The router is undoubtedly a fundamental piece for our connections. That is why when a vulnerability arises, a failure that may compromise our security or privacy, we must try to correct it as soon as possible. In this article we echo a news story that reports on how a TP-Link router has been hacked again and thus putting users at risk.
Security issues with the TP-Link AC1750 router
Specifically, this problem that we mentioned affects the TP-Link AC1750 (Archer C7) router . It is one of the most popular and sold of the company. As with many modern routers, this model has a USB port to connect other equipment, such as printers or memories to modify the firmware or share content on the network.

It is precisely that USB port that has caused the problem. When a USB drive is connected, the router activates an SMB share, enables FTP, and powers up a DLNA media server. The contents of the unit can be accessed using these protocols.
A security researcher has tested to see what could happen to a malicious flash drive . It found a vulnerability that can be exploited to read pre-authentication from the router’s file system. This would allow the stealing of the login credentials. It is possible through symbolic links.
Keep in mind that the TP-Link AC1750 router runs OpenWRT . This means that symbolic links can point to files normally present on Linux-based machines. The malicious USB drive must be formatted with an NTFS partition and the content will later be accessible over the network.
Now this security researcher has found that by default, symbolic links are not removed from the reference if accessed via SMB or FTP. However, symbolic links will be followed if accessed via DLNA. The interesting thing is that only multimedia file types will be served. This requirement can be achieved by naming the symbolic link with a multimedia extension, such as .wav. For example, a symbolic link to / etc / shadow would be called shadow.wav.
An important point made by the security researcher is that the plain text password for the administrative web interface is stored in / etc / config / usbshare by default. With this password, we could change the router’s configuration options.
The researcher created three symbolic links to test his theory. After plugging in the flash drive he was able to access the files via DLNA using a client like VLC. We can see the image it shows on Medium .
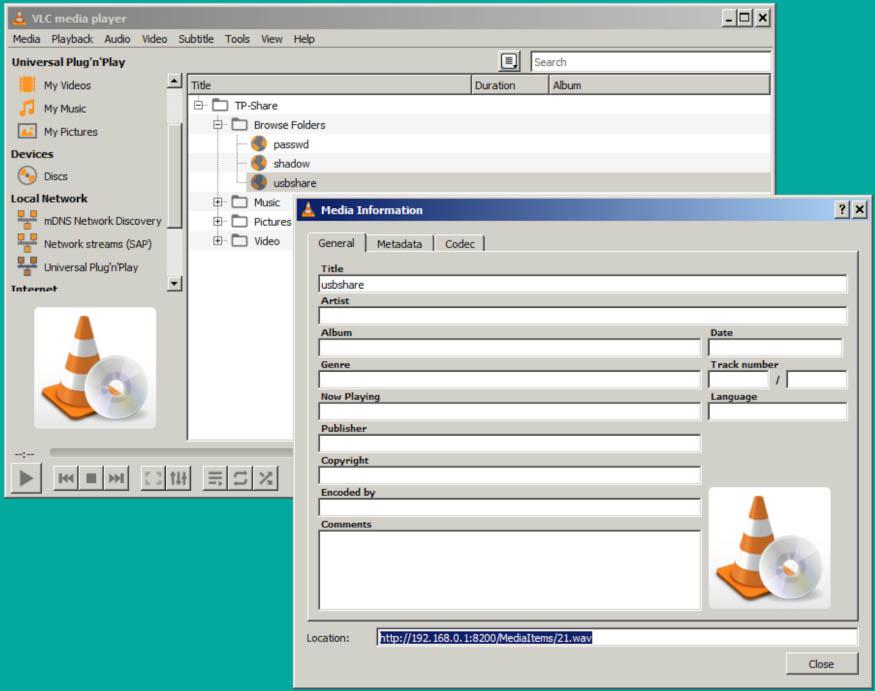
Here we can see how “usbshare” can be accessed via HTTP at http://192.168.0.1:8200/MediaItems/21.wav. The content of this file can be downloaded using the link.
When you acquire the necessary credentials, you will be able to access the web interface and access the file system.
The attack needs physical access
As we can see, this attack will require physical access to the device . It is not a scenario that we can consider as ordinary. However, it could happen in a work environment or if we invite someone to our house and they want to try our router. Also that person could have the password to access.
In case someone attacked the router with this method, they could, among other things, create a VPN for their web traffic to pass through this hacked device.
The vulnerability has been registered as CVE-2020-5795 . At the time of writing this article, TP-Link has already released a patch to correct the security flaw. It is important that users always have the latest versions available. In this case we can download it from the official website .
We leave you a tutorial on how to audit a router with Routersploit.