Every day cybercriminals try to hack into our Gmail accounts in order to make a profit and steal our digital identity. In this complete tutorial, we are going to explain in detail how to protect your Google account to make it very difficult for these cybercriminals and not to be hacked. To avoid this, we can use a secure password, two-step verification and other recommendations that we tell you below.
The importance of having our Google account protected
In the last five years, the way of working and receiving correspondence and information has changed a lot. Right now it is becoming more and more a trend to work in the cloud. Therefore, sharing an Excel sheet with co-workers is becoming more and more common. It is also normal to have shared folders and private company documentation. A safety failure of a worker can put an entire company at risk, as has happened with the “big ones”, where the weakest link was the worker.

Also, not everything has to do with the workplace. It also affects our private and personal lives. With the arrival of the digital age, one of the things that has happened is that a large part of the correspondence on paper has disappeared. Obviously, this is due to ecological reasons that will benefit our planet in the future. However, periodically, we receive information from our bank and on some occasions we receive or request documentation from it. For example, we deposit money or make a transfer at an ATM and ask to receive a receipt by e-mail. Also another common thing can be to have your invoices saved in Google Drive.
Last but not least, there are private emails with family and friends that we want to keep safe too. In short, looking at the current panorama, we seek to protect your Google account from being hacked, since the vast majority of users use Google’s popular Gmail service.
First line of defense: use a strong password
Our first barrier against cybercriminals is having a strong password . When cybercriminals manage to attack a Google account, it is usually because a password is not very secure or has been previously stolen in a service where we also use exactly the same password. In this article we have made a complete tutorial on how to create a strong password , something essential to protect our identities online.
As a summary, if we want to build a good password it must contain:
- Capital letters.
- Lowercase.
- Numbers.
- Symbols.
- The recommended length would be a minimum of 12 characters.
Another factor that we must also take into account is that we must change our passwords periodically . For example, if you suspect that your password has been stolen, or you have had to use it on a public computer, this is a good time to change it.
When preparing our new password we also have to follow a series of recommendations:
- Do not use the same password for everything.
- Avoid using the date of birth, and other public events easy to find out.
- Do not leave it on a post-it attached to a monitor
- Do not write it down on a paper that we always carry with us
- Do not save it in a file without a password on the desktop of our PC.
A password generator that we could use if we don’t dare to create a password ourselves is to use the LastPass password generator . Once we have created that password by ourselves or through a website, it is time to change it.
The first thing we have to do is access our Google Account . If you have not logged in, you will have to enter the password. Once inside we will go to the Security section. We are going to ” Sign in to Google, Password” and there it asks us to re-enter it. Next, a Change Password screen appears .
To finish with this section, it should be noted that Google allows us to check all the passwords that we have synchronized in Google Chrome. If you click on the previous link, it will show us if there has been any leak and if they have been exposed. In addition, it will tell us if our passwords are not secure and if it is convenient to change them.
How Google’s 2-Step Verification Works
Two-step verification will protect us from malicious users even if they have our password. It is about adding an additional defense to your Google account to avoid being hacked. When someone steals our password, they could block your access to our account. In addition, it could delete all your content, impersonate our identity and use the account to reset the passwords of other accounts that we are using.
Here’s a video that talks about Google’s 2-Step Verification:
If we activate it, the process to log into our account will be somewhat different. First of all, every time we log into Google, we must enter our password. In this sense, it will not have changed much, the difference is that one more step has been added.
The second thing that will happen is that a code will be sent to our phone through a message, a voice call or our mobile application. In this way, if someone tries to enter our account, as they do not have that data, they will not be able to access.
It also allows, if you need it, not to use two-step verification on a specific PC. From that moment on, when you log in from the “trusted” computer, it will only ask for the password. However, when we log into our account with another computer, we must use two-step verification.
It can be said that thanks to this new security procedure we have added an additional layer of protection. Therefore, even if someone manages to obtain your password, they will need your phone or use the security method you have chosen to access your Google account.
As for the ways to apply that second authentication factor, we have the following alternatives:
- Through text messages (SMS). In some cases your operator may charge you fees, this method is not considered safe because SMS can be intercepted.
