Of all the security threats that we can find when browsing the Internet, Phishing is undoubtedly one of the worst. It is a method hackers use to steal passwords and take control of an account. With the passage of time, in addition, they have been perfecting the techniques to attack. In this article we are going to talk about what Cloning Phishing is . We are going to explain what it is and what you can do to avoid being a victim.
What is Cloning Phishing?

We can say that a Phishing attack is a strategy used by cybercriminals to defraud. For example, they may send an email containing a link to a malicious site, which appears to be a legitimate page. But when the victim clicks, they are actually entering a fake website, where their personal data is at risk.
Now, Phishing can have different variants . Attackers are constantly updated to achieve increased success. One of these options is what is known as Cloning Phishing. It is based on the cloning of previously sent emails. They will impersonate an official entity in this way.
What the attacker does is clone an email that the victim has previously received. This way, if you receive it again, it may not seem strange to you and you will end up clicking on some link, logging in or sending any type of data that you may request from them.
For example, let’s think about a social network that normally sends an email when we are tagged in a photo. It’s something we’re used to and we can click to see that photo. Now, what the attacker does is clone just that email. You are going to send an email containing something identical, saying for example that we have been tagged in an image.
But of course, that email is actually fake ; as soon as we click on a link we will end up on a fraudulent page and possibly the password of that social network will be stolen or something will be requested. It is a Phishing attack that is going to try to be a clone of a normal, legitimate email that we could receive at any time.
How to detect and avoid Clone Phishing
As you can see, cloning or clone phishing is more difficult to detect. You will not receive a sporadic message, without much sense, but you will receive something that could really be legitimate at any time. This makes us take even more precautions to prevent attacks and malware on our systems.
Analyze addresses and links
The first thing you can do is analyze very well the email address of the email you have received. If you suspect that it may be a scam but you see that it is really the same as a real e-mail, take a good look at that address. Sometimes a symbol, a letter or anything can vary and that is already a clue that tells you that you should not open anything that comes from that address.
You can also choose to analyze the links attached to it. There are pages like URLVoid or Sucuri that help detect dangerous links. Basically what you do is paste that URL that you have received and they use a database to determine if it may contain any threat or if there is nothing wrong with accessing it.
You must bear in mind that the latter is simply one more help. It could be a very recent cloning Phishing and the links do not yet appear in the databases and, therefore, those tools would not indicate to you that it is a scam and you could be in danger if you open it.

Avoid logging in from external links
This advice is to avoid problems with Cloning Phishing. It is important that you avoid logging in from external links that come to you through social networks, mail or any platform. It does not matter if it is an e-mail that you have received and you think is reliable, since you never really know if it could be a scam and it is better to be safe.
Ideally, you should log in by entering the website directly through the browser or by accessing it through an application. This way you will avoid entering from a link that may be false and could lead to a scam without you being aware of it and putting your passwords and personal data at risk.
Do not download suspicious files
Another recommendation is not to download any file or document that arrives through an email that may be suspicious. Hackers can use this strategy to sneak viruses and malware in general. Think that simply through a text document or an image could contain malicious software.
Therefore, avoid downloading files if you do not know if they are really reliable. This will help you to be more protected from malware and will reduce the risk of your equipment malfunctioning or your personal data being exposed.
Protect email address
If you want to avoid receiving emails that could be dangerous, such as Cloning Phishing, a good idea is to protect your email address . What can you do? For example, avoid exposing the address in public forums or comments on web pages that can be seen by anyone.
If you need to register on pages that may not be secure, a good idea is to use disposable emails. In this way you will avoid using the main one and you will not expose your personal data more than necessary. There are many options on the Internet.
Keep your computer safe
On the other hand, keeping your computer safe will also help you avoid problems with Cloning Phishing and other similar threats. Use a good antivirus , such as Windows Defender or Avast. This type of program will notify you in case you download any malware or something that could compromise security.
