The global pandemic caused by the COVID-19 coronavirus has accelerated some trends that already showed potential, but which seemed to take years to become massive. We are not going to review them all, but we are going to focus on teleworking. Working from home first started out as forced by the situation, with long hours of Zoom meetings or endless chats in Slack. However, the passage of time has revealed the benefits for both workers and employers. This summer, telecommuting is not going to be an exception and we bring you 6 vital tips for your safety.
One in two workers plans to telecommute this summer. Taking advantage of the arrival of good weather and the expansion of high-quality connections, whether fiber or mobile, many will choose to continue working far from the big cities or at least without going to their work station, as long as they are allowed to do so. . In fact, 80% of managers would allow their staff to change residence according to a recent study.

To the above, we must add the growing number of cyber attacks detected, a trend that also does not stop growing. Users’ personal computers are usually a vulnerable point through which to sneak into the corporate network of a company, so we must be able to detect and avoid cyber attacks.
Detect cyber attacks
Udemy computer security experts and instructors give us six keys to learning how to detect and prevent cyberattacks:
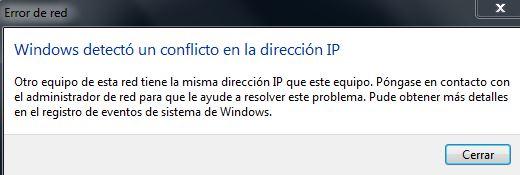
IP address cloning
Through the message “Windows detected a conflict in the IP address” we are alerted about a possible use of ARP ‘poisoning’ techniques by the intruder. This is mainly used to break into the local network and steal the data that passes through it.
Failed logins to the computer
“During a login attempt, the user’s security context accumulated too many IDs. of security. Please try again or consult your system administrator ”. Another message that highlights the existence of security problems , especially if the security policy restricts a single login per user account and per computer.
Slow file saving or LAN network
The “broadcast storms” , that is to say, that the network is being saturated, are one of the ways of acting of the hackers. The user usually perceives slowness when saving a file or accessing a web page. If we detect it, we may be having an attack.
Company domain changes from https to http
If when accessing the domain of our company from the browser we see that it has stopped using https encryption and now shows only http , this indicates that the security of access has decreased and we may be victims of an attack.
The WiFi network is constantly connecting and disconnecting
In addition to a performance issue, this can mean a deauthentication attack on the router . This type of attack seeks to obtain the credentials to the company network.
Files appear and disappear
The last aspect that can help us detect a cyber attack is files mysteriously appear and disappear from servers or computers. We can also see how the extensions of some files are changed, with ransomware being the culprit in that case.