Although we are generally used to using the tools that usually come by default in Windows, the variety of options is not limited to them. Microsoft has different tools designed so that advanced users and system administrators can have much more control over the system. A clear example of this is the Microsoft Sysinternals , a set of tools, such as Process Explorer or Sysmon that help us manage Windows to the maximum.
What is Microsoft Sysmon
Sysmon is one of the essential advanced tools for all those users who want to have absolute control over the system. Once this tool is installed, Sysmon automatically takes care of recording all events and all system activity. This software that is configured as a service and is running during system reboots in order to know in detail what happens while Windows starts , we work with it or we turn it off.
This tool gives us detailed information about all the processes that are created, the network connections that are established, and the changes that are made when creating files. In this way, it is possible to detect, with relative ease, all kinds of suspicious or unauthorized activity that could be a danger to the computer, such as malware.
And now, with the new version 13 of Sysmon , it will even be possible to detect the most complex malware.
What’s new in the new version 13 of Microsoft Sysmon
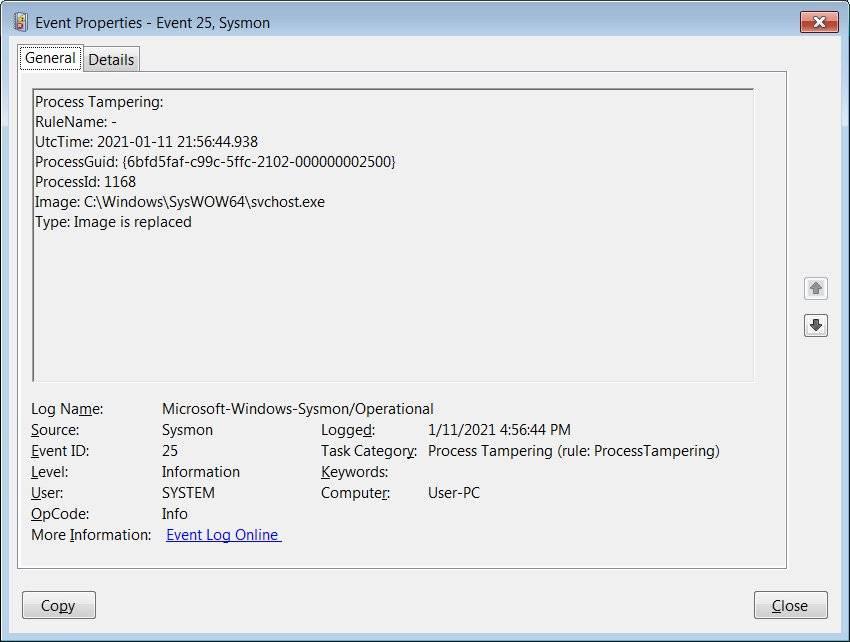
Undoubtedly, the main novelty of the new version 13 of this tool is the possibility of detecting the processes that have been manipulated to try to deceive antivirus or other security software. When malware takes advantage of Process Tampering , it is usually hidden within an apparently trustworthy process. And since many of the security programs have these processes whitelisted, they go unnoticed. Even if we open the task manager, we won’t be able to identify it.
This is a technique widely used by more advanced malware such as Mailto / defray777 ransomware, TrickBot or BazarBackdoor. Fortunately, thanks to the new Microsoft Sysmon 13, we will now be able to detect these types of threats. To do this, we only have to download the new version from its website and manually add the “ProcessTampering” option within the program’s configuration file. This new directive is part of the Sysmon 4.50 configuration scheme.
Once this instruction has been added, we must execute the program using the -ie parameter indicating the corresponding configuration file. For example:
sysmon -i sysmon.conf
From now on, Sysmon will monitor all PC activity . When something tries to control a process and it is suspicious, an Event 25 will be generated within the Windows Event Viewer , which will indicate that there has been a process alteration.
Does it really work?
From Bleepingcomputer they have put this new function to the test to see if it really works to detect malware. The experts have downloaded and executed, in controlled environments, versions of the TrickBot and BazarLoader malware. And, unfortunately, Sysmon has not been able to detect the alterations in the processes that these malware carry out.
What the new Sysmon 13 has detected are many process alterations in the browsers, both in Chrome and in Firefox and Edge. All of them, of course, false positives. It seems that Microsoft still has to refine its tool a little more so that it can be useful.