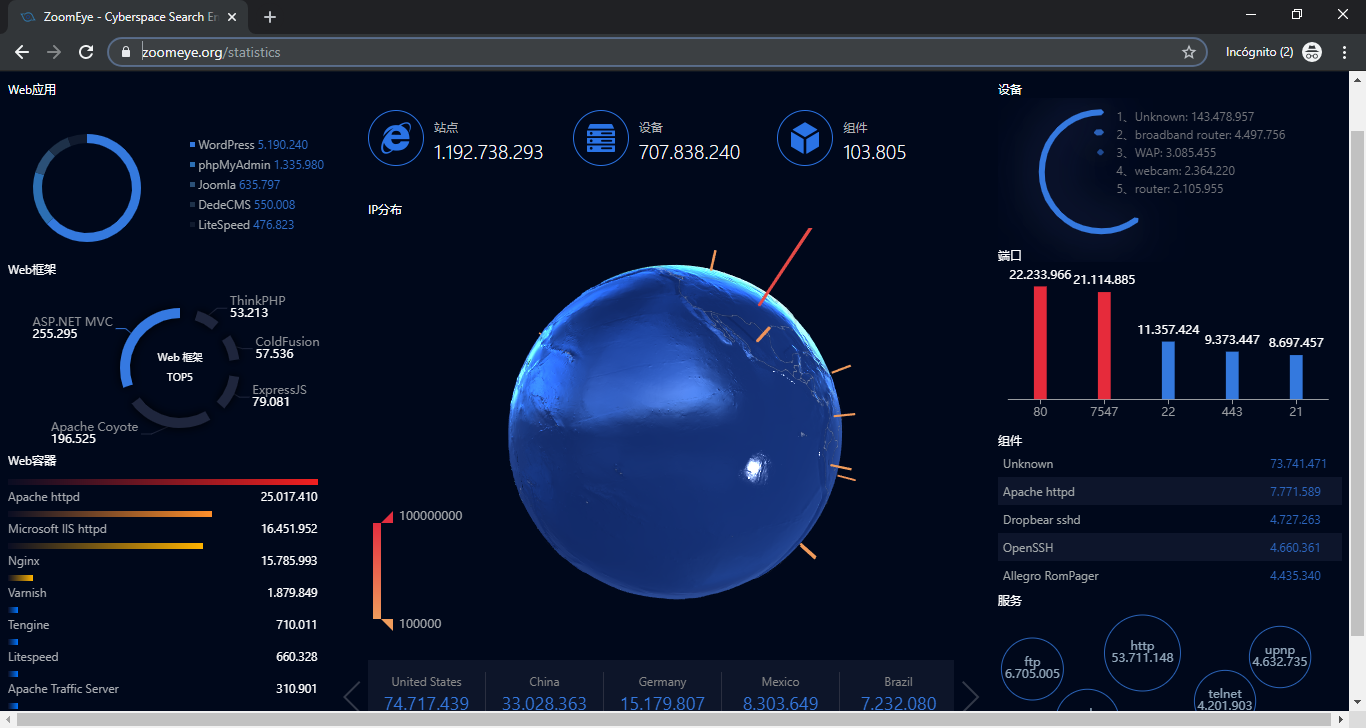
Zoomeye
Zoomeye is very similar to Greynose but is developed for the Chinese market. It has a search engine where entering IP addresses, a word, etc. will show us information about it. Being in Chinese, we recommend that you use it with a translator, since although the information of the results will show it in English, the menus and some data will not.
Zoomeye also has a very interesting section called statistics, where we can see different statistics of the entire planet of all kinds, from countries, browsers, servers, protocols, etc. If you want to access this function you can do it from the following link .
