Good security to protect our accounts is vital if we want to protect our data and all the information we keep on the PC. The login, or login, is the point that prevents an unauthorized user from logging in with our account and accessing all of our data. However, if we want to be really protected, it is not enough for us to configure the account and forget it, but we have to carry out a series of tasks so that it is completely protected.
Group Policy is a unique feature of Windows 10 Pro . Windows 10 Home users will not be able to run “gpedit” in the way we will explain here. Although they can use specific software, Policy Plus , which will allow these users to access these administrative settings without having a Professional edition of Windows.

What are account policies
Account policies are a series of advanced settings , intended primarily for administrators, that allow us to limit the number of login attempts and force password change and use of strong keys. In this way, instead of being able to test passwords indefinitely, we will be able to establish a maximum number of attempts, and choose what will happen if said threshold is reached. And, furthermore, by being forced to use a secure password, it will be practically impossible for them to enter our account.
By activating the account lockout policy , what we do is tell Windows 10 that it can only allow a maximum number of login attempts. And, in case of exceeding it, it will block the session for a time, preventing more passwords from being entered. And, if we activate the password policy , we will force them to make good use of them.
In this way, we will be protected against brute force attacks.
Activate account lockout policies
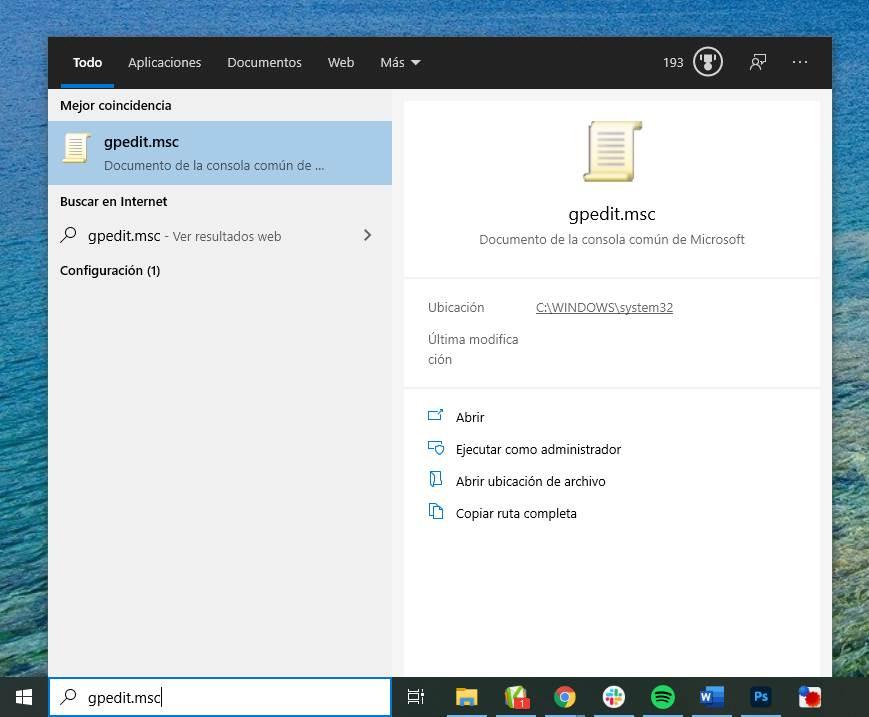
To access these options, the first thing we will do is run the following command: gpedit.msc. We can do this from the Windows 10 search bar, or from the “Run” window that will appear with the Windows + R keyboard shortcut.
