
Tips for saving files on the Internet safely
Storing files on the Internet is a very interesting option to create backup copies or simply share it with someone. There are many alternatives, but […]

Storing files on the Internet is a very interesting option to create backup copies or simply share it with someone. There are many alternatives, but […]

The popular manufacturer of routers, VPN routers and firewalls for companies, Zyxel, has suffered a serious security flaw in its operating system. This critical vulnerability […]
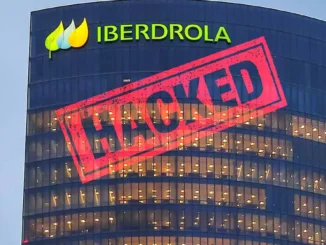
The price of electricity will not be the only concern of Iberdrola’s customers today. The company has reported a cyberattack that they have suffered and […]

All of us use a password to log in to different online accounts, whether in banks, email, websites to see the consumption of electricity, gas, […]

While the number of cyberattacks skyrockets each passing day, cybersecurity practices also evolve to fight with them. At first, the idea was never to let […]

The security measures we use are not always equally valid. In the same way that hackers update their attacks, it is necessary for users to […]

To find out to what extent a device or a network is secure, we can perform different tests. It is always important to protect the […]

When we connect to the Internet, all applications redirect their traffic through certain ports. While some ports are open by default (for example, 80 for […]

You can have intruders on your computer with both physical and remote access. Think, for example, when someone has been able to take your PC […]

Cybercriminals are always focused on trying to get money from their victims, to achieve their goal, they use any type of method in order to […]

We live in an increasingly digital world and that is changing our ways of doing things. However, deep down despite this we have the same […]

Users are increasingly concerned about our security and the first line of defense should be to have a good password. Obviously not all are the […]

Keeping Windows in good condition is essential to ensure that it works well and that our data is safe. For this, something essential is to […]

We generally use a certain main operating system on our computer, but we can also install a secondary one or try another one through a […]

On a regular basis we try to avoid the arrival of all kinds of malicious code on our computer, although we are not always successful. […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise