The world of cybercrime never rests and they are always looking for new strategies with which to obtain benefits. Cybercriminals no longer act alone and sometimes work in groups, which makes them more dangerous. On this occasion, we are going to talk about ransomware attacks, and if we should rescue the data by paying cybercriminals. We will know all the dangers, and how we can avoid paying for the data ransom.
What is ransomware and what consequences does it have
When we suffer a ransomware attack, the malware is responsible for encrypting all our data on the PC where it has been run, and it is also possible that all data shared on the local network is encrypted, therefore, we must not only protect our computer , but all the teams in the company and properly check the write permissions that they have.
If we want to return to normality, we must erase and restore the servers and PCs using our backup copies, if we have applied a good backup policy. The other option is to use a decryption key to be able to unlock files and data. The downside is that, to obtain that decryption key, in the vast majority of cases we have to pay a ransom to cybercriminals.

Ransomware causes a huge negative impact that disrupts business operations, and can also cause permanent data loss. The causes that it causes to the company are: downtime, loss of productivity, income and reputation. But that’s not all, also your confidential business information can be destroyed or publicly disclosed.
Evolution of ransomware attacks
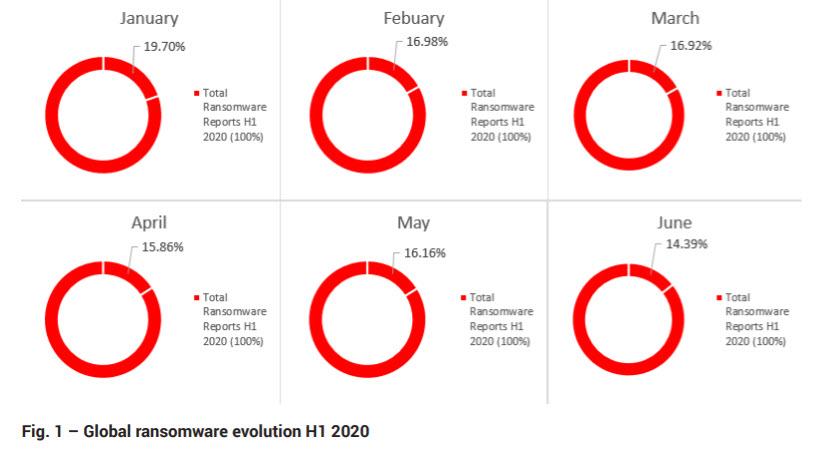
Ransomware attacks in the first 6 months of this year 2020 have increased at a dizzying rate . According to mid-year report of Bitdefender 2020 , the number of global reports ransomware increased by 715% yoy. If we rank by the number of attacks received, the United States ranks first, followed by the United Kingdom. This is a graph of the ransomware worldwide:
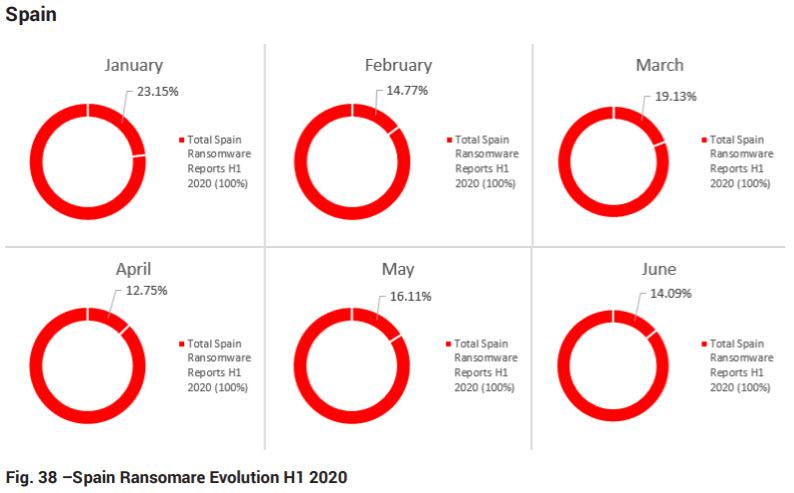
In Spain, also during the first half of 2020, ransomware attacks have been increasing, as you can see here:
Another thing to keep in mind is that a ransomware attack is rarely targeted. In this sense, 99% of them do not stalk their victims or make a deep examination. Their tactic is to send e-mails indiscriminately and then wait to see who they have hit.
Pay the ransom or restore data from backups
As we have already mentioned before, cybercriminals seek to collect a ransom, and if we pay it, then they will give us the key. This ransom is normally paid in cryptocurrencies such as Bitcoin, although the attackers could stipulate another. Despite the fact that working with Bitcoin is relatively simple, it can take days to get everything ready. In addition, during that period you will not be able to operate normally on the infected system, or at least, you will do so in a very limited way.
In the case of paying the ransom, there is no guarantee of data recovery. Sometimes ransomware decryption doesn’t work, or you lose some of your data. Even if your files are decrypted well, it is also likely that you are still infected by malware, Trojans, and keyloggers. Therefore, our system will not be clean and unreliable after the decryption process is finished.
To summarize, we are going to give you a series of negative points for which paying the ransomware ransom is not a good idea :
- You are helping cybercriminals with their extortion business.
- Nobody guarantees that the decryption key works, first you pay, and then they may not send you anything or it may not work.
- Cybercriminals could have introduced additional malware, to infect you after a while, and you have to pay again (because you have already paid once).
- It will always be cheaper to have a good backup policy, and not have to pay cybercriminals.
Restoring from backups, even if it takes longer, may be the solution. However, it is only possible if we have:
- A robust backup procedure, ideally with the 3-2-1 backup scheme.
- The established procedure has been followed.
- Backups have been tested in drills and simulated incidents.
However, the cybercriminals behind ransomware also have ways to ensure that our backups are infected as well. For this reason, companies need to plan and safeguard their backups in a way that guarantees their integrity when we have to use them.
Prevention and staff awareness
Preventing ransomware attacks involves having an incident response plan. In the same way that, for example, we have home or other insurance, we hope not to have to use it, but in the event of a misfortune we are covered. Another important element is the awareness of the workers of a company to avoid a ransomware attack. Most infections of this type are due to an employee falling for a phishing attack.