Once we see the window for local group policies, what we must do is navigate to the following directory:
Configuración del equipo > Configuración de Windows > Configuración de seguridad > Directivas de cuenta
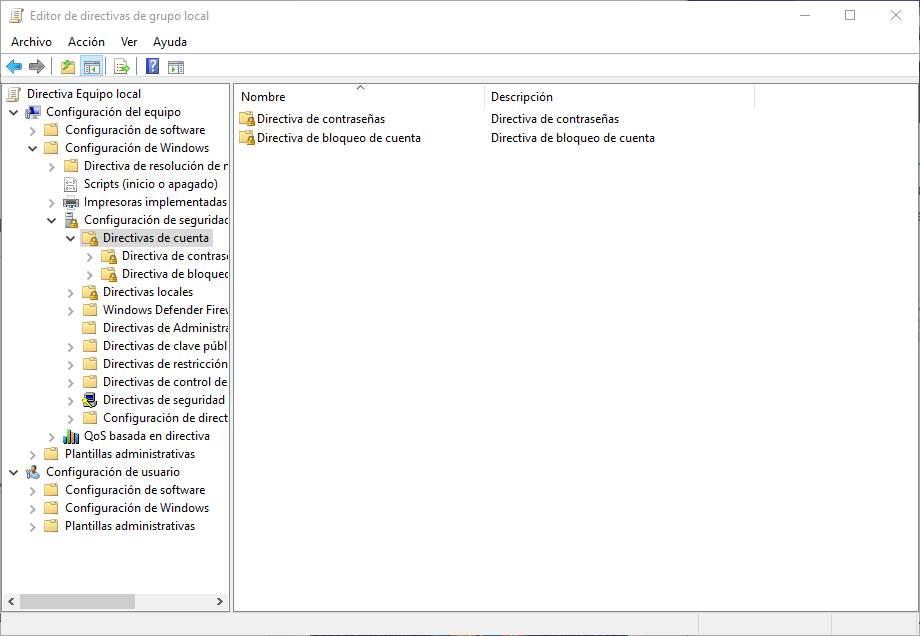
Once at this point, we will double-click on “Account blocking policy”, and we will be able to see the different options that we can configure in this section.
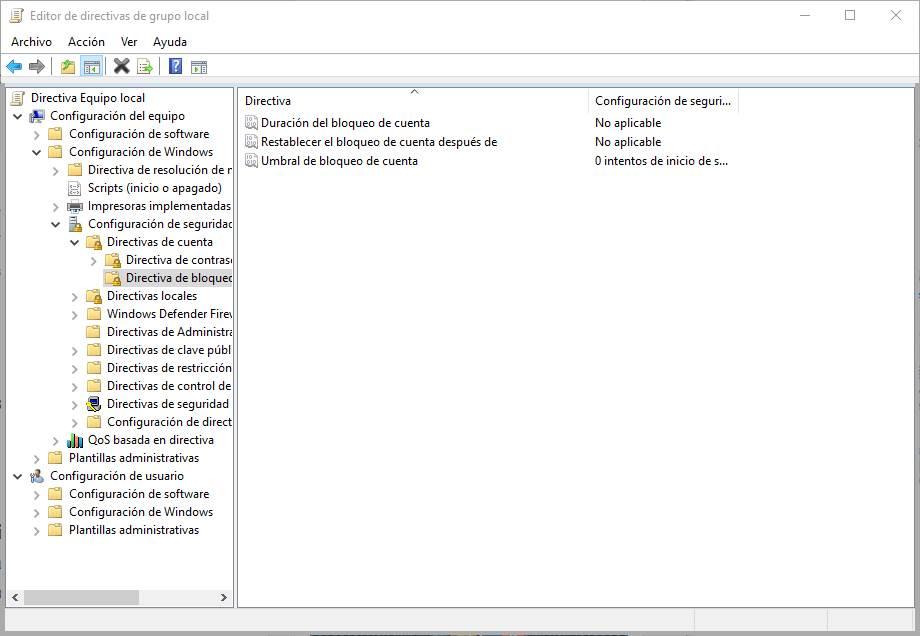
The first option that we have to activate is the ” Account lockout threshold “, since the others will not be available until then.
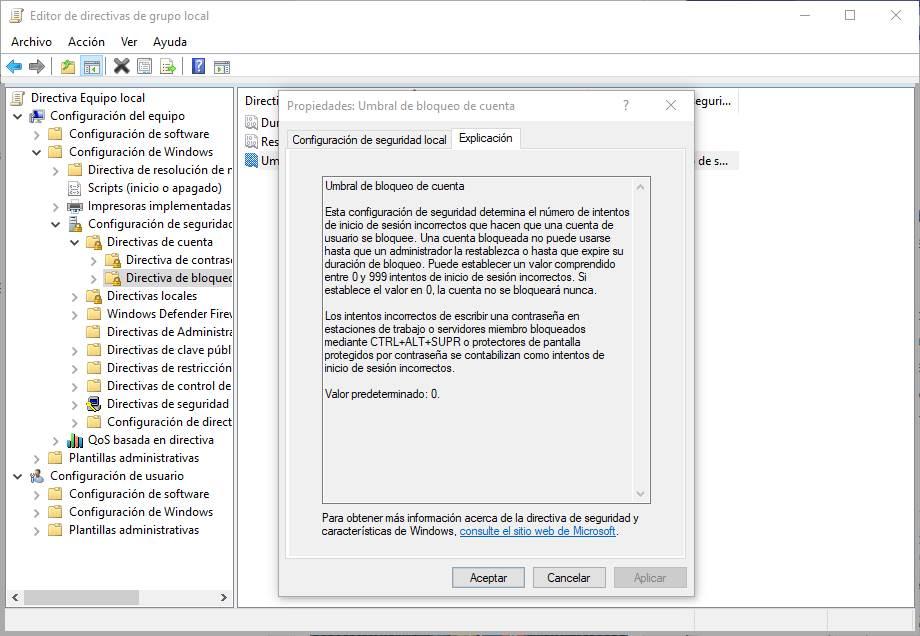
In this security configuration we must specify the number of incorrect login attempts that must be made in order for the user’s account to be blocked. Once blocked, the account will be inaccessible to all users until it is restored or until a specific time has passed that we can specify in another policy later.
