Windows periodically releases its security patches to solve any possible failure that has appeared in the operating system. And it is important that we always update. But this month it is even more so because Microsoft‘s security patch resolves almost 70 different vulnerabilities.
Microsoft has released its new security patch and it is best to update as soon as possible. In total, the new patches solve or correct 68 vulnerabilities, but the company has indicated that, of all, there are eleven security flaws that are considered critical. But not only these, the rest have also been classified as being of important severity, so update as soon as possible.

S and vulnerabilities
The 68 failures or vulnerabilities have been divided into different groups that classify them according to type or according to errors, as we can read from Microsoft’s own website. Of them, a total of 27 privilege escalation vulnerabilities. These are followed by 16 remote code execution security flaws, 11 “Information Disclosure” type flaws, 6 “Denial of Service” vulnerabilities, 4 “Security Feature Bypass” type security flaws and “3 Spoofing flaws”. ”.
In addition, the list of actively exploited vulnerabilities has been provided. In other words, they allow remote code execution and are a serious risk to our computer if they are exploited by any hacker. Are:
- CVE-2022-41128: A bug in Windows Scripting Languages that enables remote code execution.
- CVE-2022-41091: vulnerability in Windows Mark of the Web that allows the evasion of different security measures.
- CVE-2022-41073 – Bug in Windows Print Spooler that allows the option to gain privileges on the PC.
- CVE-2022-41125 : error in Windows CNG Key Isolation Service that would allow, like the previous one, to gain privileges on the PC.
- CVE-2022-41040 : security flaw in Microsoft Exchange Server that allows, like the previous ones, to gain privileges on the PC.
- CVE-2022-41082 – A remote code execution vulnerability in Microsoft Exchange Server.
For all these reasons, we must update as soon as possible to put an end to the different vulnerabilities and bugs that we have been able to find.
How to update
If you want to update your computer and there is an update ready, it will be common for a notification to appear on it that allows you to press a button. But if not, we can search for them manually in its configuration.
We simply have to go to “settings” on our computer and go to the last section: “update and security” . Here we can see if there are updates available on the computer or if you have already updated but you need to restart to complete the process, as you can see in the image below.
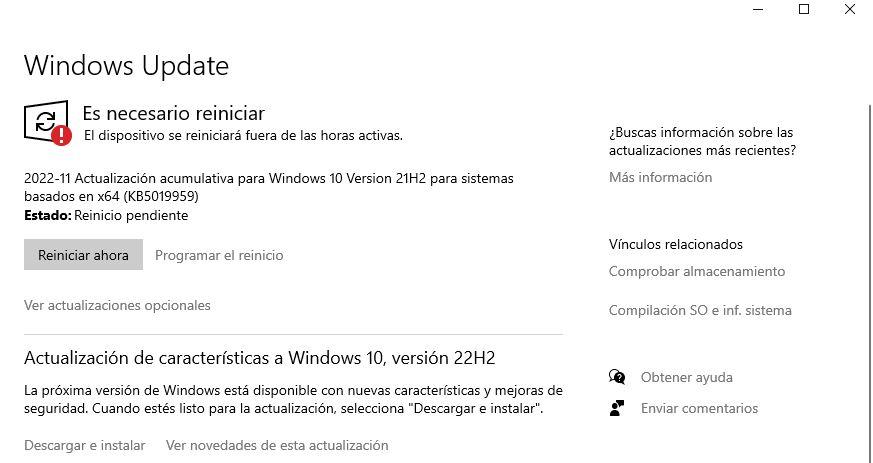
We will only have to follow the steps from the Windows configuration to complete the process. Click on “download and install” if you want it to start downloading or touch on “what’s new in this update” if you want to know what improvements or changes your computer will have once you do it. When you have completed the restart, you will already be protected from the aforementioned vulnerabilities, but that does not mean that you must always be aware of what websites you visit or what you should be careful with.