Email is a service widely used by users on the Internet. There are many providers that offer us the possibility of sending and receiving e-mails. However, the truth is that it has also become a means of spreading malware and other threats. We can even have intruders inside that compromise our privacy. In this article we explain how to know if someone has entered our Outlook or Gmail account .
Hackers set their sights on email
It is a reality that we use email daily for everyday tasks such as registering for an online service, sending a document, receiving a response on a work issue, storing receipts for products that we have purchased online …

There are many uses that we can give to e-mail, since it also serves to save documents and files, use it to remember passwords, create a contact list, etc. But also all this means that if someone has access to our account we can have important privacy problems .
Cybercriminals set their sights on e-mail . They use different methods to steal information, passwords or infect computers. For example, Phishing is a widely used technique to get hold of our passwords and credentials. Also sneak malware through attachments.
If an intruder manages to enter our Gmail or Outlook account, we can suffer important consequences for our privacy. So we are going to see how we can detect it. We focus on these two providers since today they are the most popular in Spain.
How to detect intruders in our Gmail or Outlook account
First of all we are going to begin to explain how to know if there have been intruders in our Gmail account . For this we have to log in with our data. There are several clues that tell us if there may have been intruders or not. One of them is very fast and simple, since you simply have to go to the bottom right and there they will indicate the last activity of the account. Do we see something strange that does not fit? It is an indicative that shows us if there may have been intruders.
If we click on Details, a new window will open with more data. The date and time of the last logins appears, from which browser and which IP address. But also, if we click on Show details in any of the logins that appears, it will show us the operating system used.
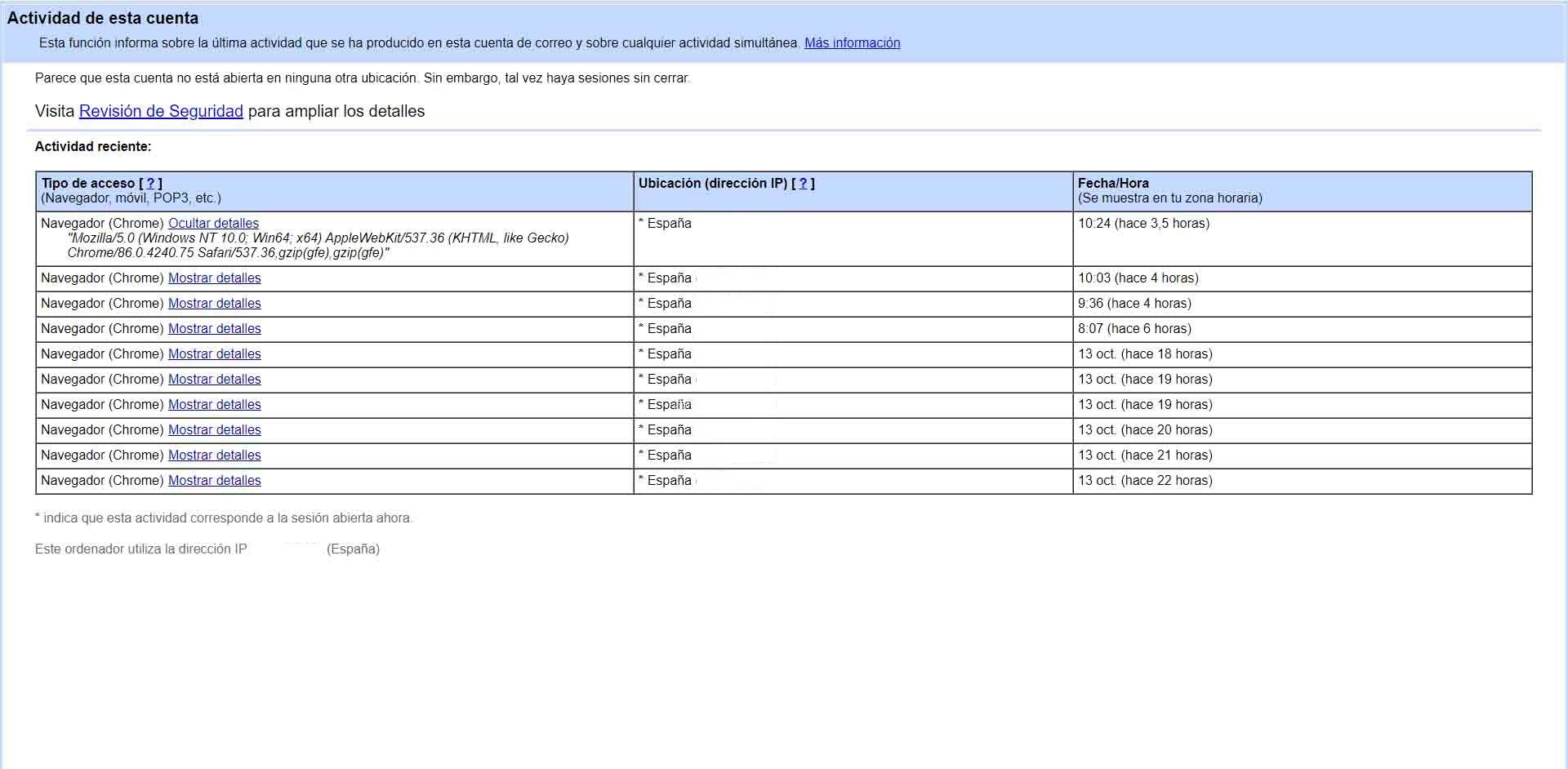
In case we find something strange it could mean that there are intruders. We must act as soon as possible to change the access password.
