Cybercriminals are always on top of the latest trending topics. The coronavirus or Covid-19 is one of the elements that is most affecting the lives of all people worldwide this year. This made criminals soon see their potential, and they decided to exploit the coronavirus pandemic with malicious emails to try to make money from their victims.
The coronavirus has changed our way of life and work
The COVID-19 outbreaks have disrupted the lives and operations of many individuals and businesses. Our way of life has radically changed with specific confinements, and, in addition, teleworking has gained further momentum.

However, cybercriminals are not oblivious to our concerns and have exploited them for their own benefit. In this case, they decided to take advantage of the coronavirus by sending malicious emails to our inboxes. This is how they intend to take advantage of the concern that the pandemic is generating in us. These types of e-mails that we receive are important, since they explain how we should work, the new way of ordering and more.
They have taken advantage of the coronavirus to send malicious emails
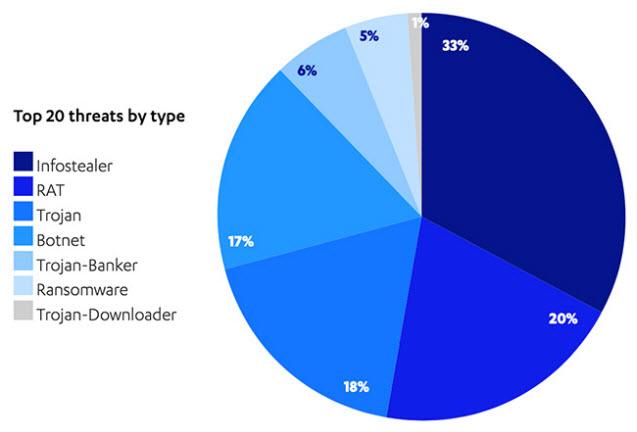
According to security company F-Secure , this is the current attack landscape. Here are the top 20 threats by type.
Starting in March, and for most of the spring, a significant increase in malicious emails using Covid-19-related issues could be seen. The goal was to manipulate users by exposing them to email attacks and scams.
Cybercriminals quickly exploited the coronavirus seam by sending malicious emails. These campaigns sought to deceive users in one of two ways:
- Ordering masks on fake websites.
- Causing infection with malware after opening malicious attachments.
In that sense, three-quarters of the attachments in these emails contained malware. His objective was none other than stealing confidential information, such as the passwords and other credentials of the victims.
Detecting malicious emails is not an easy task, and employees need to be prepared to prevent information leaks. Here you have explained how to identify malicious e-mails .
Email and working in the cloud, a source of danger
In terms of sectors, the financial one should be noted that Facebook was the most frequently forged in phishing emails. However, it should be noted that financial companies have proven to be the most popular for spoofing in phishing emails. If we were to join all the banks together, they would represent 32% of the attempts in this category. This shows that there are sectors that are more vulnerable to Phishing attacks.
These are the companies that have been used the most in phishing emails.
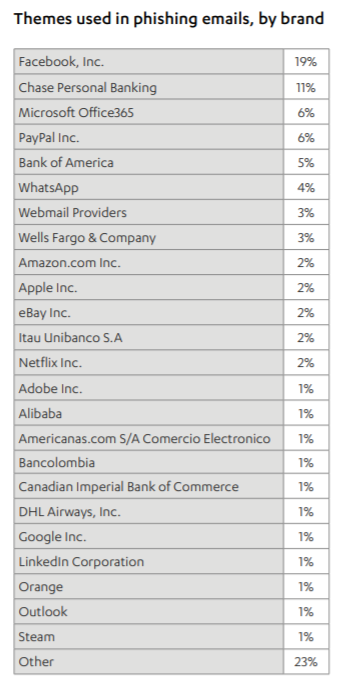
Here we must not forget that, apart from those that have affected Facebook and the financial sector, cybercriminals have also taken advantage of the coronavirus pull by sending malicious emails. Email has been the most popular way of spreading malware in the first half of the year, accounting for more than half of all infection attempts. In this sense, the most common malware spread by attackers has been Lokibot .
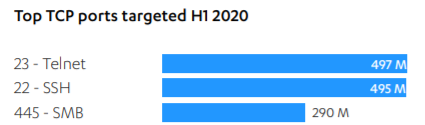
As for the most frequently scanned IP ports, they were Telnet, SSH and greater distance SMB. Here you have the data:
Furthermore, we can also see that attacks that take advantage of cloud-based email services are steadily increasing. Here is a significant increase in phishing emails targeting Microsoft Office 365 users.
If you look at the table of companies that have been impersonated to send phishing emails, we see how it is in third position. Here is a graph of how it has affected Office 365:
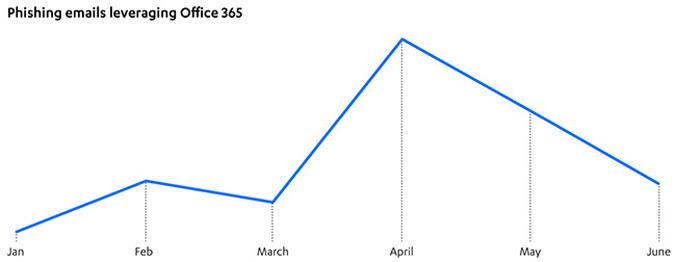
Here you can see how April was a time when this version of Office suffered the highest volume of phishing emails.
Finally, we can say that cybercriminals in this first half of 2020 have benefited from the coronavirus by sending malicious emails, without forgetting about phishing on Facebook and Office 365.