Many sites ask us to log in or register to access certain information or online tools. In most cases, to make the process much faster, they allow us to register or log in with our Google, Facebook or Twitter account. However, this means having to grant certain permissions on our account information. Next, we are going to show how to know which applications have access to our Twitter account and how to eliminate third-party applications with access to our information .
When we connect a third-party application to our Twitter account, we are granting it access to certain information and to carry out certain actions on our own account, such as reading our tweets, seeing who we follow, updating our profile, accessing our messages and it is even possible that they can publish tweets in our name.

Therefore, we must be more cautious and be more careful with the permissions that we grant to certain applications when logging in through our Twitter account. The typical process is to access a website and when we want to connect to it, make use of a certain online tool or access certain information, we are asked to log in. In this case, next to the option to register, we are shown the option to Connect to Twitter or Login with Twitter.

By clicking on this option, we will be redirected to the social network website, where we will be asked to authorize the use of our account by that website or application. At that time, we can review all the permissions you request , but the truth is that in most cases, we usually accept without further ado.
Therefore, surely we have already given certain permissions to certain applications and we do not know very well what they are. Specifically, we can give read permissions , so they can access our profile information, tweets, account settings, etc. They can also be read and write permissions , so in addition to being able to access this information, they can update our profile information, publish or delete tweets, follow or stop following certain accounts, etc. Also, they may have read, write and direct message permissions, so, in addition to all of the above, applications with such permissions will also be able to send direct messages on our behalf, as well as see all the direct messages that we have sent or received through Twitter.
Therefore, we will show below the steps to follow to see which third-party applications have access to the information from our Twitter account.
Know which applications have access to your Twitter
Both from the browser on the desktop of our PC and from the Twitter app on the mobile we can see which applications have permissions on our account by following the steps shown below:
- We open our web browser and go to the Twitter site .
- We log in with our account.
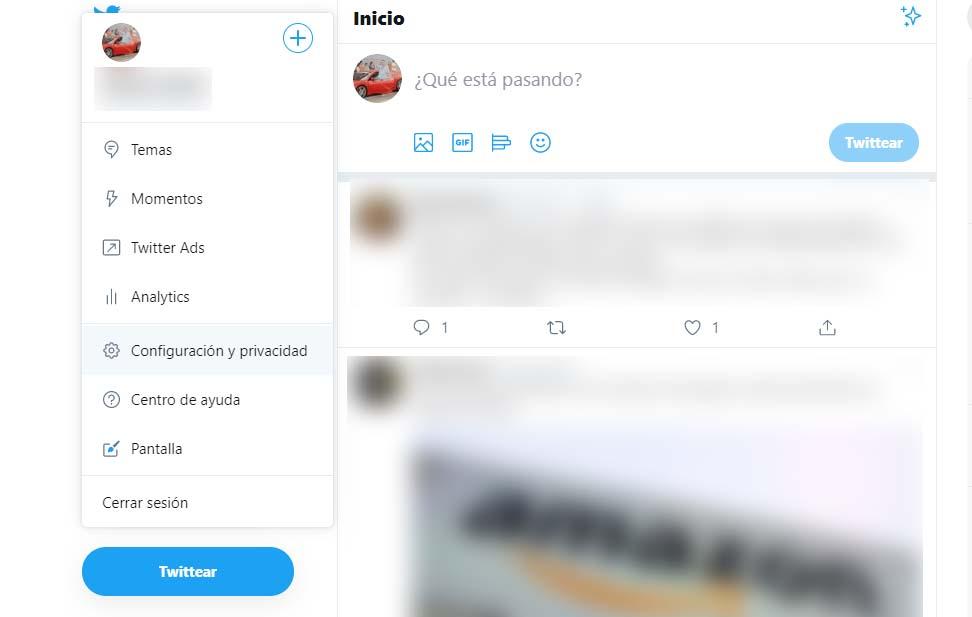
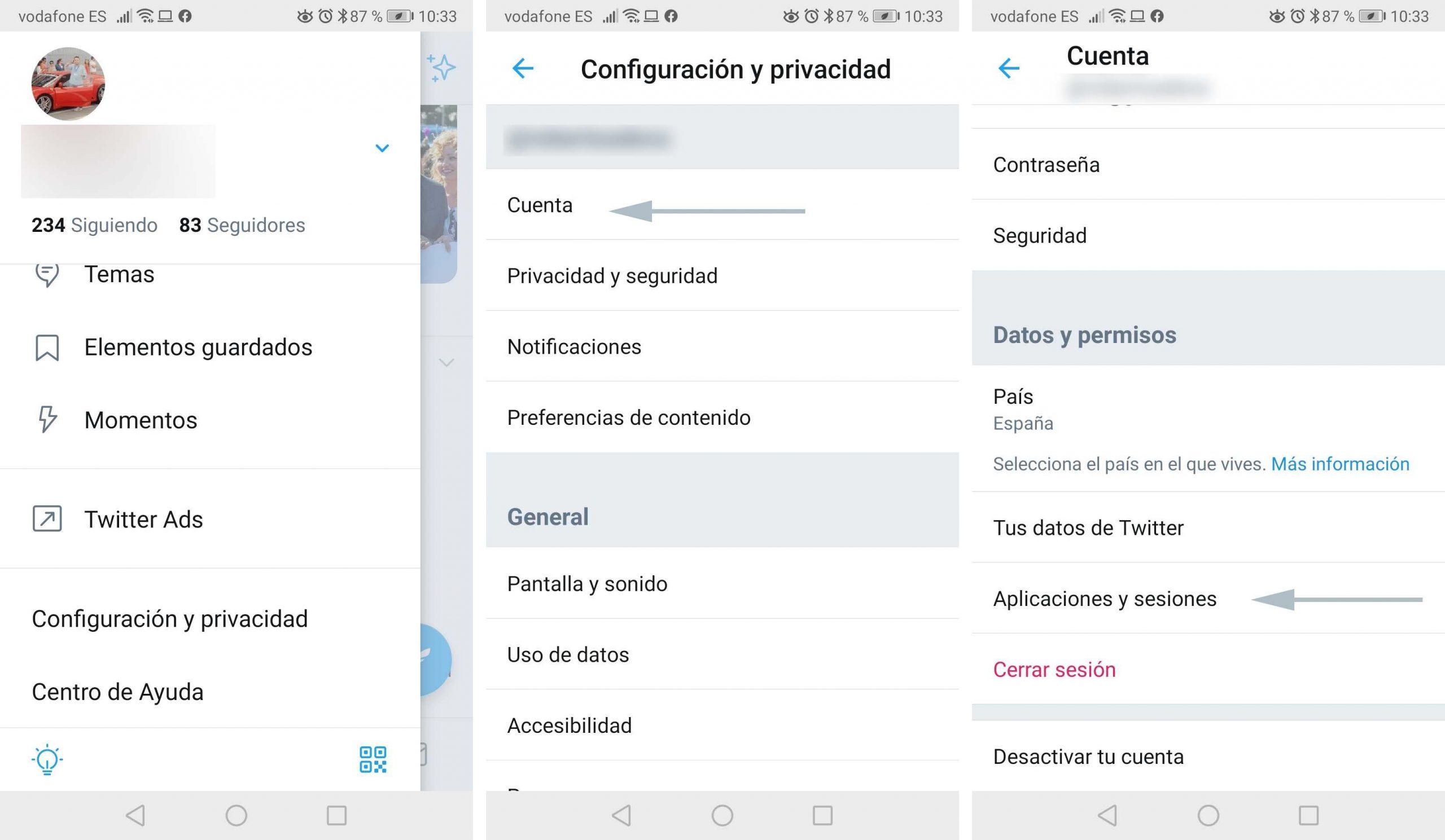
- From the menu button we access Settings and privacy.
- We select the Account option.
