Organizations that have a server, whether they are individuals or companies, want them to work well and be secure. Regarding information security, we could talk about the PCI DSS and ISO 27001 standards and regulations such as HIPAA and CMMC, which seek to strengthen the system as a form of defense against computer attacks. The reason why we act like this, is we want to implement more advanced security measures and protections to guarantee and improve our security. Its objective is to close those unnecessary doors that we have open through which cybercriminals could carry out their attacks and steal our data. In this article we are going to talk about how to secure a server thanks to automation.

What is securizing a server
Securing a server could be defined as the process of configuring the IT infrastructure. In this case we refer to servers, databases, networks, operating systems and applications. Our goal is to minimize the attack surface of our company, that is, the vectors and vulnerabilities that cybercriminals could use to gain access and control over our infrastructure. The goals we set out to achieve are improved safety, regulatory compliance and long-term cost savings.

Securing a server must include:
- Operating system configuration and user authentication . Here it would be important to disable the default accounts that are not used, create only the accounts that are needed, and establish specific user groups with specific rights.
- Remove or disable unnecessary services, applications, and network protocols . Some examples might be file and print sharing services and network and system administration tools.
- Configure appropriate access controls to resources . In this case it is important to limit read and write access permissions along with limiting the execution of system tools by system administrators.
Another thing to keep in mind is that IT security teams, when it comes to server hardening, have to make it an ongoing process where they have to maintain their organization’s compliance posture over time. . It may also be interesting to know the file systems that we can choose for a NAS server.
How to deal with securitization
Companies can have several servers, to which we have to add that each one of them has many configuration options. In relation to this, it becomes very complicated to manually perform a constant and complete reinforcement to maintain the security of those servers. In this regard, it should be noted that:
- A server securization project should start with an analysis of the impact hardening policies will have on the production infrastructure before we make any changes.
- We have to implement different hardening policies for different systems.
- Constant policy and infrastructure updates are going to affect your compliance posture.
One way to achieve this hardening of the server is to create a test environment that accurately reflects its complexity, simulating the traffic and the number of users on the network. The drawback is that it is a daunting task if done manually. In addition, there is a high probability of error, which could result in costly production downtime.
For this reason, a good solution is to resort to automation like the one we can achieve with the CalCom Hardening Suite . Thanks to it we can minimize this risk of inactivity. Once their software was installed on our servers, it would start a learning mode where they collected data from different sources on the machines. It would then analyze them to understand how the proposed policies will affect system operations.
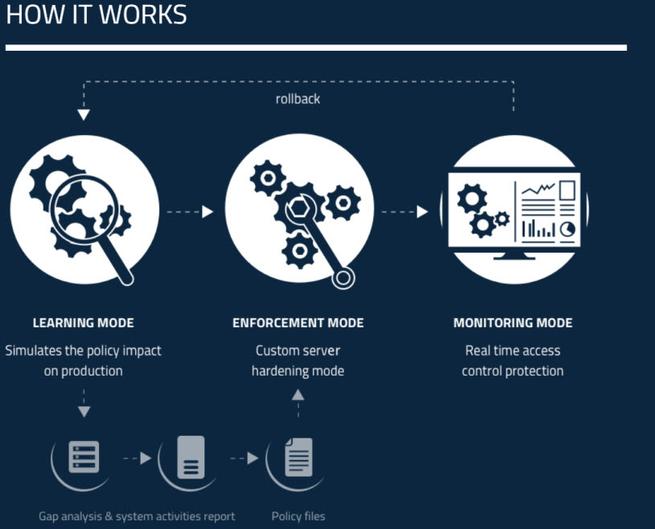
A resulting report is then produced listing each proposed policy, its desired value, and its current value. Then, based on this analysis, the solution creates the optimal policy action plan for each server to maximize policy compliance and prevent us from negatively impacting production.