- With a phone call in which the verification code would be provided to us.
- We could use the Google Authenticator app for Android, iPhone or BlackBerry and thus generate verification codes. It can also work, even if your smartphone doesn’t have phone or data connectivity.
- Using a security key in the USB port of a PC, it would be a “something we have” authentication.
- Printing or downloading alternative one-time codes for when our phones are not available.
- On your Android smartphone if you have active data connections, it may ask you if you authorize the login with a pop-up message.
Practical example of enabling Google 2-Step Verification
Once we know the advantages that Google’s two-step verification offers us, we will explain how to activate it. In this article, before starting this process, we recommend that you have previously established a strong password. This is the first thing you should do in your Google account to avoid being hacked.
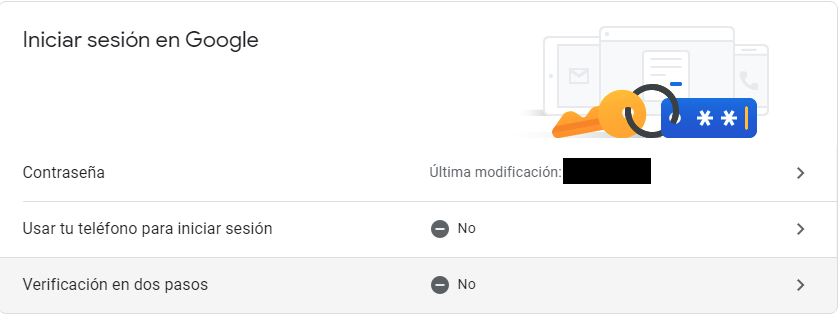
Two-step verification is also known as two-factor authentication. This will add an additional layer of security to our account in the event that our password is stolen. The first thing we have to do is enter our Google Account by entering our password if we have not logged in. Then we will have to go to the Security section, Sign in to Google and click on Verification in two steps .
At that time we will get a screen like this:
Here what we have to do is click on Start and we will advance to the next screen.
In the first part we will choose the device that will control the verification in two steps. By default, it will assign you the one of your main smartphone. In this case, Google has detected the correct one thanks to the fact that I have my phone number registered in the account. Then, you can also click “Show more options”:
Here it gives the possibility of using a security key, or text message or voice call. In this case, I recommend doing nothing, that is, if you do not plan to use it, it is better not to open this section. Next, we are going to click on ” Try Now ” to get to the next step.
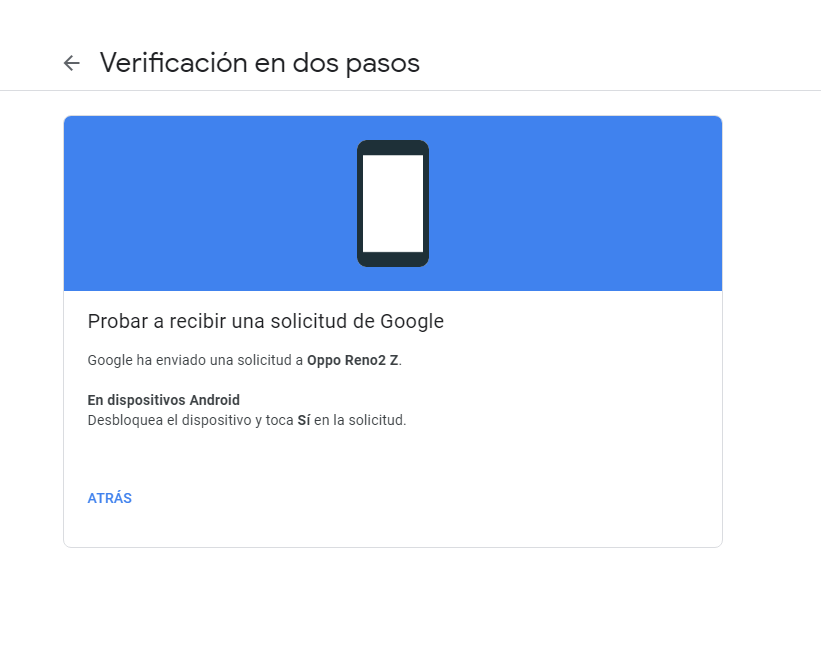
At that time Google has sent a request to our smartphone. At that time you must take your phone and unlock it when you receive a notification. Then you have to click Yes to that request.