As for Outlook we have a similar option. Again we have to log into our account, go to the icon of our profile, top right, and enter My account. We go to the Security section (it will ask us for the password again) and we access the Login Activity (the first option). There we will see all the logins we have made, the location, IP address, device or browser.
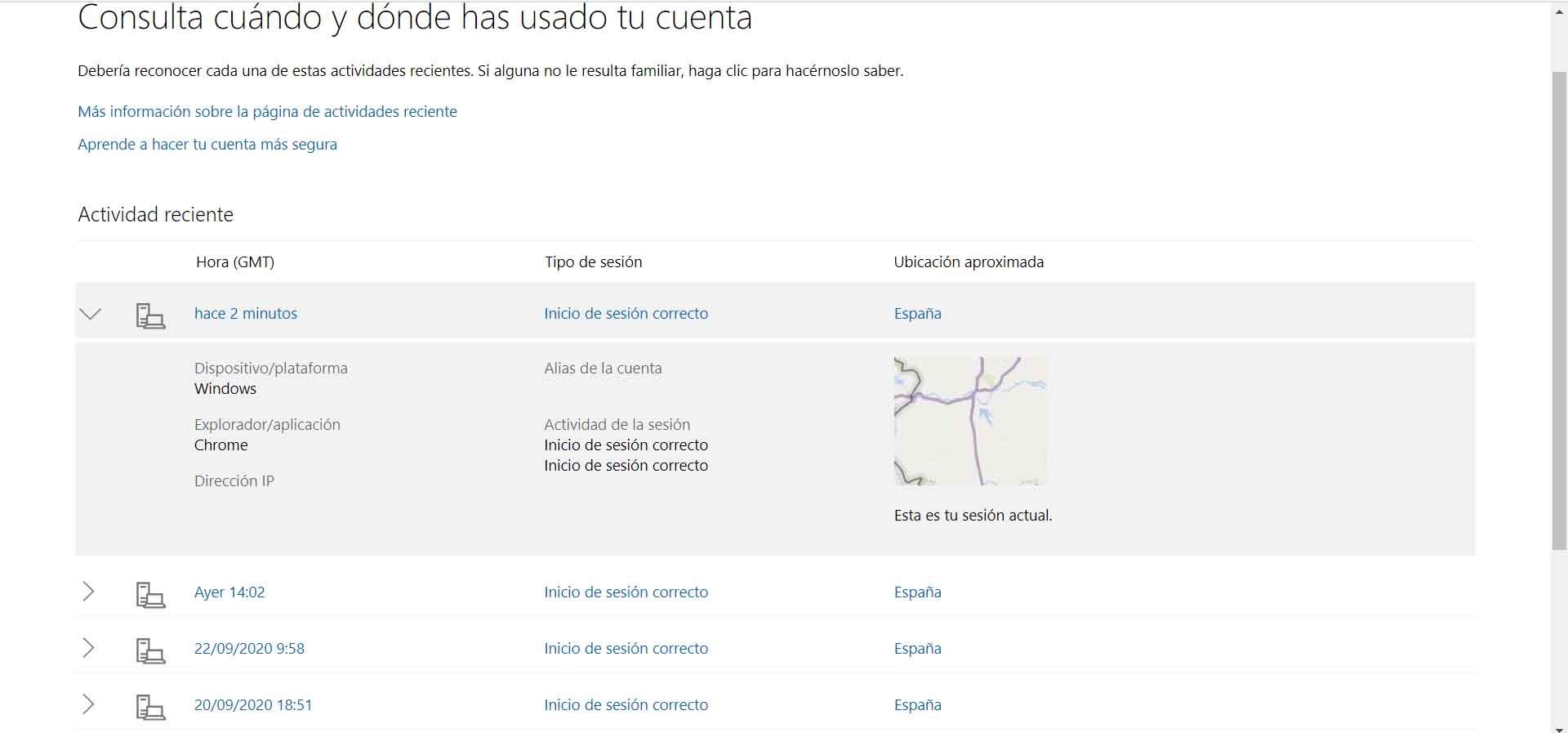
Once again, in case we notice something strange we must change the password of our account to ensure that there are no intruders.
Signs that indicate intruders in our mail
We have seen a method that we can use in Gmail and Outlook to see if someone has logged into our account without our knowledge. But there are different signs that can also indicate that there is something strange. These are the main ones:
- Read emails: if we see that we have emails that have been opened, it is a sign that someone has accessed our account in some way.
- E-mails disappear : one of the most typical signs is also when e-mails disappear. Let’s say that suddenly we see that some emails that we had stored have been deleted.
- Installed plugins: we have different options to add plugins in our account. If we see that we have something installed that has not been put by us, it could be a bad sign.
- Login alert: we can also receive an alert that someone has tried to log into our account or receive a two-step authentication code, a sign that someone has tried to enter.
How to avoid intruders in the mail
We are going to give some tips to avoid intruders in our email account. This can be applied to both Gmail and Outlook. They are simple recommendations to apply and that can protect us.
Use strong passwords
One essential is to use passwords that are strong and complex. They must contain letters (uppercase and lowercase), numbers, and other special symbols. All this in a random way, that is unique and also has a suitable length.
Two-step authentication
Additionally, these types of services allow two-step authentication . It is an extra barrier, a code that we can receive to log in when we enter from another computer, beyond the password.
Use official apps
Undoubtedly something very important is to only use applications that are official , safe and downloaded from legitimate sites. It is true that sometimes we can opt for third-party tools, but they are not always safe.
Avoid insecure networks
The networks to which we connect will ensure that our accounts are secure. You should avoid as much as possible logging into public Wi-Fi networks. In a pinch, good advice is to use VPN services to encrypt the connection.
Review information frequently
Finally, one more tip is to review the information frequently. This way we will have constant control and see if an intruder has been able to access.