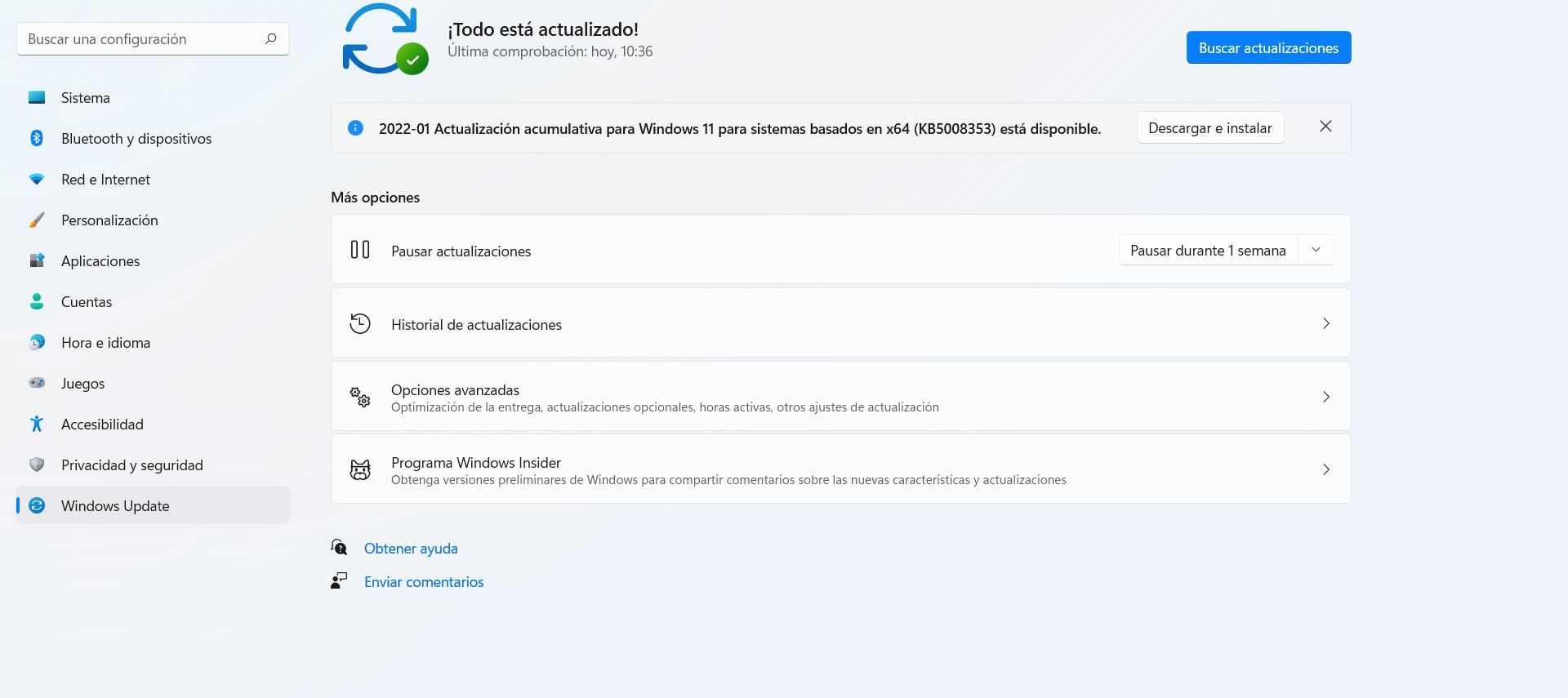
Likewise, it is important to keep everything up to date . In the case of Windows, to update the operating system you can go to Start, Settings and Windows Update. In this way you will always have the latest version available and you will be able to correct certain errors that may appear and that could compromise your privacy.
This is something you should apply no matter what kind of operating system you are using. Always update any program you use and thus avoid security problems that may affect you.
In short, as you can see, cloning phishing is a major problem that can leave your personal data exposed on the network. It is essential that you take measures to detect it and prevent it from affecting your security and privacy. Have a good antivirus, keep everything updated, but especially keep common sense and don’t make mistakes.