2021 is not being the best year for Windows security. Every so often a new security flaw appears in the operating system that jeopardizes the security of all users, flaws that, by the way, are not solved until several weeks later, when the new Patch Tuesday hits. And, in case Microsoft had little with the security problems of the printers, now a new security flaw of the most worrying has been added: HiveNightmare.
HiveNightmare (name that has been assigned to this vulnerability) is a security flaw present in all versions of Windows 10 from 1809, and in Windows 11. Thanks to this flaw, any user, even without administrator permissions, can access to critical system files, such as SAM, SYSTEM and SECURITY . By doing so, this user could gain the highest level of privileges within the Microsoft operating system: SYSTEM. And, with it, you can literally do whatever you want on your PC, even run random code in your PC’s memory, or change Windows programs.
This bug is very similar to Sequoia , a bug that was released the same day but mainly affects Linux users.
Microsoft, at the moment, has not given much information about this new security problem that affects all its modern Windows. However, thanks to the researchers, we can know a trick to see if we are affected by this failure or, if not, if our PC is already protected.
Test if Windows is vulnerable to HiveNightmare
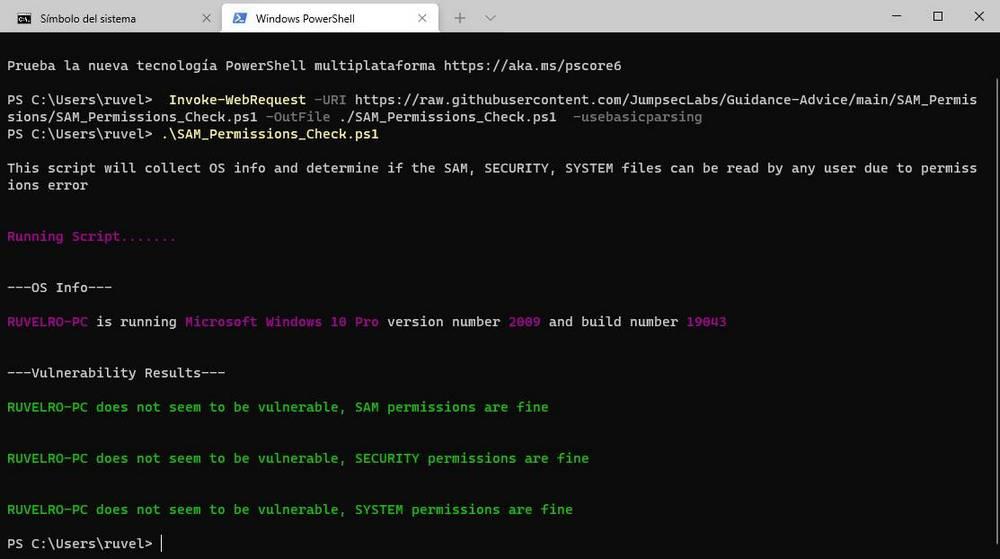
In GitHub we can find a simple script thanks to which we will be able to check the permissions of the SAM, SYSTEM and SECURITY files with a couple of PowerShell commands. To do this, the first thing we must do is open a Windows advanced console window, with administrator permissions (this is very important) and execute the following command:
Invoke-WebRequest -URI https://raw.githubusercontent.com/JumpsecLabs/Guidance-Advice/main/SAM_Permissions/SAM_Permissions_Check.ps1 -OutFile ./SAM_Permissions_Check.ps1 -usebasicparsing
This command will allow us to download from PowerShell the script ” SAM_Permissions_Check.ps1 ” from the GitHub servers. The download only takes a few moments, and at the end we will simply have to execute the following:
.SAM_Permissions_Check.ps1
The script will be in charge of analyzing our PC and will show us if our PC is vulnerable (marking the affected files in red) or if we are protected (marking them in green).
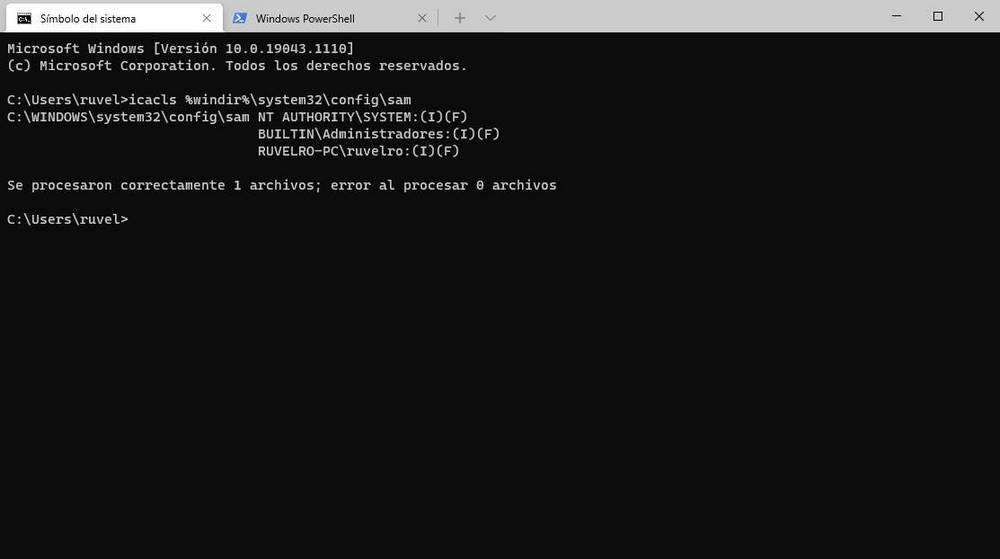
We can also test it from CMD, if we don’t like using PowerShell. To do this, we simply have to open a Windows console window and execute the following command in it:
icacls %windir%/system32/config/sam
If the output shows a message like “BUILTINUsers: (I) (RX)”, then we are in danger. Otherwise, our PC will be protected.
Is your PC affected? Protect yourself
If your PC is protected, then you no longer have to worry about anything. On the contrary, if it is in danger, it is necessary to protect ourselves if we do not want to continue taking risks. To do this, what we must do is open a CMD window, with administrator permissions, and execute the following commands in it:
icacls %windir%/system32/config/*.* /inheritance:e vssadmin delete shadows /for=c: /Quiet vssadmin list shadows
The first command activates ACL interheritance, the second clears the shadow copies from the system, and the third checks that there are indeed no shadow copies on the system.
Now we are protected until Microsoft definitively corrects this serious problem in Windows.