Security is one of the essential points that manufacturers must demand, especially to protect our devices from all kinds of malware. However, in the last few hours it has been discovered that app signatures , a security mechanism that Android has, have been compromised.
The seriousness of the matter must be taken into account. More than anything, because this signature is what certifies that an application that has been created by a particular developer has not been subsequently modified. Well, these particular certificates have been leaked. Among those affected we can find recognized brands, both smartphones and processors, such as Samsung, LG or MediaTek.

They leave the door open to malware
One of the main problems that have been found as a result of this is that, those certificates that are used to sign the system apps, are also used for the Android app, ” android.uid.system “, which has all kinds of privileges. Therefore, if an app is signed with the same certificate, the door is left open for malware to have the same system permissions and privileges, as it is signed with the same certificate. And, on this occasion, it has been found that there are already several examples of this style.
For this reason, one of the most important points is to always have the certificates under control. Basically, because the developers will need it to continue updating those same applications that they have been developing. And it is that, the mobile operating system verifies that it has been signed with that same certificate to know that it has not been modified by third parties.
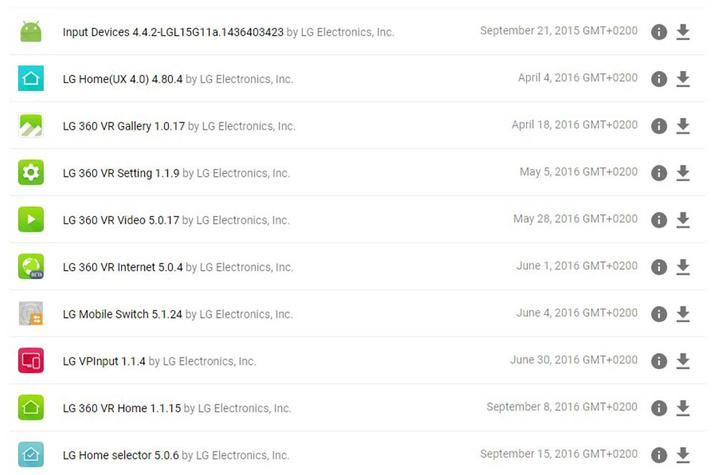
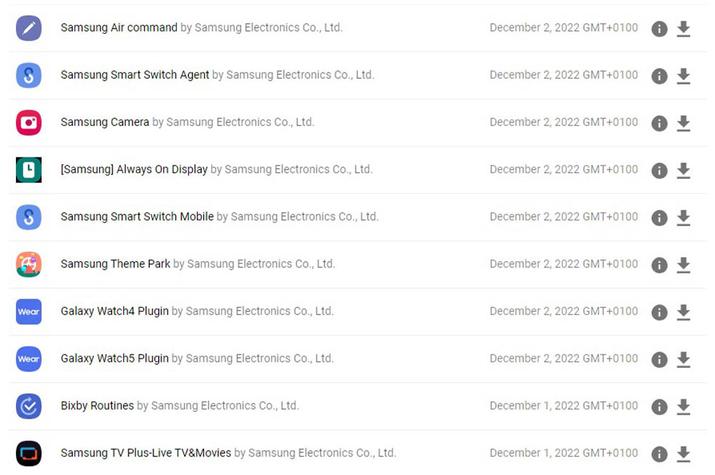
Specifically, this problem has caused different malware to have the same privileges as the Android app itself. Furthermore, the leaked certificates have been found to be from Samsung Electronics, LG Electronics, Revoview, and Mediatek. In the event that you have any of the following apps that appear in the following images on your smartphone, they could be vulnerable to this particular problem, since they are signed with the leaked certificates:
What is the solution
This particular issue was discovered by a reverse engineer from the Android Security team . In addition to sharing it on his Twitter account. Basically, it detected how several apps with malware used Android certificates.
Although, the solution that Google has proposed is for the different manufacturers to change the platform certificate to a completely new one as soon as possible. In this way, it is possible to invalidate the certificates that have been filtered. But, for this, an OTA will be necessary . However, steps have already been taken to “minimize the impact”.
In addition, they make it clear that Google Play Protect will be able to find apps with malware that include these certificates. In this way we will not fall into their traps and we will not install them on the phone. And not only this, but from Google they clarify that “OEM partners quickly implemented mitigation measures as soon as we reported the compromised key. End users will be protected by user mitigations implemented by partners.”