The Internet is a dangerous place if you don’t know how to navigate correctly. There are many programs that are used to protect against all these threats such as antivirus , but the truth is that sometimes they can give more problems than solutions. Apple integrates within macOS a firewall system called Firewall that controls all incoming and outgoing connections to your Mac. In this article we explain what it is and how you can configure it.
What you should know about this system
The Firewall of a Mac is a really complex system that aims to avoid all the threats that can be found. Next, we will tell you everything you need to know about this system that is owned by the Cupertino company itself.

A native protection system
A native firewall is integrated into the macOS operating system, which is really useful to be able to be protected at all times. It can be said that this is a firewall system to all the connections that enter and leave the Mac to be able to monitor all the information that is going to pass through . This is something that is totally unrelated to the applications you have installed on your computer since they do a block monitoring of all these constants. It can be said that it is the most sophisticated control system that exists to be fully protected.
The most classic simile is that of a highway in which different vehicles that are data packets circulate. All of these want to get in and out of your Mac that can be considered the city. But to prevent an unwanted vehicle from entering, such as criminals, there are police controls for monitoring. This is the main function of the firewall: to review in detail all the connections and decide which one continues to circulate and which one does not. It must be borne in mind that the internet is a very wide world and there are many threats that can be found through these communication channels . But keep in mind that this system ends up isolating all these applications to act independently.

What can you protect yourself from
As we have commented previously, there are many threats that can be found on the internet. The firewall is largely responsible for preventing data packets that are harmful to the device from entering. The most common is for example when a simple download is made in macOS. If they are made from web pages that are not trusted, they may be programs that are totally false and that try to mask malware or ransomware that aim to hijack your computer.
Through this firewall system, the system is able to know exactly what is being downloaded. When it detects a threat, it will block it and leave it in quarantine waiting for your manual decision. In addition to these downloads, it is also applied individually to each of the applications as we have previously commented that they require internet downloads. The very installation of an application can be blocked by this system if it is seen to be infected in any way. To this is also added the fact of accessing web pages that are not within the secure database. The latter is important, since they always have to be updated to have the best possible protection.
Does it replace other antivirus?
There are many antiviruses that can be found in the market and whose mission is to prevent all these threats from entering the Mac itself. But the truth is that the quality of the program and the database must always prevail. On many occasions there are some antivirus that are free and that can give many more problems than solutions to all users. We have seen numerous data leaks and also antivirus that have been a virus when installed.
This makes the macOS firewall one of the best antivirus that can be found for the Mac itself. Being developed by Apple itself, it makes it possible to integrate perfectly with the operating system of course. It makes it the best option to be able to block all incoming connections by having the necessary permissions to do so. In conclusion, the firewall can perfectly replace a traditional antivirus.

