We do not stop with the leaks. This weekend there was a huge leak of Facebook user data, with 533 million records, 11 million of which belong to people in Spain. Among the data was the full name, phone, city, work, and even email. Now a similar leak has affected LinkedIn .
Specifically, the data of 500 million LinkedIn users has been collected and is for sale on the Internet. The database of the web to search for work has been discovered by CyberNews, where in addition the hackers have offered a registry of 2 million people as proof of the existence of the database.

Name, phone numbers, email and more leaked from Linkedin
Among the data that appears in the leak are the LinkedIn IDs of each user, full name, phone numbers, email addresses, phone numbers, gender , links to other LinkedIn profiles, links to profiles of other social networks , and work history and other information available in the profiles. Being a website with our online curriculum, all the public data that we have could end up in that database.
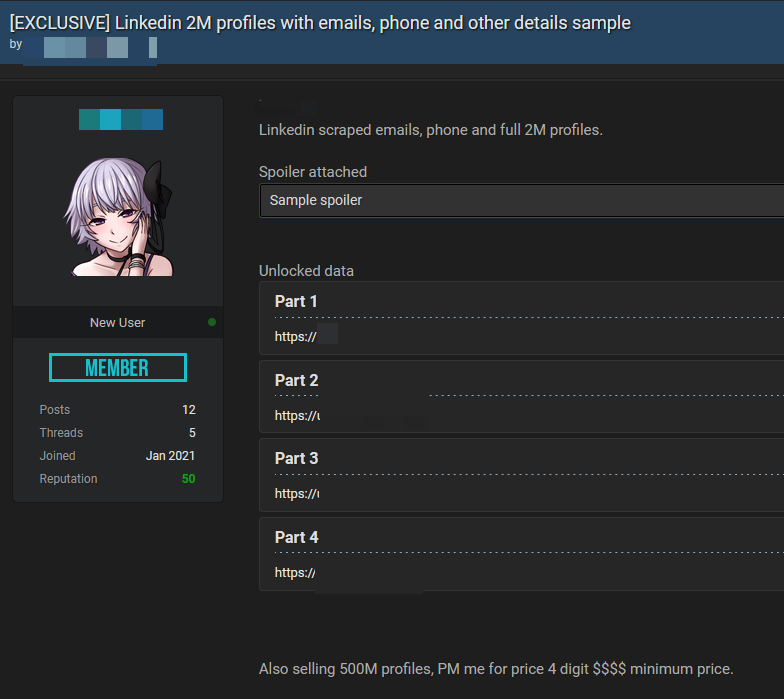
The data has been made available for sale on RaidForums, just like that on Facebook. In this case, the data owner is asking for at least 4-digit figures for the data as a minimum in exchange for the entire database.
As with the Facebook database, an attacker with all this data can carry out phishing attacks against us by knowing our name, email and much more information, giving a touch of realism if he impersonates a bank or another company with which we have contracted services. They can also phone us with spam calls and also impersonating other people. Finally, they can try to brute force our LinkedIn passwords.
Beware of spam phone calls or phishing emails
Therefore, it is advisable in these cases to be extremely careful with the calls or emails we receive . For example, we may receive emails from hackers posing as LinkedIn, where they are only looking for us to provide them with the password and other information to gain access. The recommended thing to do to make sure if it is a real email or not is to enter the official LinkedIn website and manually make the changes without clicking on any suspicious link.
Another recommendation is never to reuse passwords between various services, since if they manage to hack it on one website, they can reuse it on another to take control of the accounts if we do not have two-step verification activated. For this, it is recommended to use password managers with unique passwords for each platform. In turn, two-step verification with applications such as Google Authenticator is recommended whenever possible, since it is much more secure than using SMS.
At the moment we cannot verify if we are in the LinkedIn hack, so we will have to wait until the database is added to Have I Been Pwned, where the phones could also be added if enough appear.