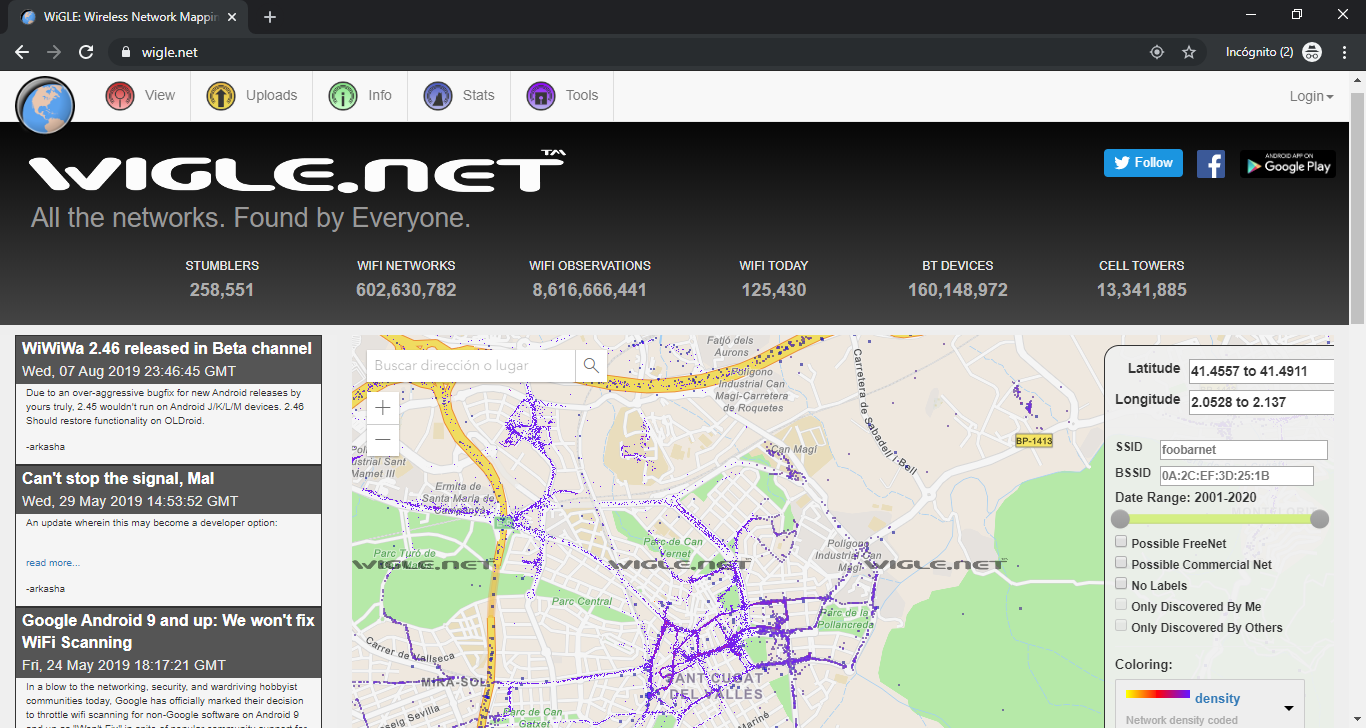
Wigle
Wigle is a search engine for wireless networks by coordinates. That is, when we enter Wigle we find a map, and on the right we can enter latitude and longitude coordinates to go somewhere on planet Earth. If we zoom we can see the different hotspot networks that are available in the place. There are also Wi-Fi devices, Bluetooth, and telecommunications antennas. Of course it can be very useful to see around us and if we have any network available nearby. You can access Wigle in the following link .
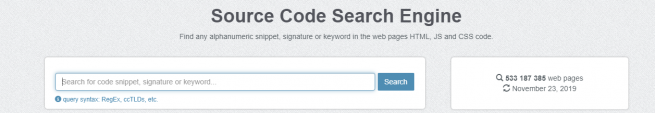
Publicwww
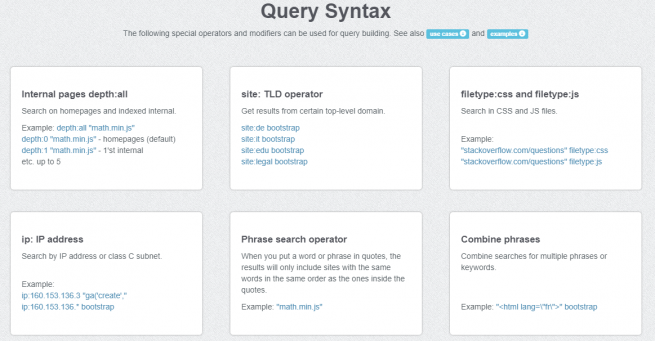
Publicwww is a website that through a search engine allows us to search for HTML, JS and CSS code on any web page. Its use is really very simple, but it can be very useful. The operation of Publicwww is very simple. Once we enter your website, we must enter in the search box, the code we want to find out if it is on any website. Once entered we must right click on the bar where we have entered the code, the “Search” button, and it will show us the results found.
