Hackers are constantly threatening users. By the mere fact of being connected to the Internet, our PC, and all the data stored on it, are exposed. Therefore, it is very important to have good security software to help us avoid falling into the clutches of hackers. But antiviruses are not always effective, as there is malware so complex that it is capable of evading the security of these programs, as is the case with the Emotet Trojan, which has returned to its old ways.
What is Emotet
Emotet is a polymorphic Trojan that allows hackers to adjust its functionality very easily remotely, making it very difficult for classic antivirus to detect this threat. This Trojan can expand or reduce its functions by means of “modules” , of which the SPAM module (to use the victim’s PC to send emails), the network worm module (to infect other PCs connected to the network) stand out. , the email password capture module and the browser password copy module. It is even capable of detecting forensic tools and virtual machines to avoid identification.

This malware first appeared in 2014 in Germany, Austria, and Switzerland, quickly reaching the United States and the rest of the world. In 2015 and 2018 it had new waves, with each one becoming more complete, dangerous and undetectable. And in 2020, this malware has carried out a wave, with which it has infected millions of computers and, in addition, it has gone practically unnoticed around the world, leaving victims at the mercy of hackers.
How to detect Emotet
This Trojan is quite difficult to detect , especially after it has infected a PC. Antiviruses cannot detect the threat and, furthermore, due to its advanced persistence functions, if it is detected and removed, it regenerates itself more out of the box than ever.
Therefore, to detect it successfully, it is necessary to use specific programs, such as EmoCheck . This open source software is designed to allow us this malware. Even if we have been infected by the newest version of it, which began circulating in April of this year and infected millions of computers in July, we can know that our PC is infected.
Just by downloading the program and running it, we can diagnose our PC to see if we are infected or not. We recommend running it with Administrator permissions to be able to correctly analyze the PC.
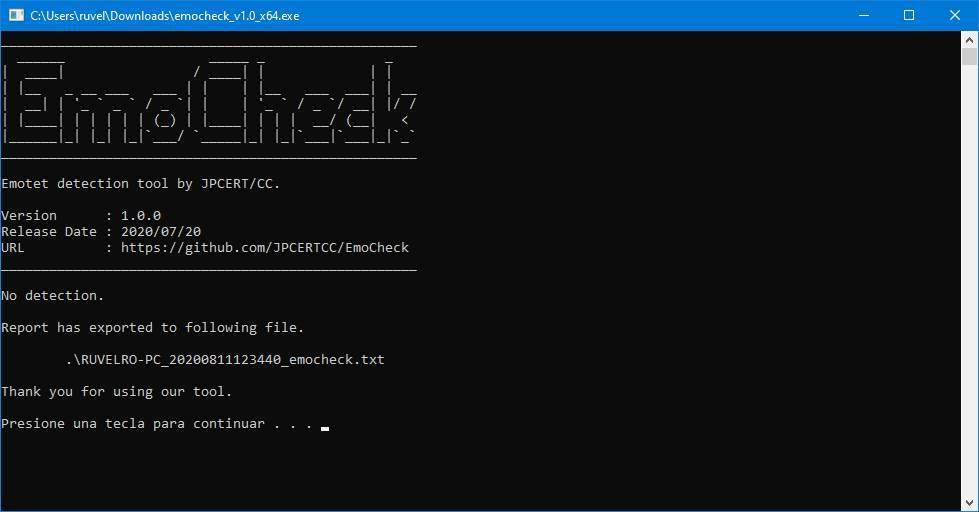
If not, this program will not tell us anything else. We can close it and continue using the PC normally. But in case of being infected we will be able to see a warning message indicating the PID (Process ID) of the malware, as well as its executable

We can check if this process exists from the Windows 10 Task Manager, in the “Processes” tab or in the “Details” tab.
If this is the case, then what we should do is isolate the computer (disconnect it from the Internet), restart Safe Mode or a Linux Live distro, and delete the file that it does not indicate.
After eliminating this executable, we will have to analyze the PC with a good updated antivirus to make sure that there is no trace of it. And, if we can, even with other anti-malware software to get a second opinion on PC security. It also doesn’t hurt to check our bank accounts , to check that everything is correct. And change the passwords of all the services we use, just in case the Trojan has stolen the Windows or browser passwords.
Protect our PC from this Trojan
To prevent this Trojan from infecting our PC, the first thing we must do is make sure that we have Windows 10 updated with the latest security patches. Furthermore, it is also necessary to have efficient and reliable security software that allows us to detect the threat in time, if possible before it reaches our PC.
Windows Defender and Malwarebytes Anti-Malware are an excellent combination of antivirus and antimalware thanks to which we will be able to detect the virus before it reaches our PC.
Of course, we must also have safe practices when browsing the Internet. There are many ways in which this Trojan can reach our PC. The main one is through malicious websites that include a JavaScript script designed to distribute the threat. But it can also be through malicious emails that reach us with attachments. Of course, these files should never be run.
The software we use to connect to the Internet must also be up to date, especially the web browser (Chrome, Firefox, etc). The more up-to-date the PC is, the less likely it is that the infection will reach us through a vulnerability. And using legal software also helps avoid potential infections.