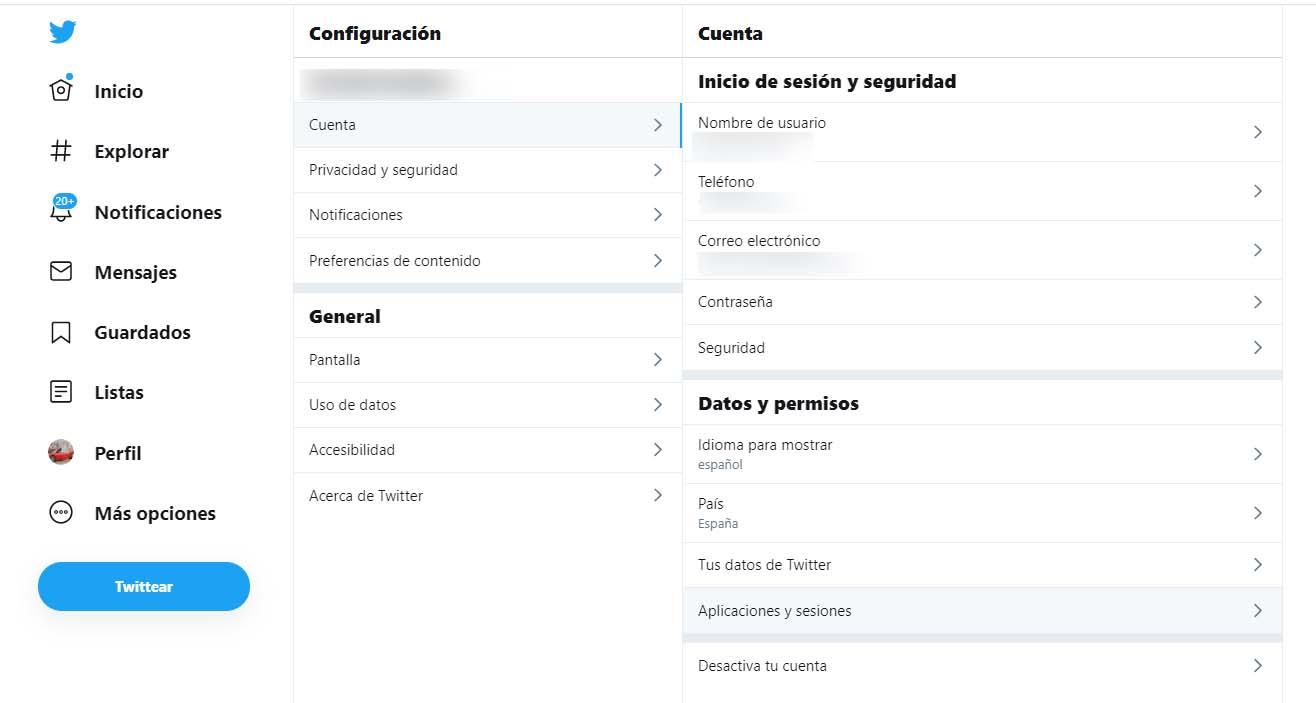
- Within the Data and permissions section, we click on the Applications and sessions option.
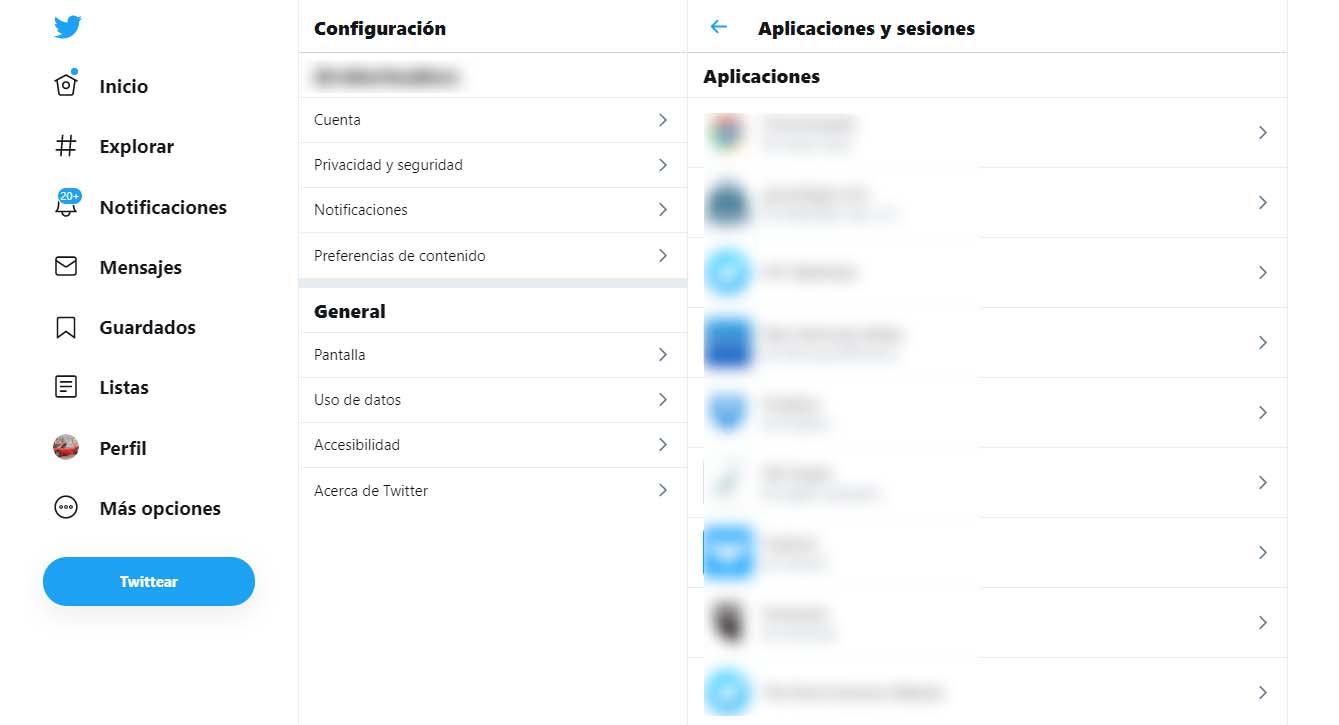
- Next, we will be shown a list with all the applications that have access to our Twitter account.
