In a report on what happens after a new software vulnerability is discovered. shows us how responsible vulnerability disclosure and exploit development should be done. Therefore, how that vulnerability disclosure is made relative to the time they are made public can make it more beneficial to the attacker or defender. Today, security researchers looking for vulnerabilities do a very important job. Thanks to them, security gaps are found that can be patched before they are used by cybercriminals. For this reason, these researchers create exploits that show that this security flaw exists.
The problem is that, as soon as these vulnerabilities or exploits are made public, depending on the time frame we give, they can help IT administrators more to give them time to fix all the failures in their infrastructure, or benefit cybercriminals to exploit that security flaw that was just discovered.

Disclosure of vulnerabilities and exploits over time
In a joint investigation carried out by Kenna Security and the Cyentia Institute , they analyzed how time affects the disclosure of vulnerabilities or exploits, and when it benefits the attacker or the defender the most. Thus, they examined how these common practices used by security researchers can affect the overall security of corporate IT networks. Depending on when they release their investigation findings, they can negatively or positively affect the safety of our companies.
In the report, 473 vulnerabilities that had been publicly exploited were analyzed. Additionally, it was found that disclosing vulnerabilities before a patch is available does not typically create a sense of urgency among companies to fix that issue. According to Ed Bellis, chief technology officer for Kenna Security, research shows that the timing of exploit code publication can shift the balance in favor of attackers or defenders.
The research also reveals that there are periods of time when attackers have momentum versus defenders, regardless of when a patch is released. Sometimes, some companies do not have time to install the patch before cybercriminals carry out their attack. The research team for each vulnerability traced its life cycle over a period of 15 months. Here’s a breakdown of all the sequences observed in the vulnerability life cycle. Thus, we see from when it was discovered until when it was finally exploited.
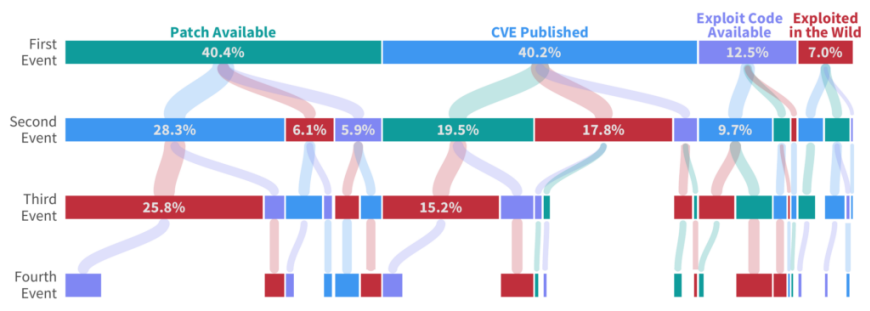
Here it was observed that only 16% of the CVEs studied followed the most common sequence of reserved, patched, scanned, published and exploited. Other conclusions were also drawn from the research, such as:
- 60% of the vulnerabilities have a patch before the official publication of the CVE and increase to 80% after a few days.
- 80% of vulnerabilities are detected in an active environment within two days of the patch release.
When do the attackers get the upper hand?
In terms of how often the exploit code is released before a patch is released, it happened about 24% of the time. Furthermore, 10% of the exploits occurred before a patch was available to fix it. In 70% of the CVEs exploited, it should be noted that the exploitation code is prior to the exploitation.
Just because a patch is available does not mean that it will be used. This is because companies have a list of open vulnerabilities and are solving them to the best of their ability. On the other hand, just because the exploit is available does not mean that attackers use it immediately. It should also be noted that there are periods of time, in which cybercriminals can deploy more attacks than IT administrators can patch.
Research by Kenna Security and the Cyentia Institute revealed that when an exploit code is released , attackers gain an average 47-day lead on their targets. Another thing to keep in mind is that when exploits are released before patches, security teams will need more time. Thus, addressing the problem will be more complex even after the patch is released. In the 15-month study, attackers were found to gain the upper hand 60% of the time .
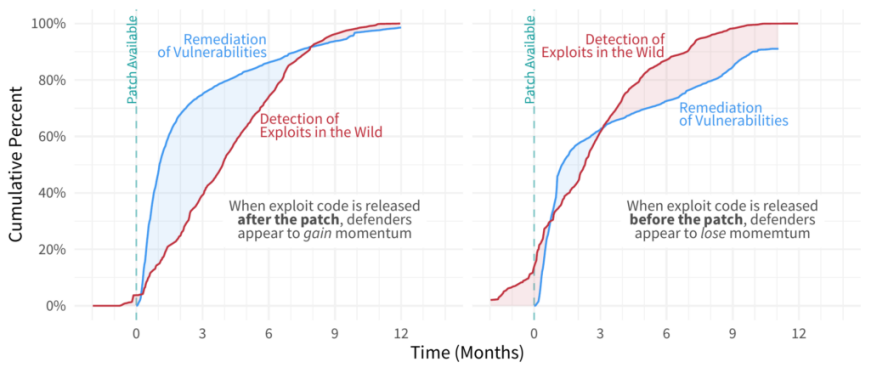
The investigation offers strong indications that early disclosure of the exploit code gives attackers an advantage .
