Signal is currently the most secure messaging application on the market. It has end-to-end encryption , and increasingly includes more functionalities from other apps such as WhatsApp. WhatsApp co-founder Brian Acton himself invested in it. However, the company detected that there was a tool that promised to be able to hack the app, and instead they have been the ones who have hacked the tool.
The tool is the one used by the company Cellebrite , which creates software to automatically extract data from mobile phones . Although they say that they only sell their services to governments and national security agencies, the truth is that they do business with authoritarian regimes such as Venezuela, Russia, China or Belarus, and even paramilitary groups in countries like Myanmar. Among the uses is spying on journalists and activists around the world.

A few months ago, the company announced that they had added Signal to their tool , and they published a somewhat confusing post about how they could read messages from a mobile phone while having physical access to it. They later deleted the post, and then replaced it with an even more confusing summary. However, the headlines that they had managed to hack Signal stayed in the media, despite the fact that they have not broken either the encryption or any protection method of the app. Everything was basically a lie.
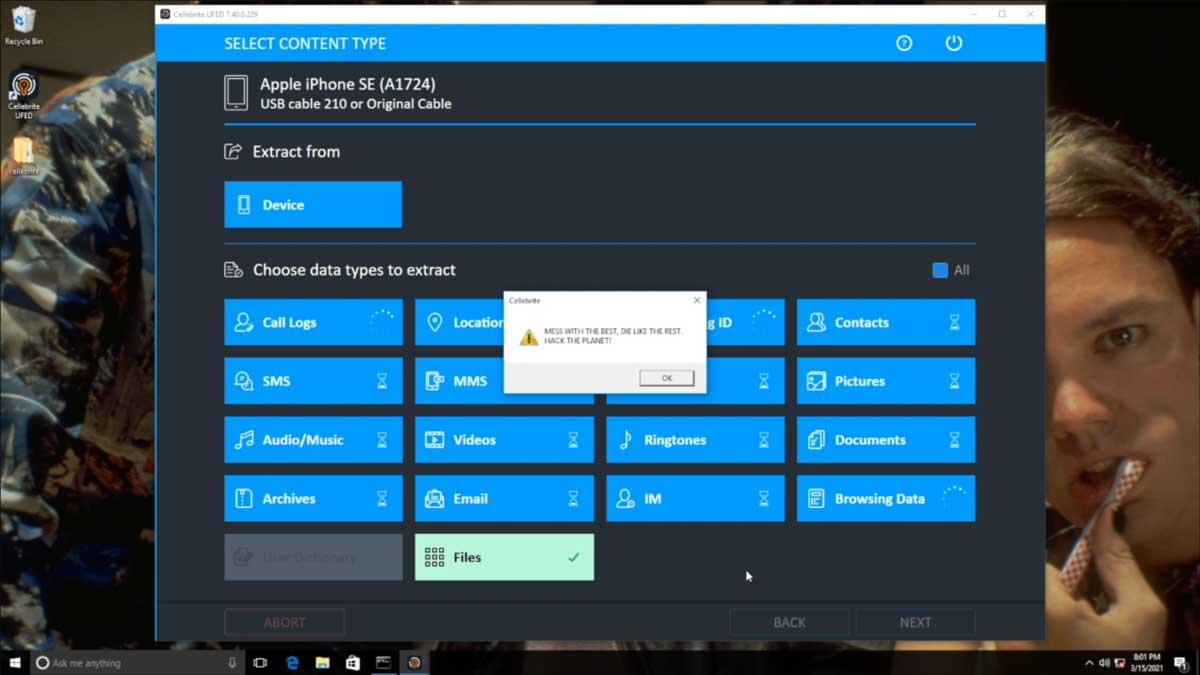
UFED and Physical Analyzer: the two Cellebrite programs
However, Signal did not stop there, and they decided to fight back. To do this, they analyzed the tools, which to begin with require that someone have physical access to your mobile. The company does not offer data interception or remote surveillance services. To hack the devices they have two software tools: UFED and Physical Analyzer.
UFED creates a device backup on Windows using the adb backup command on Android and iTunes on iPhone. Once the backup is obtained, it is processed with Physical Analyzer to be able to search them comfortably. When Cellebrite said that they already supported Signal, it meant that they could display data extracted from an unlocked device in the second program.
This can be done with any app if they manage to unlock the device , so with this method they can spy on WhatsApp, Telegram, Facebook, your SMS, your photos, etc. Basically, the tool automates data collection instead of having to export WhatsApp chats or taking screenshots by hand.
By chance, Signal claims that, walking down the street, a small package “fell” out of a “van,” and coincidentally was a Cellebrite hacking kit , with the latest versions of hardware and software, plus a multitude of adapters for mobiles. Software, which looks for ways to corrupt device memory or exploit other vulnerabilities, should be protected against attacks. But it is not, giving rise to many avenues of exploitation.

Thus, Signal has managed to execute arbitrary code on one of Cellebrite’s machines simply by including a file with a special but innocuous format on a device that is being hacked with Cellebrite. With this, there are no limits to the type of code they can execute.
With this, they can modify the files created in a scan, and those that are scanned in the future, inserting texts, photos, contacts, files or any other data. With this, the veracity of the data obtained with these tools is called into question, since they can be modified to make them appear legitimate, so there may be alteration of tests.
Signal says they will give details of how the vulnerability works to Cellebrite if the company communicates current and future vulnerabilities they use to hack devices to affected companies, which they probably won’t do because they would be out of business.