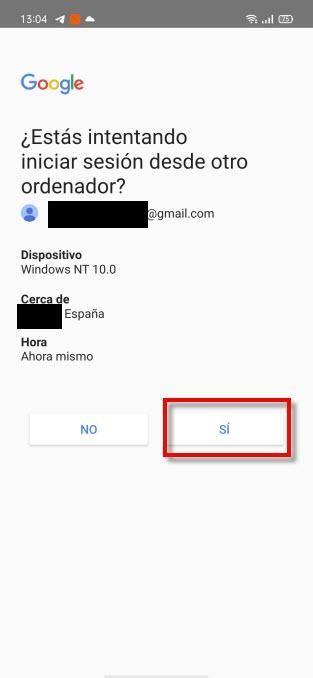
Once the request is accepted on our smartphone, we will proceed to carry out the last steps.
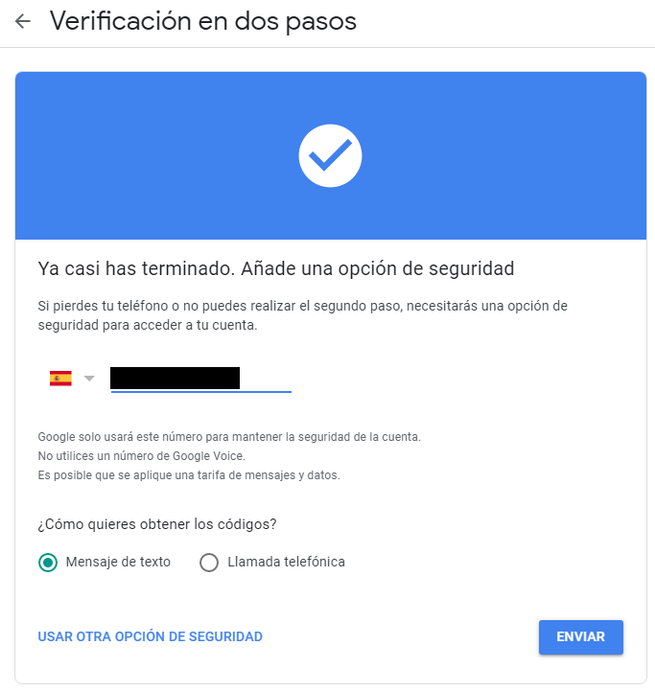
Then, to get the codes, I chose the option «Text message». Then I received an SMS on my smartphone and entered them. If done correctly, we will get a last screen.
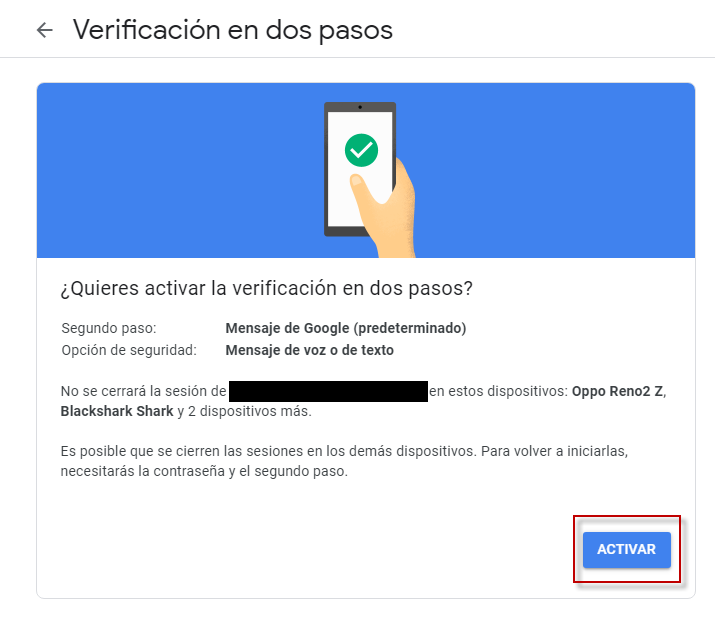
To finish with Google’s two-step verification we simply have to click Activate . From now on we have an additional layer of security that protects our Google account.