Thus, in approximately nine of the fifteen months studied in this research, attackers were able to exploit vulnerabilities at a higher rate than what the administrators of those networks were patching. On the other hand, defenders only had an advantage for six of those fifteen months we mentioned earlier.
The exploit code in relation to the CVE release
As you can already deduce, there is a very close relationship between the disclosure of vulnerabilities and the appearance of their exploit. After the disclosure of this security flaw in a CVE, time begins to run until the code for its exploitation finally appears.
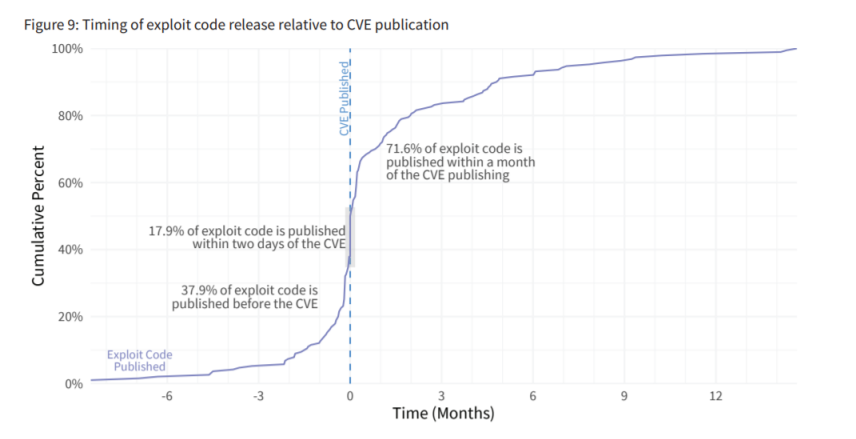
By the time a CVE is published, all pertinent information is fully available. This is how both attackers and defenders already have it, although sometimes they already have it before. Knowing when exploits appear relative to their release date can help defenders estimate how long they have to mitigate exposure.
Thus, one day after publication, more than 50% of the vulnerabilities already have code available to exploit them. One month after the publication of a CVE, 75% have been armed. Therefore, advocates should take a published CVE as a sign that the countdown of their clock has started and that action must be taken.
The importance of having a patch for defenders
Without doubt, the availability of patches marks the starting point from which advocates can begin to repair. Here you have a graph of the first detection of vulnerabilities by the scanner in relation to the availability of the patch.
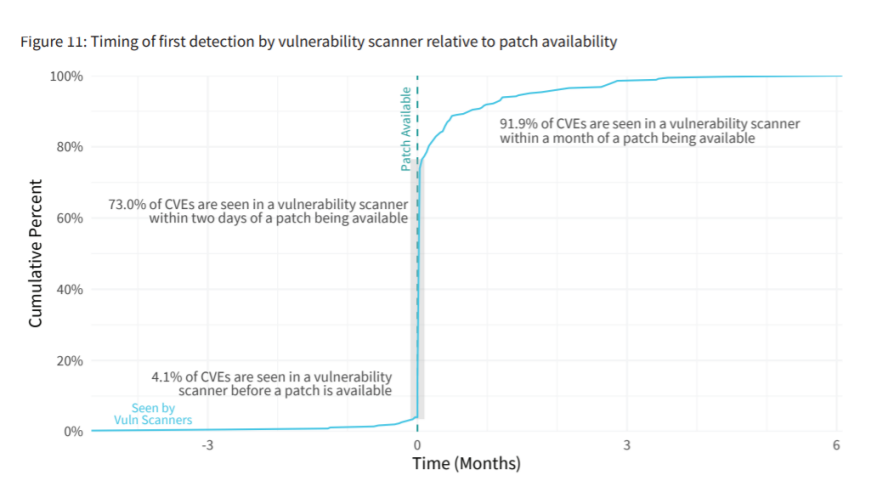
One conclusion we get is that more than 9 out of 10 vulnerabilities are detected in a network environment when the patch is available. This means that defenders know where the vulnerability exists on their network, and they have the means to remediate it in the form of a patch.
Again, this suggests that coordinated vulnerability disclosure is working as intended. By the time the CVEs become official and the patch is available, advocates have begun their remediation work. However, the time required for the remediation process to complete is another matter. For this reason, unpatched vulnerability disclosures are a drag on defenders. This situation could be further complicated if there is an exploit code.
Responsible vulnerability disclosure
The moment researchers find a vulnerability, they present its existence and the relevant exploit code they used to exploit that flaw. The software developer will create a patch that they will make available to their users. However, these developers sometimes fail to take action, and researchers end up publicly disclosing the vulnerability. The latter is to the detriment of defenders because time is running out and there is no solution available.
Other interesting data provided by the research were:
- More than 80% of exploited vulnerabilities have a patch available at the time of CVE publication.
- Only 6% of the vulnerabilities were detected by more than 1/100 organizations.
In short, it is necessary to disclose vulnerabilities and responsible exploitation codes to facilitate the work of defenders.