If we want to know what syntax we can enter in the search box, we must click below, where it turns blue “query syntax: RegEx, ccTLDs, etc.” and a new page will open, with the different ways in which we can search the code. We attached some screenshots where you can see examples.
Hunter.io
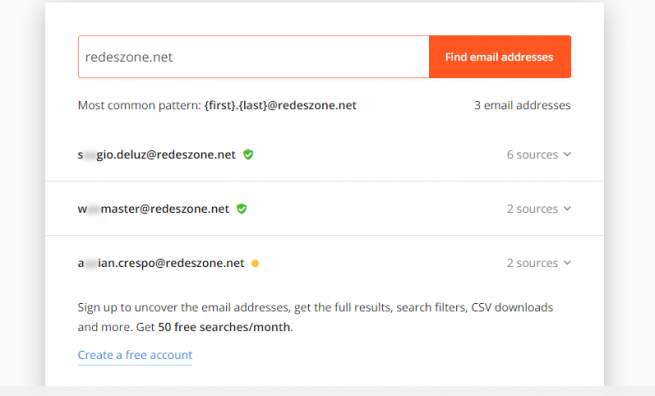
Hunter.io is a website where we have a search engine where we can enter the name of a company, and it will show us all the email addresses that have leaked about that company. This website can be useful if we need to find an email address. The operation of Hunter.io is very simple. Once we enter your website, we must enter in the search box, the name of the company we want to find out if any email address has been leaked. Once entered we must click on the right in the bar where we have entered the email address, the button “Find email addresses” or when we enter the name of the company can appear in the search engine.
Once clicked if you can’t find anything, the message will appear below the following search box “This doesn’t look like a domain name”. However, if you find a result, the email addresses found will appear and next to it a green icon if they are still active or yellow if you do not know. In addition, it will also appear on the right side of each email address found, a down arrow that will indicate on which website you have found the email of the company we are looking for and will indicate if the place where it is still active or not He found it.
Haveibeenpwned
This Haveibeenpwned website allows us to find out if any password on any web page has been leaked by the address of our email. We recommend this website to try it, especially for the leaks and theft of information in recent years. The operation of Haveibeenpwned is very simple. Once we enter your website, we must enter in the search box, the email address we want to find out if the password has been leaked from any website. Once entered we must right click on the bar where we have entered the email address, the “pwned” button.
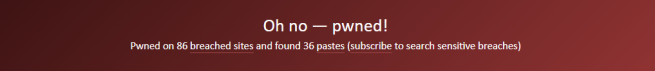
If you do not find that our email address is leaked, the following text will appear below the green and white search bar, “Good news – no pwnage found!”. However, if you find that our email address has been leaked, the following text will appear in red and white, “Oh no – pwned!”.
In the event that it happens to us that this leaking, the first thing we must do is change the email password. Then, on this website if we go down the entire website, it will indicate where you have found that our email address and password have been leaked. This web page can save us from a good problem of improper access, so we recommend that you test your email addresses to see if they have been leaked.
