
The need to protect our privacy has become one of the most important focuses of modern computing, and for this reason storage device manufacturers have long incorporated hardware encryption systems, so that users have it easier. when it comes to preventing unauthorized access to our data. But do you know how the hardware encryption of an SSD works ? In this article we are going to talk about it, we are going to tell you what advantages it has over software encryption, and of course we are going to tell you about the types of encryption there are.
When we talk about the technical specifications of an SSD many times compatibility with certain hardware encryption algorithms is mentioned, but it is quite likely that those names and acronyms do not tell most of the users much. Most people know that encryption is related to privacy and data protection, but in this article we are going to go a little further and explain it to you in a simple way so that you can reliably know what it is. capable your SSD when you buy it.
What is SSD encryption?

From large companies and public administrations to individuals, the desire to protect important personal and private data has become a necessity. To protect this data against unauthorized access or external attacks, encryption provides an extra layer of protection that will prevent intruders from accessing the data, so that even if a hacker accesses your computer or someone steals your hard drive external, will not be able to access your data.
To understand what encryption is in a simple way, we can understand it as a way to convert the information entered into a digital device into unreadable data blocks unless you have the specific encryption key. The more sophisticated the encryption process, the more unreadable the encrypted data will be, and vice versa, decryption will return the encrypted data to its original form so that it is readable again, which is why you should bear in mind that encrypting a storage device It also has some performance impact because the data must be decrypted before it can be used.
Hardware vs software encryption
As its name suggests, software encryption uses one or more software programs to encrypt the data on your storage drive. The first time an SSD is encrypted, a unique key is established and stored in the PC’s memory, and this in turn is encrypted with a user-defined passphrase. When the user types that phrase, the key is unlocked and access to the encrypted data is allowed, so in reality software encryption is something of an intermediary between the reading and writing of the data and the device.

When data is written to the drive, it is encrypted using the key before it is physically saved to disk, and when data is read, it is decrypted using the same key before presenting it to the user. This entails a considerable workload for the PC’s processor, since as the encryption is based on a program (which must be resident in memory), it is the CPU that is actually in charge of carrying out the workload of encryption and decryption. of the data.
Software encryption has two very clear disadvantages and an advantage that is also a disadvantage: the first disadvantage is that you depend on a program, and therefore without it you cannot access the data, so if there is a problem in he himself will have serious difficulties. The second downside is that if a hacker finds out your passphrase (just like finding out a password), they will be able to access all your data without restriction as a copy of the private key is kept on the storage device itself. Finally, the advantage is that the encryption and decryption performance is superior to that of the hardware since it depends on the CPU, but at the same time it is a disadvantage because it will reduce the performance of the PC by using its resources.
The units that use hardware-based encryption, meanwhile, we could say that they integrate this program into the unit itself, so they do not depend on the processor to perform the encryption and decryption tasks of the data. Self- Encrypting SSDs (SEDs) have a built-in chip that encrypts data before writing it and decrypts it before reading it directly from the NAND media. In this way, hardware encryption sits between the operating system and the system BIOS, making it much more secure than software encryption.
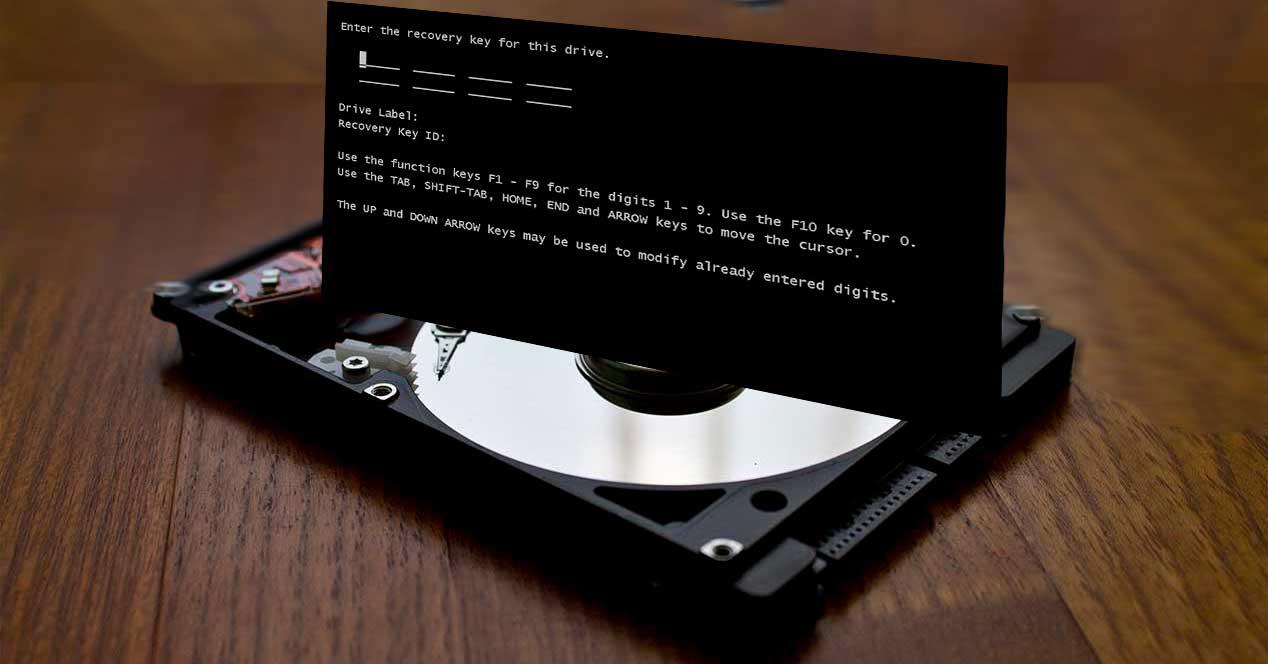
The first time the drive is encrypted, an encryption code is generated and saved to the SSD’s NAND Flash memory, and the first time the system is booted with the drive, a custom BIOS is loaded, prompting for the user’s passphrase. . Once entered, all content is decrypted and access to the operating system and user data is allowed.
What types of encryption are used on SSD?
As a general rule, in an SSD with a self-encrypting chip we will find two types, AES being the best known and most used. AES (Advanced Encryption Standard) is a symmetric encryption algorithm (this means that the encryption and decryption keys are the same) that divides the information into 128-bit blocks before encrypting them with a key that depends on the level AES encryption (for example, AES 256 bit means that the key has 256 bits, and obviously the larger the key the more complicated it will be to decrypt).
In fact, 256-bit AES encryption is an international standard that guarantees superior data protection and is even approved by the US government since it is considered literally indecipherable, which makes this standard the most robust that exists. .

And why is it indecipherable? As we have said, an AES-256 encryption uses a 256-bit private key; For each of these bits, the number of possible keys is doubled, that is, 256-bit encryption is the equivalent of two raised to 256 possibilities, or in other words, an absurdly high number of possible keys that even a super computer would take centuries to guess. But that’s not all, as each key bit has a different number of rounds, which is the procedure for converting from plain text to ciphertext; AES-256 has 14 rounds, so the chances of a hacker getting 14 times the correct 256-bit sequence are slim.
On the other hand we have the encryption based on TCG Opal 2.0 ; TCG is the international regulatory group that defines the hardware-based root of trust of interoperable computing platforms of trust, and that establishes Opal 2.0 as a protocol that can initialize, authenticate and manage encrypted SSDs by independent software vendors, that is, this allows data to be encrypted and decrypted by the SSD rather than the CPU when encryption is used by supported software such as solutions from Symantec, McAffee, and others.