When we talk about the different types of software that we normally use on our computers, whether desktop or mobile, one of the main ones is browsers. These are programs that over time have gained in importance, we talk about proposals like Google Chrome .
In addition, as we have seen firsthand, these have not stopped evolving and improving based on updates and new features. But despite all this, users demand even more in most cases, and that's where popular extensions come into play. To say that these are very useful tools that can improve the browsing experience in a simple and direct way.
At the same time, we can find them of all kinds, from those related to security, to those in charge of accelerating navigation or automating tasks. Many of these work in the background and almost without us being aware of their existence. But of course, as in most areas of the software, there are also extensions that try to harm us, the so-called malicious or dangerous extensions of the browser. It is worth mentioning that these, whether due to a defective design or bad intentions, can cause damage to the equipment or endanger our personal and private data.
Avoid extensions with malware in the browser
Therefore, we will give you some very useful tips to ensure that the extensions we use will not cause us problems in the future. The first thing to do is read the permissions of each add-on carefully before installing them in the browser. This is something we don't usually look at, accepting the conditions automatically, which is clearly a mistake. However, with this first step we ensure that an element of these does not perform unwanted activities on the device.
It is true that it can be a somewhat boring task, but in many cases, we will appreciate it in the future. And there are extensions that are granted permits unnecessarily asking for access to more personal information than you need to carry out your function. This could be because it also intends to use that personal data in a way that we do not want, so we should consider discarding it. It is also advisable to make use of extensions of trust among the many that we can use.
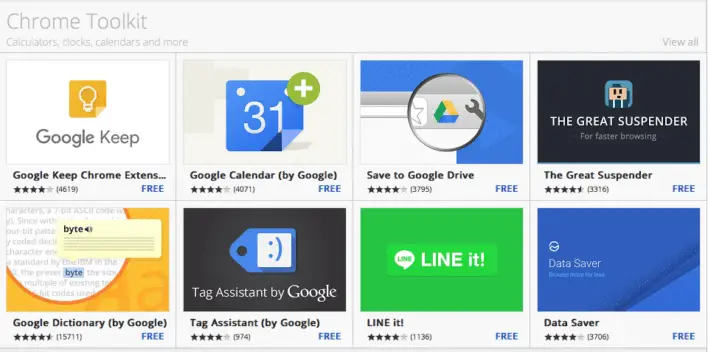
Although we found a lot of extensions in the official Chrome store, we should not install any developer's projects. And it must be borne in mind that it is easy for cybercriminals to create extensions with hidden code to steal data. Therefore, before installing an extension we must check the ratings and reviews of other users. This will make us see the negative sections detected by others or if it has very few facilities, which could be a bit suspicious.
Dangerous extensions may be in the official store
Therefore, we can also send an email to the developer to ask any questions we have. Thus, if we are not satisfied, we can discard its installation, or remove it if we had already installed it. Also, it is not good to abuse these, since in many occasions we install extensions that we are not even going to use, or we do not uninstall the unnecessary ones. Moreover, the intensive use of these negatively affects the performance and operation of the browser itself.
Changing third, we must also keep in mind that if an extension suddenly requests a new set of permits, we should suspect. And it is possible that it has been pirted or sold to a third party and needs to be eliminated. This is a tactic that cybercriminals often use to extract personal data from users, buying extensions that have been abandoned by their developers. Therefore, we must never accept a new set of permits without finding out the reason for it.
And finally, we will tell you that we must avoid websites that offer multiple grouped extensions. We say this because there are developers who use this tactic to introduce some malicious extensions into the set, without us noticing.