The value that we can give to this policy ranges from 0 attempts (without protection) to 999 attempts.
The next option that we must configure will be ” Account lockout duration” . This will allow us to specify how long the account will be blocked in case the password is entered incorrectly the times we have specified in the previous point.
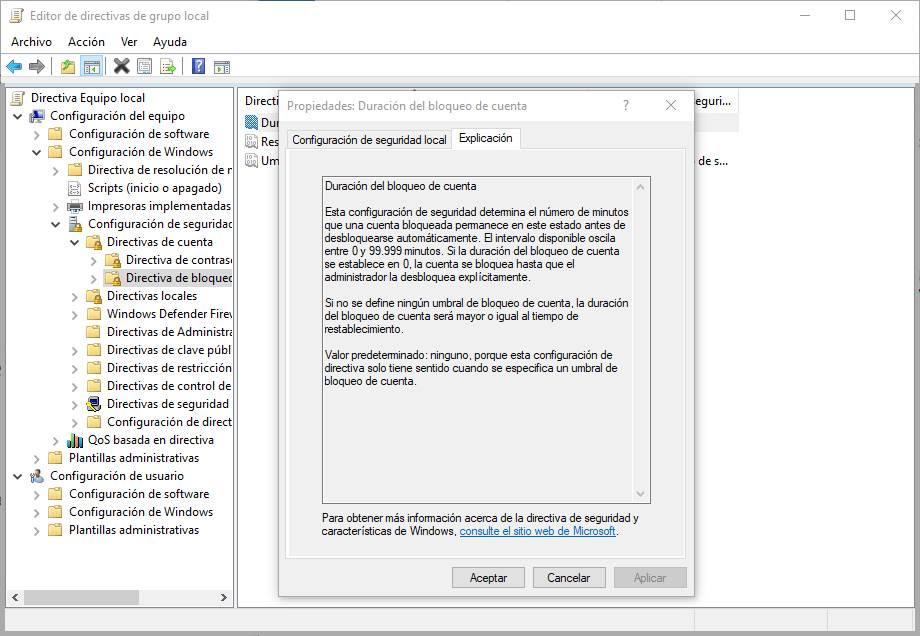
The time interval that we can specify ranges from 0 minutes to 99,999 minutes. If you specify “0 minutes, the account will be blocked and the administrator will have to manually unlock it from the server.
And finally, we have the option ” Reset account lock after .” From this policy we will be able to specify the time that must pass from when we have entered the wrong password once until the counter returns to zero. The value of this account must be equal to or less than the duration of the block.