In this sense, the staff of a company must have training in cybersecurity awareness, in this way, they can identify phishing emails, other scams and threats of various kinds. One way to reduce risks is to try to reduce internal email, so it will be easier to focus and pay attention to external email that are the ones that carry danger. Some applications like Slack could contribute to this reduction of internal emails.
Furthermore, employees should be prepared by taking security awareness courses. In addition, if we hire a private company that tests workers with a surprise phishing campaign, it can add a security bonus. It does not pose any risk, and so we check if they have learned to act correctly.
How to improve security in our company
An important element is the application of the principle of least privilege . Here we must ensure that employees have the minimum access rights to perform the functions defined by their role. They should not be able to access functions that do not correspond to them, thus, if their account is compromised, as their functions are more limited, it is less dangerous. In this sense, it is necessary to adequately limit the people who have access to an administrator account.
A good configuration of the spam filter can also help, thus, by reducing the volume of spam, it will allow us to spend more time looking for anomalies in the emails we receive.
We must also have a good antivirus and antimalware that must be updated every day. In addition, the operating system and the programs we use must be up to date with the latest security patches. To this we must also add that our network equipment has the latest available firmware installed to avoid security breaches.
Regarding the network topology, it is best to work with sections segmented into VLANs and with access controls. In case of problems, if a segment is infected, it is easier to solve, and mitigate the impact, than a network where we have all the equipment connected.
Good backup policy
In a ransomware attack, one of the things that will allow us to emerge triumphant from the attack is to have a good backup policy . This should be based on:
- We should have three copies of our data: the live system, plus two backups.
- Those two backups must be on different media.
- One of those backups must be done off-site.
The regularity with which we make these backups will determine the information that we can lose, therefore, it is highly recommended to make daily backups, and for critical systems, it is essential to make hourly backups.

Also, a very important detail is that the backup copies must be encrypted . However, none of this will help if cybercriminals manage to infect your backups. The ransomware is set to take a while before it activates so your copies could be infected. If we want to combat this, we can use immutable backups . These are backups that cannot be written to once made. This means that they cannot be infected by ransomware or any other type of malware. The problem you have is that it is expensive, but it could save your business.
Report and have an incident response plan
If we want to guarantee a coordinated and efficient response to a ransomware attack, we must have an incident response plan . This plan must include the following phases:
- Preparation . Fine-tuning what has been mentioned in this tutorial is a good place to start. Also, rehearsing the plan with simulated incidents and seeing how an attacker could attack our company can be a good starting point.
- Identification Identify as soon as possible what is happening, who and what is infected, what is the extent of the problem, and if data has been leaked.
- Containment We must prevent the infection from spreading and quarantine the infected systems.
- Eradication We have to make sure that malicious software has been removed from all compromised computers.
- Recovery . Here we must restore data from immutable backups if we have them. Otherwise, we must check that the backups are free of malware before restoring them.
- Final analysis . Once we have solved the problem, we must find out how the infection occurred and what could have stopped it. It would also be necessary to discern whether it was the consequence of an exploited vulnerability, or of human error. Finally, take measures so that it does not happen again.
When we suffer a ransomware attack we must report it, since it is a crime. Also, you may have to report the incident to your regional or national data protection authority. Finally, remember that paying the ransom is usually not the best option because your system could still be infected after decryption.