OSINT Framework
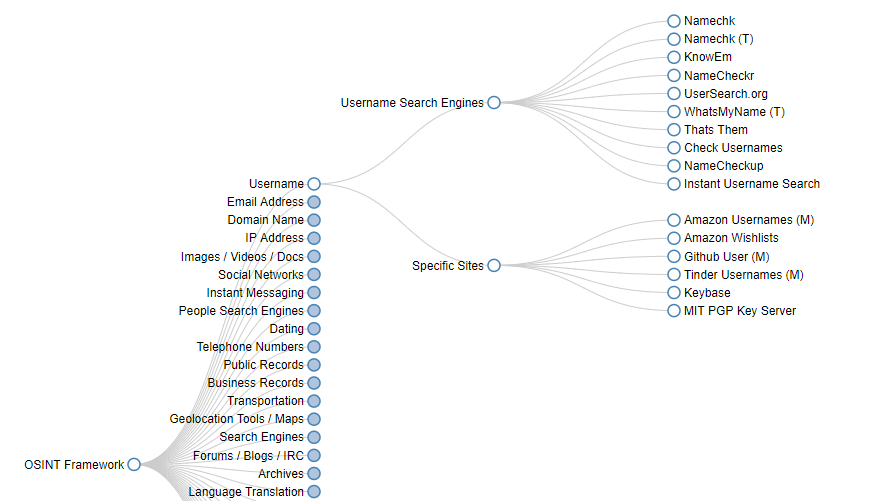
OSINT Framework is a website that through the use of different menus, we can find links to different websites about information about the category we are looking for. When we enter the OSINT Framework website we find on the left side a series of subcategories, which we will see next, where it is about following the different options, according to what we want, and, in the end, it leads us to a series of results, that clicking on them will open a new tab with the search engine that we have selected. We have to take into account that, if we click on the blue ball, another submenu will open, however, if the ball is white, the selected web will be opened.
The different submenus that we can choose are the following:
- Username : Within the “username” section we have other subcategories, such as “username search engines” or “specific sites”. Selecting one of these subcategories allows us to narrow down the available services we have to search for user names.
- Email Address : Within the “email address” section we can choose between the different subcategories “email search”, “common emails formats”, “email verification”, “vreach data”, “spam reputation lists” and “mail blacklist”. Selecting one of these subcategories allows us to narrow down the available services we have to search for email addresses.
- Domain Name : Within the “domain name” section we can choose between the different subcategories “whois records”, “subdomains”, “Discovery”, “certificate search”, “passiveDNS”, “reputation”, “domain blacklists”, “typosquatting” , “Analytics”, “url expanders”, “change detection”, “social anaysis”, “DNSSEC”, “cloud resources”, “vulnerabilities” and “tools”. Selecting one of these subcategories allows us to narrow down the available services we have to find any data on domain names.
- IP Address : Within the “IP address” section we can choose between the different subcategories “geolocation”, “host / port discovery”, “IPV4”, “IPV6”, “BGP”, “reputation”, “blacklists”, “neighbor domains ”,“ Protect by cloud services ”,“ Wireless network info ”,“ network analysis tools ”and“ IP loggers ”. Selecting one of these subcategories allows us to narrow down the available services we have to find any data about IP addresses.
- Images / Videos / Docs : Within the section “images, videos and docs” we can choose between the different subcategories “images”, “videos”, “webcams”, “documents” and “fonts”. Selecting one of these subcategories allows us to narrow down the available services we have to find any data on the above mentioned files.
- Social Networks : Within the “social networks” section we can choose between the different subcategories “Facebook”, “Twitter”, “Reddit”, “LinkedIn”, “other social networks”, “search” and “social media monitoring wiki”. Selecting one of these subcategories allows us to narrow down the available services we have to find any data on the selected social networks.
- Instant Messaging : Within the “instant messaging” section we can choose between the different subcategories “Skype”, “Snapchat”, “KiK” and “Yikyak”. Selecting one of these subcategories allows us to narrow down the available services we have to find any data on the selected instant messaging networks.
- People Search Engines : Within the “people search engines” section we can choose between the two different subcategories “general people search” and “registries”. Selecting one of these subcategories allows us to narrow down the available services we have to find any data on the selected category.
- Dating : Within the “dating” section we can choose between the different subcategories “match.com”, “ayi.com”, “plenty of fish.com”, “eharmony”, “farmers only”, “zoosk”, “okcupid” , “Tinder”, “wamba.com”, “adultfriendfinder”, “Ashley madison”, “beautifulpeople.com”, “badoo”, “spark.com”, “meetup”, “blackpeoplemeet” and “review of users”. Selecting one of these subcategories allows us to narrow down or enter the selected website or service.