How to turn off Google’s 2-Step Verification
It is also possible that in the end you will not be convinced by Google’s 2-Step Verification. One of the reasons that we could find would be, for example, that it takes time when you log in on some occasions. Another may be because on occasion you have problems using two-step verification, and it prevents you from accessing your account. And it may even be because at a certain moment, you are working only from home and you think that you do not need so much security for a season.
Now what we must do is enter our Google Account by entering our password if we have not logged in. Then we go to the Security section, Sign in to Google and click on Two-Step Verification .
At that time we will get a screen like this:
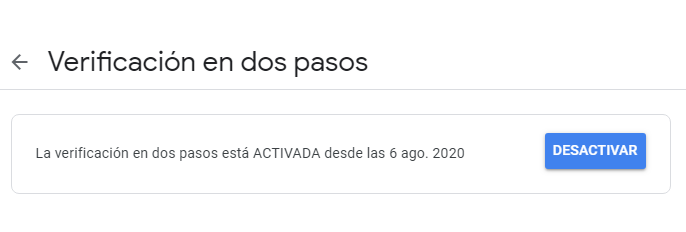
If we click on Deactivate we will start the process to stop using Google’s two-step verification. But before leaving it deactivated, this poster will appear with a warning:
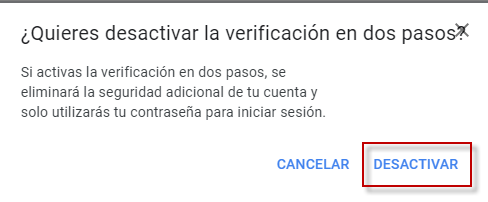
If we click on «deactivate» again, the process will be completed. Then, from that moment only our password will be our protection barrier. One way to check if it has been deactivated is to re-enter our Google account. There, at logging in, in the Two-Step Verification section, we will see: No.
Manage the devices that use your Google account and use common sense
We have already explained how to protect your Google account from being hacked. But there is one thing that we must never forget and that is the use of common sense , therefore, it is recommended that our devices:
- They must have the latest available software version installed.
- They must also have antivirus software and, if possible, antimalware.
Our way of acting must be impeccable so as not to take risks. In this section, common sense is a very important factor. Thus:
- We must avoid connecting to public WiFi networks and even less open ones.
- Nor should we enter our passwords on public or third-party computers.
Therefore, we must worry about keeping our devices up to date and acting wisely. Another thing that we must do periodically is to check the computers that use our Google account . This can give us a clue if we have an intruder, if you do not recognize a device, bad business.
If we want to do a check, the first thing we will do is enter our Google Account. We go to the Security section, Manage devices . It will give us the following information:
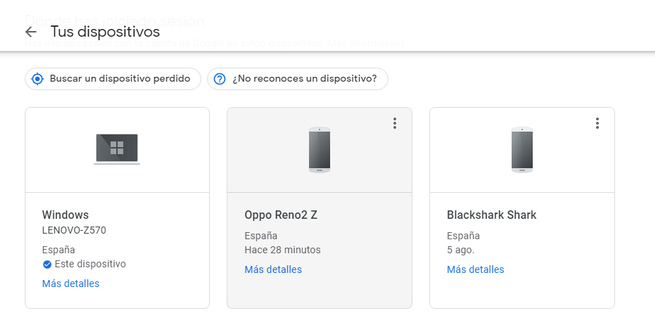
The first thing we have to do is verify that those devices are ours. In the case of having suspicions that one is not ours, the best way to proceed is to delete that device. Finally, the next thing we have to do is change the password to prevent access to that device again.
We hope that with this guide you can adequately protect your Google account and avoid any possible intrusion.