To avoid falling into the clutches of hackers and malware in general, it is necessary to install an antivirus on our computer. This program is responsible for analyzing the security of the PC and controlling everything that passes through it, being able to detect threats before they manage to infect our computer. However, we must be careful when choosing which antivirus to trust, since what initially promises to protect us, is likely to actually open the door to many other threats. So are the fake antivirus.

What are fake antivirus and how to avoid them
A fake antivirus, or rogue, is a program designed to trick the user into thinking that his computer is in danger and that he is capable of cleaning it from all kinds of threats. It is a program that seeks to supplant conventional antivirus (such as Windows Defender , Kaspersky, Avast or McAfee, for example) to leave the victim’s computer unprotected and be able to take control of it.
There are several types of rogue antivirus, and each one tries to fool users in a different way.
Programs that are installed on the PC

This is the least common type, but the most dangerous that we can find. It is easy to see it as part of the “adware” that is included in the installers of many programs. What they generally do is run on the computer and pretend to be scanning it. At the terminal, they tell us that we have a massive infection of viruses, Trojans and errors, and help us to solve everything. Yes, paying.
The purpose of these programs is that we pay a license to clean and repair the computer. If we don’t, we will be seeing error messages and warnings about massive malware infection on the PC all the time. If we pay, in addition to losing money, hackers will take over our payment method.
The best way to avoid these types of threats is to pay attention to the installers when we are going to install a program on the PC. In addition, we must also avoid downloading any program that a dubious website recommends to us.
Fake websites and fake online scanners

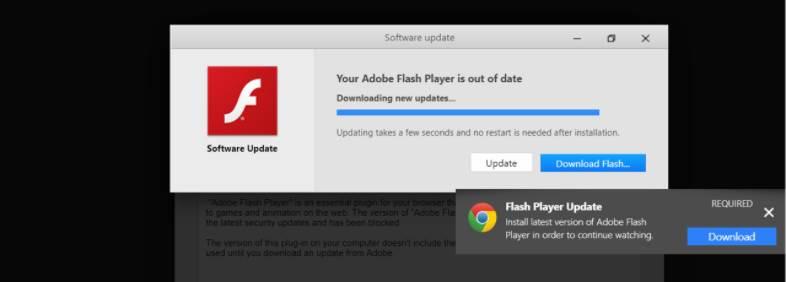
On the other hand, for example, we have fake websites that pose as antivirus scanners . When we enter a page we can see a message that tells us that our computer is infected by tens, or thousands, of viruses and that we must rely on a specific antivirus to disinfect the PC. This type of malicious websites (also known by the term “malvertisements”) what they seek is to instill fear on the user. And, as a result of that fear, deceive him.
The objective of these types of ads can be very varied. For example, they can trick us into downloading and installing a program that is supposed to clean the computer. Or they can ask us for the card data to pay for a supposed license to clean the computer, and this data ends up in the hands of hackers.
The best way to protect ourselves from this type of fake antivirus is to ignore the ads that appear when visiting the websites. Luckily, nowadays it is already rare to find this type of website, but the pirates are betting on other types of techniques with which to deceive, such as hijacking the browser.
Pop-ups that “hijack” the browser
This is a more modern and common method of trying to fool users with their computer security. Some websites take advantage of small JavaScript tricks to hijack the browser , block the computer and display a message stating that viruses have been detected on the PC and that we must clean up.
They generally use the name of Google or Microsoft to try to deceive users, and make them call a phone number (paid) from which they continue with the scam. If we call they will try to get more information about us, install remote control software and take control of our PC. They will also get hold of our bank details and all the files we have on our PC.
It is easy to come across these types of ads by following links posted on social media. In addition, either they do not have a close button, or they have a false button that, when we click on it, takes us to another website controlled by pirates from which to download, for example, a fake antivirus in the form of a program.
What to do if we have a fake antivirus installed
The best way to avoid falling into the clutches of this type of malware is to ignore it . If we see a message on a website, or a banner, in which we are told that we are totally infected by malicious software, simply bypassing it, closing the website and going to another site, we will be protected. As long as we do not follow the links in these advertisements, or download anything, or enter personal data, we will not have to worry.
The problems come when the infection has already taken place. If the fake antivirus has reached our PC, eliminating it can be complicated. It may have been hidden in the computer in many ways. For example, it may be injected into Chrome in the form of a bogus extension . Or we may find it installed on the system as one more program. It can even appear in the system tray, along with our personal antivirus (which, if it has not detected it, we should still think about changing).
Some of the symptoms that can make us suspect a possible infection are:
- The web browser is hijacked, it is not updated and it redirects us to websites that we do not want to visit.
- The PC is much slower than normal.
- Many pop-up windows appear on the PC. Many of them with virus and error messages.
- The background of the PC changes randomly.
- We cannot visit antivirus websites or install security programs.
Be that as it may, the first thing we must do to try to eliminate the infection is to restart the PC in safe mode. From there, the malware will not load at the start of the system as it is not signed by Microsoft, and we can eradicate it without problems. We can try to uninstall it from the list of programs, or scan the PC with an anti-malware, such as Malwarebytes, to detect the threat and delete it from the system.
If this is hidden in the browser, then we must restore all its settings to factory settings and start from scratch to prevent it from continuing to take control of the PC.
Tips to protect ourselves from fake antivirus
We have seen before how to mitigate infections from the most common types of rogue antivirus. But, in addition to them, it is advisable to follow some more tips that will help us to be better protected and reduce the probability of ending up in the clutches of these pirates:
- Update software and programs . We must update Windows, the most critical programs (such as the browser) and other programs used by hackers, such as PDF or Java readers.
- Uninstall outdated programs . If we have a program that is no longer supported, and that can be used by hackers, such as Flash, we must delete it.
- Install a good antivirus and keep it updated . If we have the PC protected, the security software will detect the threat before infecting the PC.
- Use common sense when navigating . We must navigate known and reliable websites, avoiding suspicious ads and links from social networks.
- Never open attachments in emails . SPAM is one of the main distribution channels for malware.