- Telephone Numbers : Within the “telephone numbers” section we can choose between the different subcategories “voicemail”, “international”, “pipl api”, “whocalld”, “411”, “callerid test”, “thatsthem – reverse puts lookup”, “Twilio lookup”, “fonde finder”, “true caller”, “reverse genie”, “spydialer”, “puts validator”, “free Carrier lookup”, “mr. number ”,“ calleridservice.com ”,“ next caller ”,“ data24-7 ”,“ hlr lookup portal ”,“ opencnam ”,“ opencnam api ”,“ usphonebook ”,“ numspy ”and“ numspy-api ”. Selecting one of these subcategories allows us to narrow down the available services we have to find any data on phone numbers.
- Public Record : Within the “public records” section we can choose between the different subcategories “property records”, “court / criminal records”, “gonvernment records”, “financial / tax resources”, “birth records”, “death records”, “Us country data”, “voter records”, “patent records”, “political records”, “public records”, “enigma”, “the world bank open data catalog”, “brb public records”, “govdata (german) ”And“ open.data-portal München ”. Selecting one of these subcategories allows us to narrow down the available services that we have to search for any public data, it is mainly focused on the USA, although we have some options for other countries such as Germany.
- Business Records : Within the “business records” section we can choose between the different subcategories “annual reports”, “general info & news”, “company profiles”, “employee profiles & resumes” and “additional resources”. Selecting one of these subcategories allows us to limit information about and for companies.
- Transportation : Within the “transportation” section we can choose between the different subcategories “vehicle records”, “air traffic records”, “marine records”, “railway records”, “satellite tracking” and “track-trace”. Selecting one of these subcategories allows us to limit information on different categories and methods of transport.
- Geolocation Tools / Maps : Within the “geolocation tools / maps” section we can choose between the different subcategories “geolocation tools”, “coordinates”, “map reporting tools”, “mobile coverage”, “Google maps”, “Bing maps”, “HERE maps”, “dual maps”, “instant Google Street view”, “wikimapia”, “openstreetmap”, “flash earth”, “historic aerials”, “Google maps update alerts”, “Google earth overlays”, “yandex .maps ”,“ terraserver ”,“ Google earth ”,“ Baidu maps ”,“ corona ”,“ daum ”,“ naver ”,“ earthexplorer ”,“ openstreetcam ”,“ dronetheworld ”,“ travel by drone ”,“ hivemapper ”,“ Landsatlook viewer ”,“ sentinel2look viewer ”,“ nexrad data inventory search ”,“ mapquest ”,“ openrailwaymap ”,“ openstreetmap routing service ”,“ hiking & biking map ”,“ us nav guide zip code data ”and“ wayback imagery ”. Selecting one of these subcategories allows us to limit information on different categories and geolocation services.
- Search Engines : Within the “search engines” section we can choose between the different subcategories “general search”, “meta search”, code search “,” FTP search “, academic / publication search”, “news search”, “other search” , “Search tools”, “search engine guides” and “fact checking”. Selecting one of these subcategories allows us to limit information from different categories and on different search methods.
- Forums / Blogs / IRC : Within the “forums / blogs / IRC” section we can choose between the different subcategories “forum search engines”, “blog search engines” and “IRC search”. Selecting one of these subcategories allows us to narrow down and select a service that performs a search on forums, blogs or IRC.
- Archives : Within the “archives” section we can choose between the different subcategories “web”, “data leaks”, “public datasets” and “other media”. Selecting one of these subcategories allows us to narrow down and select a service that performs a file search.
- Language Translation : Within the “language translations” section we can choose between the different subcategories “text”, “pictures” and “analysis”. Selecting one of these subcategories allows us to narrow down and select a translation service.
- Metadata : Within the “metadata” section we can choose between the different subcategories “exiftool”, “metagoofil”, “seal” and “codetwo Outlook export”. Selecting one of these subcategories allows us to narrow down and select a service that performs a metadata search.