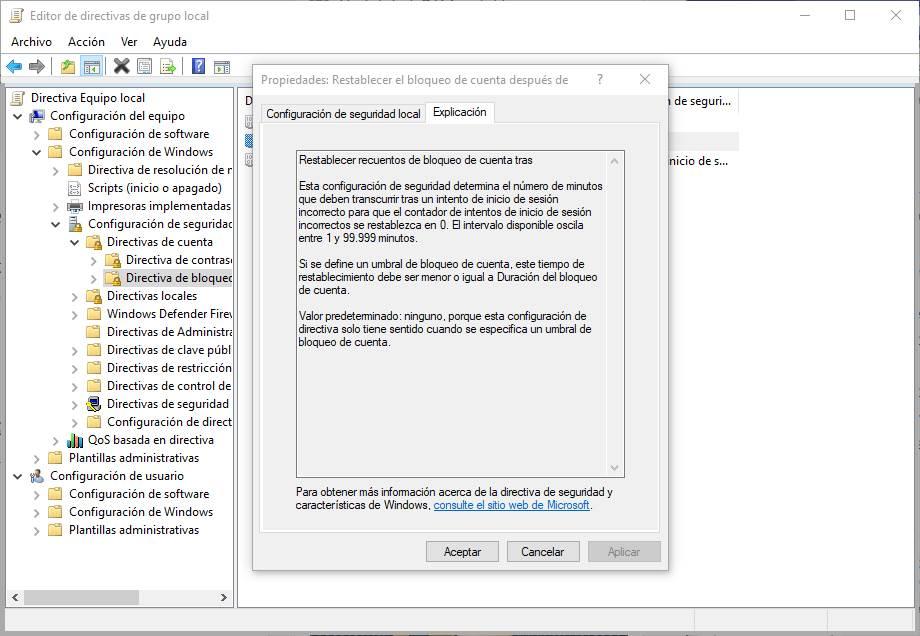
The minimum value that we can configure is 1 minute, and the maximum is 99,999 minutes.
Configure password policy
In addition to setting up automatic account lockout, we can also set up a password policy that requires PC users to use strong passwords, and also change them frequently to reduce the likelihood that they will be able to access our account without permission.
To do this, we must return to the previous section of the group policies (that is, to Computer Configuration> Windows Settings> Security Settings> Account Policies), and enter within “Password Policies”.
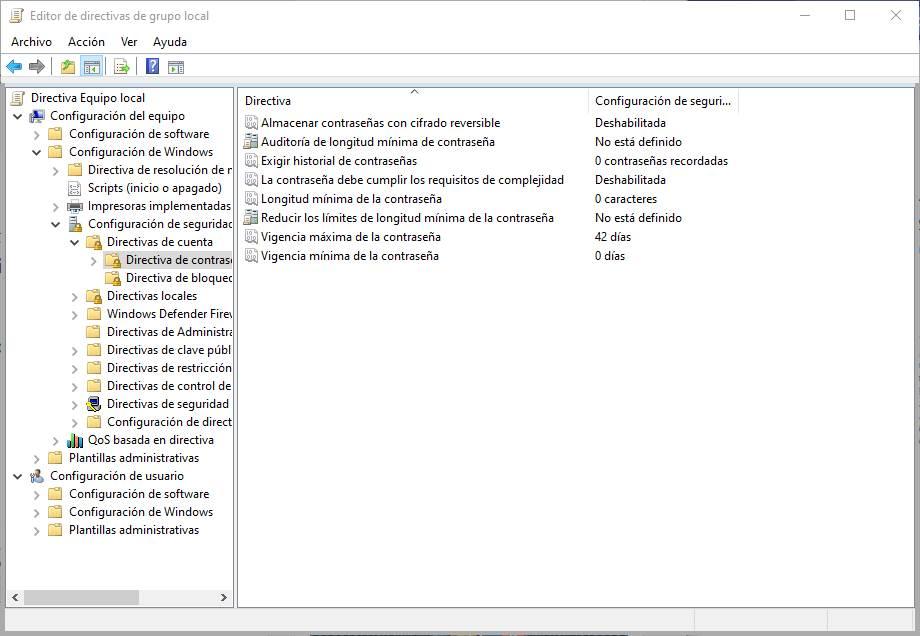
And here we are going to find the following options that we can configure:
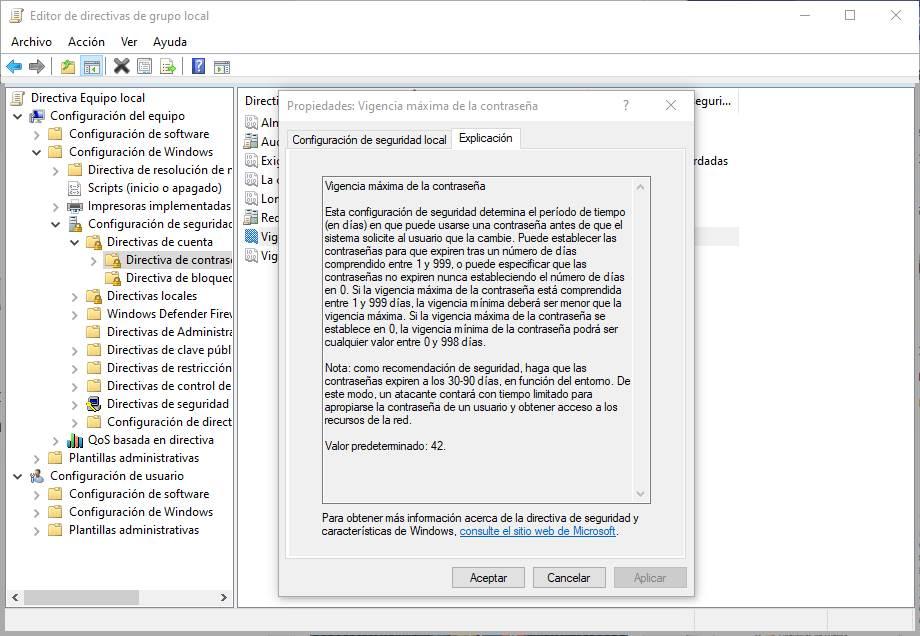
Maximum and minimum validity of the password . It allows us to indicate the minimum and maximum time that passwords can be used. This prevents being able to change the password too often, and also forces us to change it every certain number of days to avoid that, due to the passage of time, it may have been compromised. Values can range from 0 to 988 days, and the maximum time can never be less than the minimum.
