
Hackers are constantly looking for new ways to trick users into carrying out their hacking attacks. And, for this, they usually resort to very popular, widespread and used file formats with which they can attack the largest possible number of users. In this way, HP Wolf Security researchers have just detected a new malware distribution campaign that takes advantage of the .ODT format to distribute malware in an undetectable way.
Hackers often use other file formats to carry out their attacks. For example, the most common are the PDF or the .BAT or .EXE executables. For this reason, finding ourselves with a campaign focused 100% on the ODT format is even more strange. The .ODT format is the OpenDocument text file format. Broadly speaking, it is the open equivalent of Word DOCX. This format is not only used in LibreOffice and OpenOffice, but all word processors, including Word, are capable of opening it. And by doing so, the user is automatically exposed.
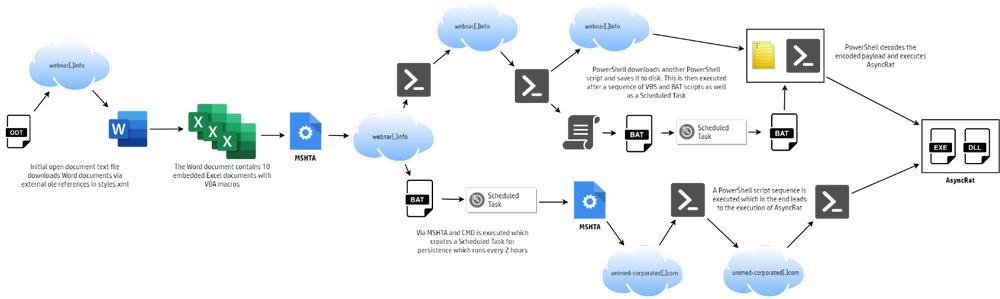
After an exhaustive analysis, samples of this malware have been detected on the network since the beginning of June 2022, but it was not until the beginning of July that a copy was uploaded to VirusTotal. To carry out this attack, the document targets various objects hosted on remote servers, but does so without resorting to macros . In this way, it evades all security measures of the system and antivirus and makes it much more difficult to detect the threat.
Instead of using the typical macro system, when the malicious document is opened, it targets more than 20 remotely linked OLE objects. The user must choose, yes, if he wants to download these objects to be able to update (in theory) the content of the document. If we download them, then several files are downloaded to our computer and executed. One of these files is an Excel sheet with hidden macros. And this is the one that finally triggers the infection when executing the macro: it installs the AsyncRAT Trojan on the PC .
avoid infection
As we can see, from the initial ODT document, until the infection is executed on the system, the process is quite complex, which shows that the hackers have gone to great lengths to avoid detection of their malware. And, to ensure reinfection, it has very aggressive persistence features.
The infection method used is very classic: a phishing email with the ODT attached . Since it is a harmless document, neither GMAIL nor antiviruses detect it as a threat. But, the moment we execute it, we are doomed. And it doesn’t matter if we open it with Office Word, LibreOffice Writer, or any other program.
If we have received this file by mail, and we have executed it on the PC, it is most likely that we are infected. and in that case what we have to do is analyze our PC with a good updated antivirus to detect and block the threat. And, in addition, be very careful with persistence, since it is very aggressive in this case.