Firewall settings on macOS
In order to achieve maximum protection and avoid having problems with this integrated program, it is important to know how to configure it perfectly. Below we detail everything you need to know about the configurations that can be made in the native firewall options.
Deactivating it is possible
In the event that there is some kind of problem with the firewall protection system, it can always be disabled. It is true that care must be taken when doing this operation as the Mac would be completely unprotected. You will sweep them down and any file can be downloaded and installed. If you are a person who usually visits pages that are completely safe or download files or documents that are not completely trustworthy, it is highly recommended to deactivate it. There is also the case in which you do not have enough knowledge to understand if something is a threat to the Mac or not.
If you also want to do without this security system for your Mac, the way to deactivate it is quite simple. But the truth is that when you have finished doing what you needed with the firewall disabled, you must re-enable it by following the same steps. To do so, you simply have to follow the following steps:
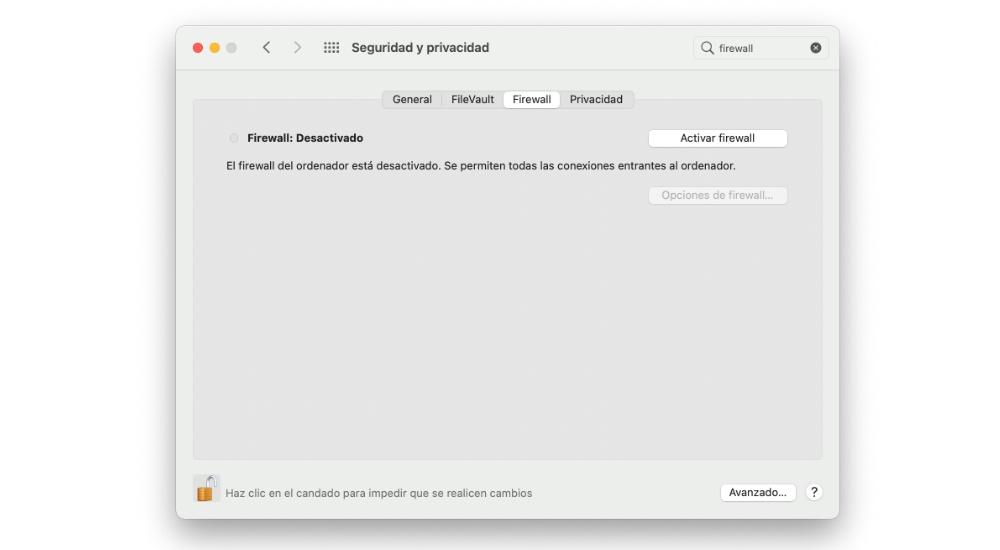
- Enter the System Preferences.
- Click on ‘Security and Privacy’.
- In the upper tabs click on ‘Firewall’.
- Click on the padlock at the bottom and enter your password.
- Click on ‘Disable firewall’.
Add exceptions
Beyond completely disabling the Mac’s firewall, you can choose to add exceptions. This can be considered an access whitelist so that some applications or services do not have to go through this service. This will make them work without any type of filter on the connections to be made. As we have commented previously, the macOS firewall makes isolated controls for different applications and this is of important relevance. By applying this filter you will be eliminating a check point in the incoming and outgoing connections and it is obviously a significant danger. Keep in mind that it is relevant to carefully choose the applications that you enter in this list. To be able to configure it, you simply have to follow the following steps:
- Enter the System Preferences.
- Click Security & Privacy.
- In the upper tabs click on ‘Firewall’.
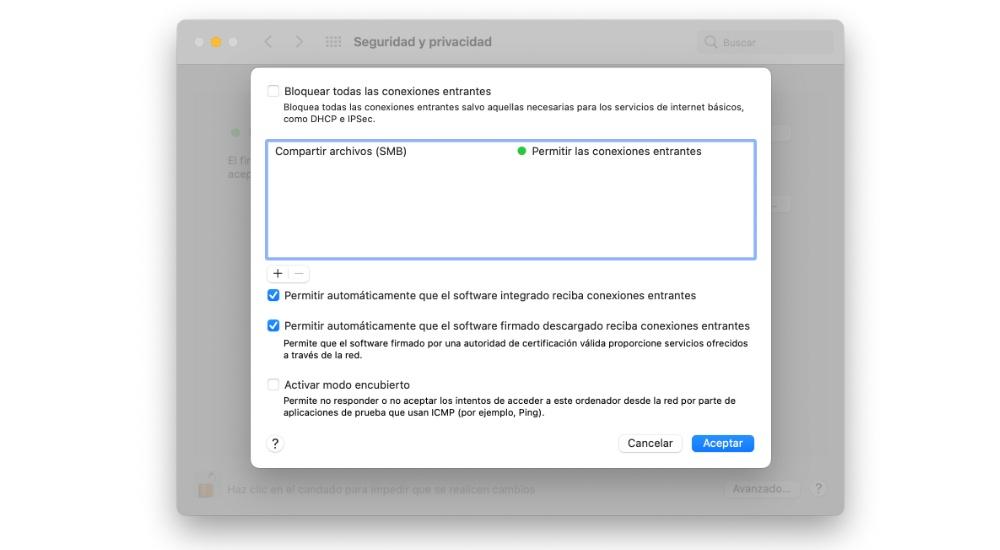
- Access Firewall Options.
- Click the + button and select an item from the list to be whitelisted.
In this same list you can also eliminate all these exceptions with the button – hovering over the specific exception you have. It is important to constantly carry out a thorough review of this entire list in order to avoid having an unwanted application at all times.
Other important options
Beyond everything we have discussed above, you can find other important options to be able to have maximum customization. To be able to find all these characteristics to customize it, you must follow the steps that we have previously commented until you reach the “Firewall Options” section. Beyond the exceptions mentioned above you can also find the following activatable options:
- Block all incoming connections . With this option you can prevent the entry of all incoming connections with different exceptions. These include basic internet services such as DHCPs and IPSec. This makes the Mac a true bunker against all downloads. This can make your Mac unusable, unable to download or install external applications.
- Activate covert mode. Activating this Firewall option would not accept attempts to access from other servers. This is something very typical that can be achieved by doing a simple ping. This will ultimately prevent incoming connections of this style from being able to enter.
- Automatically allow embedded software to receive incoming connections. With this option, all applications that have been developed by Apple will not have to undergo an exhaustive control of their connections. This is logical since Apple itself fully trusts its development and knows that they do not have any malicious data packages. That is why it is always activated by default but can always be deactivated.
Common Firewall Problems on Mac
It can be inferred that the macOS firewall is undoubtedly a very positive thing to always have on. But the truth is that sometimes it can give different problems to the user that forces them to have it deactivated. We will explain them to you in detail below.
Unable to install applications
As we have previously commented, the installations to be carried out on a Mac must go through the firmware. There are some applications that will never be installed because they are misinterpreted as unsafe. But not because they are going to do something harmful to your computer, but because it does not have the appropriate standards. By this we mean that developers do not sign some programs, especially when they are not official programs with a company behind them.
When trying to install, you may get an error message that cancels the installation itself. This can be really annoying and is mainly the fault of the firmware, which ends up blocking them when going through the checkpoint corresponding to this type of connection request. The only solution that is proposed to carry out the installation is to always deactivate the firmware, but always knowing that the application to be installed is of your full confidence.

Problems with Internet
The firmware controls all input connections to the Mac, that is, all internet connections. There are some applications that make use of this internet system to be able to be constantly connected to the network to be able to exchange data constantly. These connections can be interrupted due to the firmware itself and cause them to not work properly. That is why this is one of the most common problems that can occur with the firmware itself.
Browsers are undoubtedly the main gateway to the internet. If you want to access websites that are not trusted, the firmware will block all access. This is a serious problem since sometimes some pages that are trusted are detected as genuine threats. This can happen especially with official government websites that are detected as genuine threats. That is why you should always be careful in this regard and if you have this problem, disable the protection momentarily. This can also happen with remote control programs where input and output connections are used simultaneously. Sometimes they are detected as threats and are blocked preventing their use. That is why no protection program is 100% perfect, always having to resort to logic.