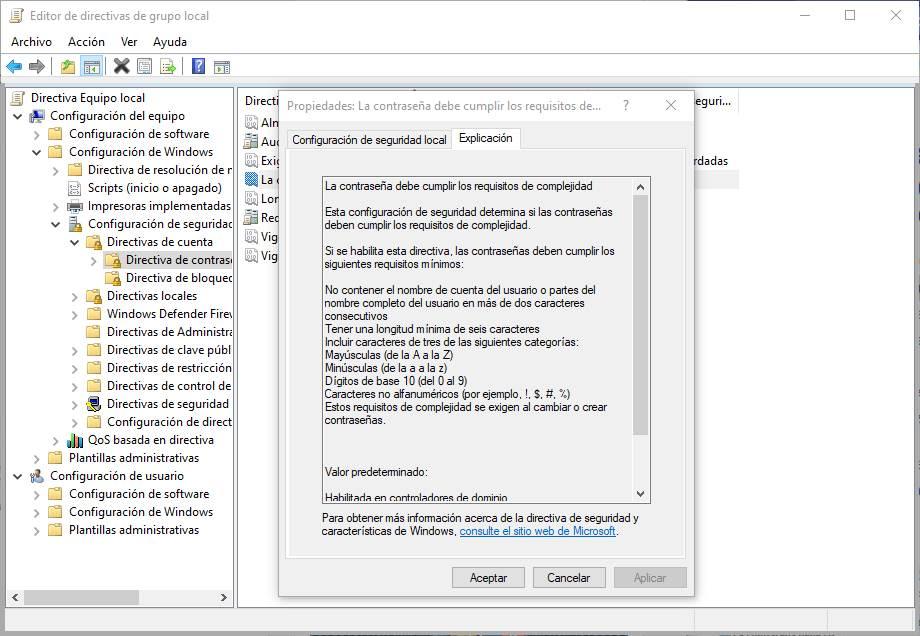
 The password must meet the complexity requirements . This directive will allow us to compel users to have their passwords comply with complexity requirements. The rules that a password must fulfill to be able to use it in Windows 10 if we enable this directive are:
The password must meet the complexity requirements . This directive will allow us to compel users to have their passwords comply with complexity requirements. The rules that a password must fulfill to be able to use it in Windows 10 if we enable this directive are:
- Do not contain the user’s account name or parts of the user’s full name in more than two consecutive characters.
- Be at least six characters long.
- Include characters from three of the following categories:
- Capital letters (from A to Z).
- Lowercase (from a to z).
- Base digits 10 (0 to 9).
- Non-alphanumeric characters (for example,!, $, #,%).