- Mobile Emulation : Within the “mobile emulation” section we can only choose the “Android” subcategory, where within the “Android” category we are given the “emulation tools” and “apps” subcategories. Selecting one of these subcategories allows us to narrow down and select an Android emulation service.
- Terrorism : Within the “terrorism” section we can only choose the subcategory “Global Terrorism Database”. Selecting this category allows us to access a database on terrorism.
- Dark Web : Within the “dark web” section we can choose between the different subcategories “general info”, “clients”, “discovery”, “TOR search”, “TOR directories”, “TOR2web”, “web or proxy” and ” IACA dark web investigation support ”. Selecting one of these subcategories allows us to narrow down and select a service or information about the dark web.
- Digital Currency : Within the “digital currency” section we can choose between the different subcategories “bitcoin”, “Ethereum” and “monero”. Selecting one of these subcategories allows us to access different services and websites on the selected digital currency.
- Classifieds : Within the “classifieds” section we can choose between the different subcategories “craigslist”, “kijiji”, “quikr”, “ebay”, “offerup”, “goofbid”, “flippity”, “searchalljunk”, “totalcraigsearch”, “Backpage”, “search tempest”, “oodley” and “claz.org”. Selecting one of these subcategories allows us to access different classification services.
- Enconding / Decoding : Within the section “enconding / decoding” we can choose between the different subcategories “base64”, “barcodes / QR”, “javascript”, “PHP”, “XOR”, “cyberchef” and “functions online”. Selecting one of these subcategories allows us to access different services and programming websites.
- Tools : Within the “tools” section we can choose between the different subcategories “osint automation”, “pentesting recon”, “virtual machines”, “paterva / maltego”, “epic privacy browser” and “overview”. Selecting one of these subcategories allows us to access different tools.
- Malicious File Analysis : Within the “malicious file analysis” section we can choose between the different subcategories “search”, “hosted automated analysis”, “office files”, “PDFs”, “pcaps”, “ghidra” and “malware analysis tools” . Selecting one of these subcategories allows us to access different analysis tools on malicious files.
- Exploits & Advisories : Within the “exploits & advisories” section we can choose between the different subcategories “default passwords”, “miter att & ck”, “exploit DB”, “packet storm”, “securityfocus”, “nvd – nist”, “osvdb ”,“ Cve details ”,“ cve miter ”,“ owasp ”,“ 0day.today ”,“ secunia ”and“ Canadian center for cyber security ”. Selecting one of these subcategories allows us to access different tools and websites for analysis on exploits.
- Threat Intelligence : Within the “threat intelligence” section we can choose between the different subcategories “phishing”, “ioc tools”, “ttps”, “ibm x-force exchange”, “malware information sharing platform”, “malware patrol”, ” project honey pot ”,“ cymon open threat intelligence ”,“ mlsecproject / combine ”,“ hostintel – keithjjones github ”,“ massive-octo-spice – csirgadgets github ”,“ bot scout ”,“ blueliv threat exchange ”,“ aptnotes ” , “Honeydb”, “pulsedive” and “Mr. looquer ioc feed – 1st dual stack threat feed”. Selecting one of these subcategories allows us to access different information websites.
- OpSec : Within the “opsec” section we can choose between the different subcategories “persona creation”, “anonymous browsing”, “privacy / clean up” and “metada / style”. Selecting one of these subcategories allows us to access different opsec tools and websites.
- Documentation : Within the “documentation” section we can choose between the different subcategories “web browsing”, “screen capture”, “map locations” and “timeline js3”. Selecting one of these subcategories allows us to access different documentation.
- Training : Within the “training” section we can choose between the different subcategories “games”, “automatingosint.com”, “open source Intelligence techniques”, “plessas”, “sans sec487 osint class”, “netbootcamp”, and “smart questions ” Selecting one of these subcategories allows us to access different training websites on the selected topic.
As you can see OSINT Framework, it would be more Wikipedia style, for the amount of menus and categories it offers, to be able to find almost any category of what we are looking for. We definitely recommend you to try it.