Following the same steps we can also know the applications with permissions on our Twitter account from the mobile:
Delete the applications with permissions on your account
From the list of applications that have permissions on our Twitter account, it is possible to see what type of permissions we have granted them. To do this, just click on any of them and then a page will appear showing the name of the application and the permissions we have given it, reading, writing and direct messages. In addition, we can also see the date on which we accept that this application had permissions on our information.
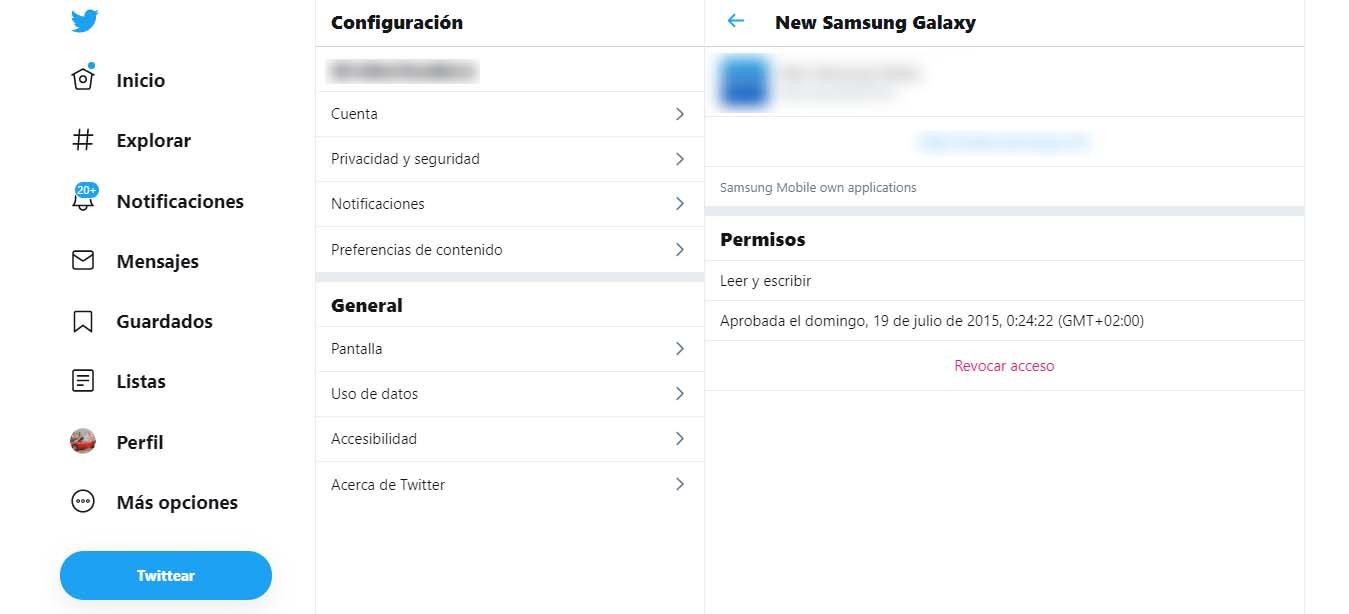
From there, it is from where we will be able to revoke or eliminate access to our information. To do this, simply click on the link or Revoke access option . Automatically, we will be removing the permissions we had given you. To remove these permissions to the other applications, all we have to do is go back to the list and go into each one of them to click on the Revoke access option.