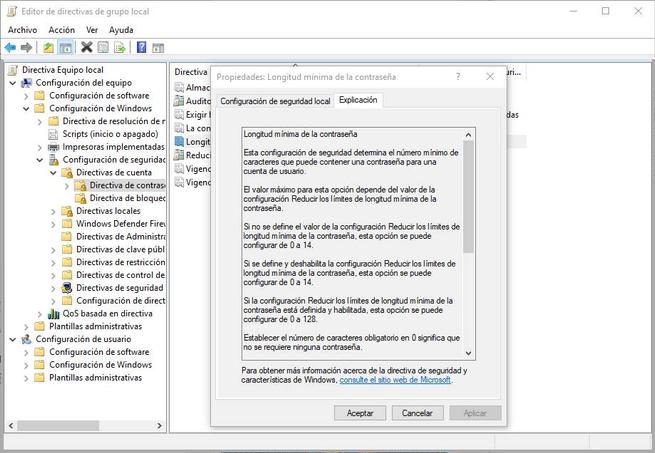
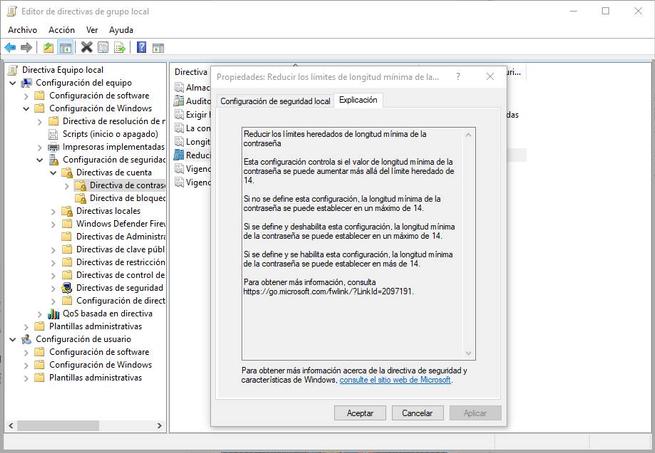
 Minimum password length . As its name indicates, this option allows us to specify the minimum number of characters that the password that we are going to establish in Windows must have. This directive allows us to configure by default a minimum of 14 characters. But, if we enable the ” Reduce the inherited minimum password length limits ” directive, we will be able to greatly extend this minimum password length limit, up to 128 characters.
Minimum password length . As its name indicates, this option allows us to specify the minimum number of characters that the password that we are going to establish in Windows must have. This directive allows us to configure by default a minimum of 14 characters. But, if we enable the ” Reduce the inherited minimum password length limits ” directive, we will be able to greatly extend this minimum password length limit, up to 128 characters.
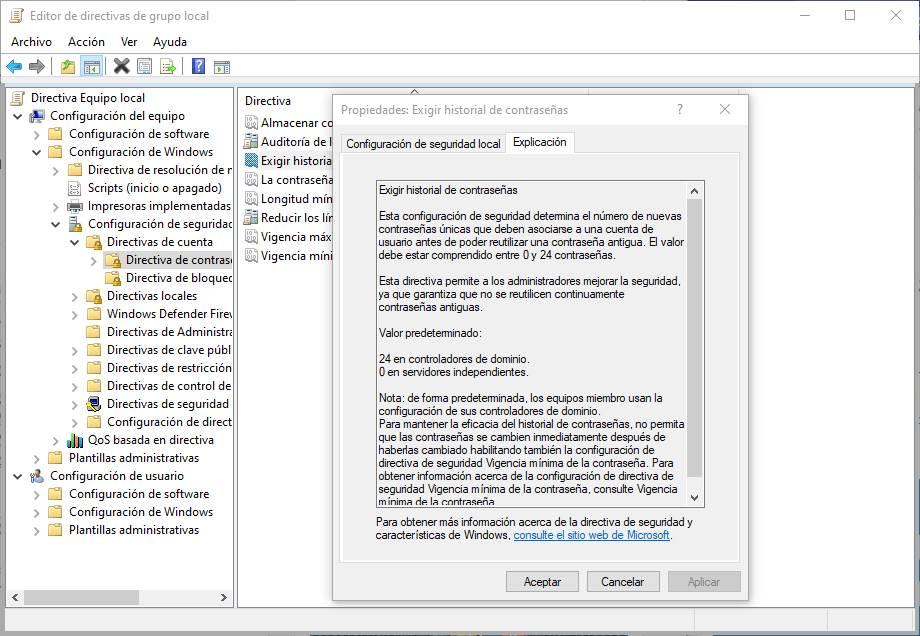
Require password history . This administrative policy allows us to specify the number of new unique passwords that must be used in an account before we can reuse an old password. We can configure this value between a minimum of 0 and a maximum of 24.
By configuring all these policies we will be able to be sure that we are using a strong password and we are correctly protecting our Windows user account.