
If you see these signs, your Smart TV may have been hacked
In this article, we will examine several indicators of abnormal behavior in a Smart TV that could suggest a potential security breach, where a hacker […]

In this article, we will examine several indicators of abnormal behavior in a Smart TV that could suggest a potential security breach, where a hacker […]

There is no denying that the internet is a vast source of information, where all kinds of data can be found. Unfortunately, this means that […]

It is crucial to prioritize security when connecting to a public Wi-Fi network due to the inherent risks involved. The presence of potential intruders who […]

Passwords play a crucial role in safeguarding our accounts and protecting ourselves against potential cyber attacks. Making even a small mistake in password selection can […]

Receiving fake messages on WhatsApp has unfortunately become a common occurrence, with hackers increasingly utilizing this method. These malicious individuals employ various techniques to grab […]

Bizum is indeed a popular option for sending and receiving money, especially for splitting bills at restaurants or contributing to gifts among colleagues. However, it’s […]

Sharing the internet connection from your mobile device is a common practice that allows you to provide internet access to other devices or individuals. For […]
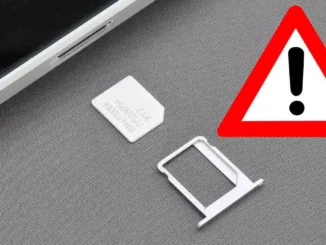
When we switch our SIM cards, it’s common to disregard the old one, leaving it in a drawer or even discarding it, assuming it holds […]

Using WhatsApp has become a daily routine for staying connected with friends, family, and even for business communications. It offers convenience, versatility, and features like […]

The usage of numerous personal passwords has become increasingly common, making the security of these passwords a top priority for many individuals. To address this […]

Your personal data and passwords are at risk of being stolen through various methods employed by hackers. One strategy commonly utilized by hackers involves targeting […]

Hackers possess the ability to exploit various types of apps to launch attacks, steal information, and compromise your passwords. However, there are specific programs that […]

As an iPhone user, it’s important to be aware of a built-in feature that allows us to assess the security of our passwords. This functionality […]

Phishing and identity theft have been persistent threats for several years, aiming to compromise our private, financial, professional, and personal information. While iPhones are known […]

In our daily lives, cloud storage has become an integral part of our routine. With numerous available platforms, we can conveniently store files of various […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise