Our personal data has a great value on the net and that causes many hackers to look for a way to collect information. In this article we echo how they have used Tor exit nodes to spy on users while browsing. A hacker managed to control a large number of nodes .
Hackers spy on users through Tor nodes
Specifically, this cybercriminal managed to control 27% of Tor exit nodes in February. This discovery was made by a security researcher named nusenu. However, although the maximum peak has been in early February 2021, during the previous 12 months they were able to control exit nodes.
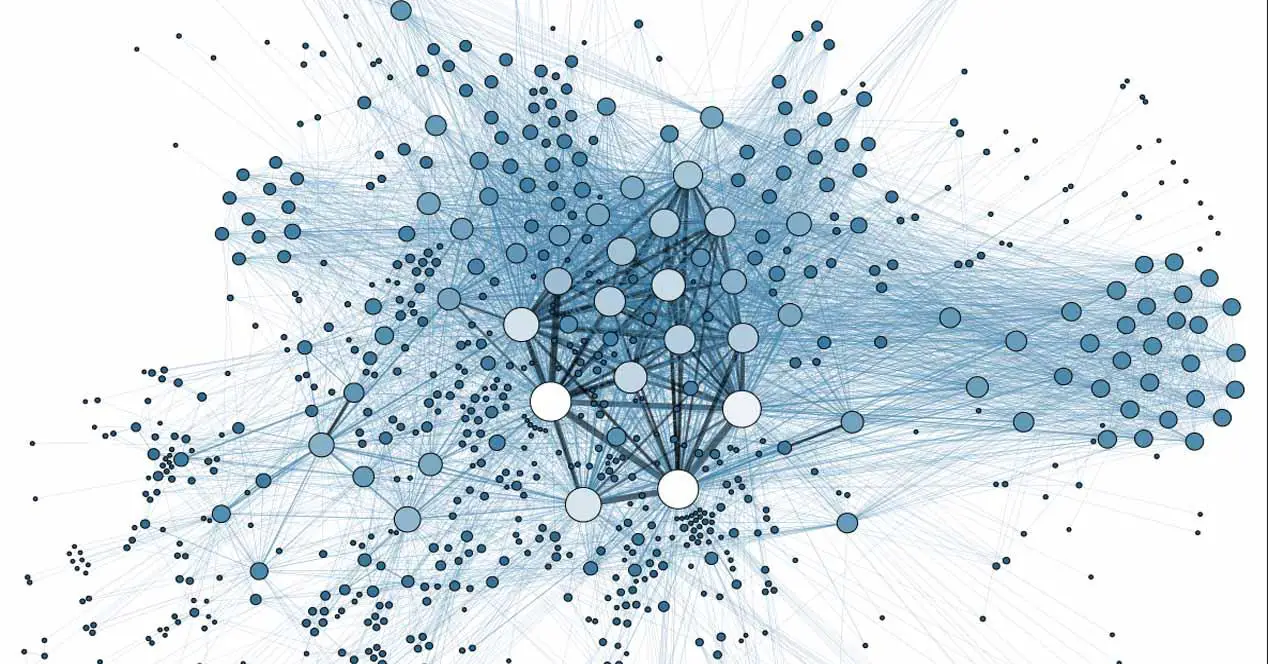
Keep in mind that Tor is a form of communication on the Internet that allows you to access the Dark Web anonymously. It is an open source software that allows to hide the origin of the user, his IP address, as well as the destination when visiting a web page. This is achieved by redirecting the connection through a series of nodes.
This is very useful to preserve privacy and prevent them from collecting user data, location, IP address, sites visited … We already know that privacy is a very important factor and there are many programs and tools that we can use to try to improve it. .
However there are different types of nodes . There are the intermediate ones, which are in charge of receiving and sending network traffic, as well as the outgoing ones, which is where it passes before reaching its destination. It is the latter that can present the most privacy concerns. In fact, they have already been used on occasion to sneak malware.
Now they have detected hundreds of exit nodes that are used for spying. The main objective is none other than to collect information. They can perform Man-in-the-Middle attacks and thus spy on the victim. According to the researchers, they carry out what’s known as SSL removal to downgrade traffic going to the Bitcoin exchange’s services from HTTPS to HTTP in an attempt to replace addresses and redirect transactions to their wallets instead. of the bitcoin address provided by the user.

Hackers can steal personal data
What happens if a user accesses an HTTP site , unencrypted? The attacker would prevent you from being redirected to the encrypted version. If the victim does not realize it, all information, personal data and what you send or receive could end up in the hands of hackers. We already know that there are attacks on the Dark Web and Deep Web .
To avoid this, one thing web developers can do is enable HTTPS by default. In this way, they could mitigate the risk that the nodes could be used by cybercriminals to steal users’ personal data.
Ultimately, the Tor network again has problems related to exit nodes. It is important that we are always aware that we are visiting encrypted websites, that we have correctly updated programs and maintain security on our computers. There are many attacks that we can suffer and it is always advisable to be prepared.