The Covid-19 pandemic, in addition to accelerating the shift to a more digital world, has also changed our workplace. In this last period of time, the idea has grown that commuting every day to work in the office feels more and more like an outdated approach. Here we are going to explain how to progress towards remote work step by step, in a trend that is becoming increasingly appreciated in the vast majority of companies where work is done with computers.
The resistance of companies to telework
Quite a few companies were not convinced by the idea of remote work, and were somewhat afraid that their employees’ productivity would be reduced. Organizations in all industries, due to the pandemic, were forced to move towards remote work. The positive surprise is that they have been surprised by the good productivity of their workers.

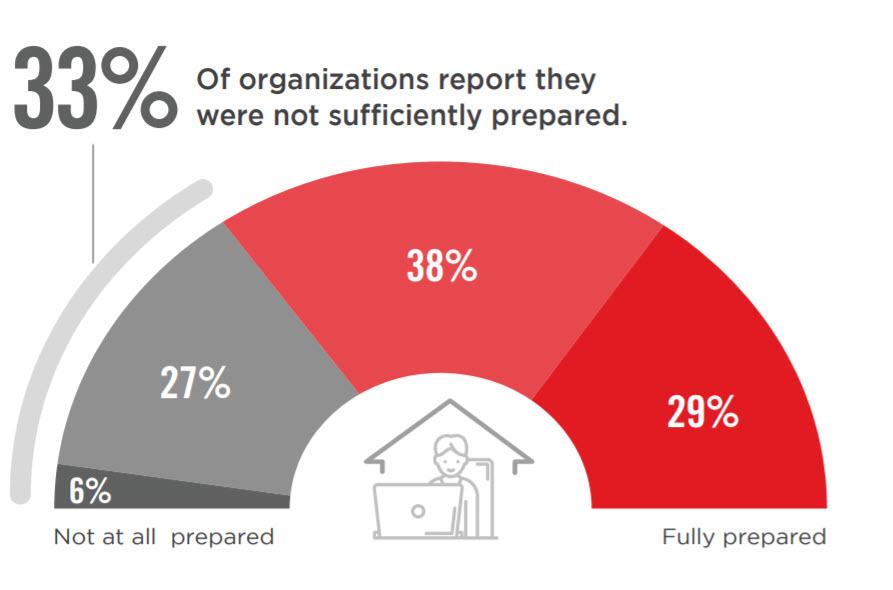
However, not everything has been positive for the business sector, especially in terms of security. In a bitglass report on remote workforce security, 33% of organizations were unprepared to do remote work safely early in the pandemic.
What IT teams need to do to fix it is implement a zero-trust security strategy. This implies that all workers are duly authenticated before access to corporate systems and data is granted.
Ensuring a zero trust strategy for teleworking
One of the most important challenges that companies have faced in moving towards remote work has been to find a solution to protect workers’ personal equipment. Thus, keeping these devices safe for 43% of companies has been a significant challenge.
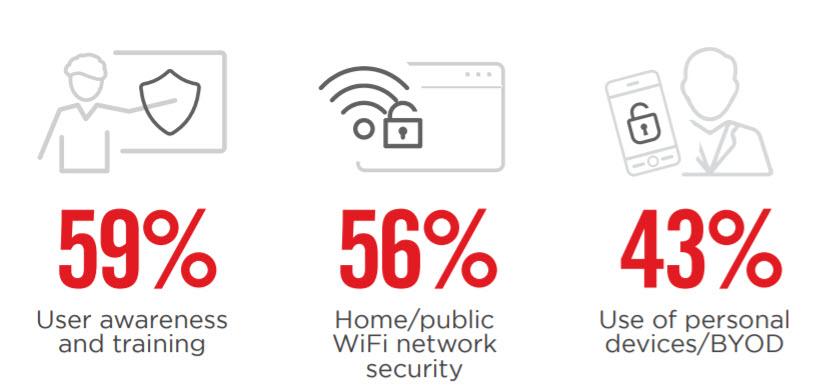
Another important issue with 56%, has been the challenge of security in the home WiFi network and when we use a public WiFi. To this we have to add the effort that user awareness and training have meant for 59% of companies. Businesses should consider a solution that offers the following capabilities to protect their data and remote workers with:
- A data loss prevention that uses watermarks, encryption, access control, redaction and blocking of critical content. The goal to achieve is that employees continue to get the access they need, without being subject to undue risk.
- Identity and Access Management (IAM) . Cybercriminals are trying to install malware on corporate networks and carry out phishing attacks on telecommuters. With an IAM or Identity and Access Management System, companies can use controls such as single sign-on (SSO) and multi-factor authentication (MFA).
- The problem of visibility to keep records of access of remote workers. 33% of companies think that lack of visibility is a problem to allow teleworking.
- The protection of remote workers , who as they work outside the corporate network are more exposed to the risks of data theft and malware. In that sense, we must protect all those workers who work from outside their homes.
Protection of the public cloud, access to the web and internal applications
In a digital age where we are moving towards remote work, we must start by securing our public cloud. Today’s public cloud uses many applications like Slack, Office 365, and more. Although it is true that each cloud application provider protects its own infrastructure, we must not forget that the companies that use each application are responsible for safeguarding and protecting the data of each application. In this sense, what is needed is to implement single sign-on and multi-factor authentication in public cloud applications.
Access to the Internet poses risks for workers and their employers, such as malware and data leakage. Traditional VPN approaches are often sought to protect access to the web. The problem is, VPNs aren’t enough for a large number of remote users. To solve this problem, companies need to use secure web gateway solutions on one device that can easily scale with the number of users.
Additionally, to protect internal applications, a Zero Trust Network Access (ZTNA) solution requires access to corporate resources to be contextually parsed based on user, group, application, location, device type, and more. We should also not forget about real-time protections, Data Loss Prevention (DLP), and Advanced Threat Protection (ATP) that can help protect against threats that arise when users access specific applications.
Finally, from this article we recommend you read the tutorial on the best tools for remote work .