
Malware attacks cost companies many millions of euros throughout the year. IT security teams have the job and goal of addressing the best possible network monitoring, and reducing the time the malware stays. It is essential that the detection of ransomware or malware attacks in general is as fast as possible, to take the necessary measures and eliminate it. If malware does not affect a company from minute zero, it is thanks to the hardening of the different teams, which is why the Blue Team of companies becomes essential.
The report on the cost of cybercrime in the countries
In a report on the cost of cybercrime by the Ponemon Institute and developed by Accenture Security, it is observed that the costs incurred by malware attacks are increasing. Here you have a graph of the costs they represent for companies in millions of dollars. For the first time, as you can see, data from Spain and other countries have been reflected.
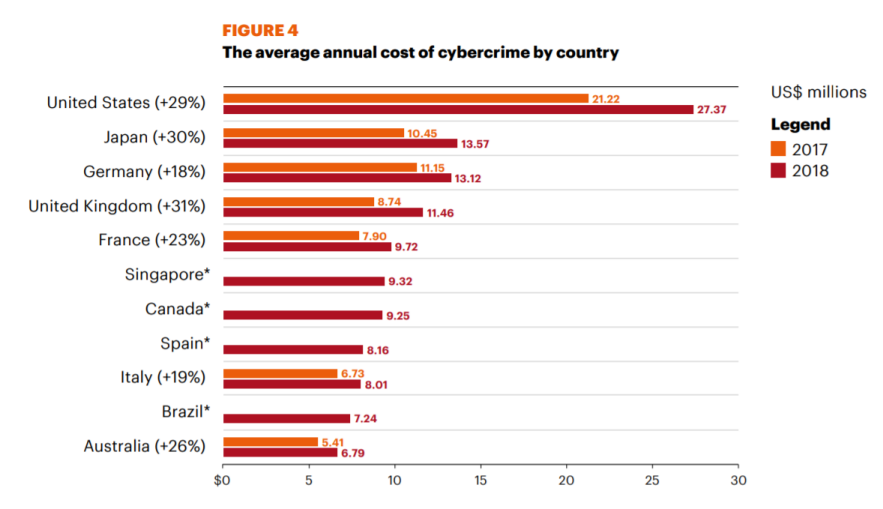
In it, it can be observed that the expenses caused by cybercriminals have increased between 19 and 31% compared to the previous year. Also countries like Canada, Spain and Singapore that participated for the first time, it is seen that the costs produced by these attacks are also important.
In his analysis of almost 1,000 cyberattacks, he highlighted the malware attack as one of the most frequent and also the most expensive to solve. Additionally, the number of businesses that experienced ransomware attacks increased 15% and the frequency with which it is carried out has tripled in the last two years.
Another interesting fact is that phishing and social engineering attacks were experienced by 85% of organizations. In this sense, we find a 16% increase in one year in attacks of this type. That this happens is concerning as people continue to be a weak link in the defense of cybersecurity.
Networks are increasingly complex and have more blind spots
An increasingly common thing is that security teams cannot see certain parts of the network as they are increasingly complex. In the event that malware manages to pass perimeter defenses, it may go undetected and cause serious damage.
If we work with a hybrid network model, these blind spots are increased. As applications move to a public cloud or companies implement virtualization, the network becomes more complex. At that point visibility becomes limited, and network security monitoring becomes more complicated.
Fortunately, things are looking up, and companies have managed to decrease the time the malware stays. Verizon in its 2020 data breach investigations report noted that more than 60% of data breaches were discovered in days or less. Although this is a significant improvement, not everything is positive. For example, more than a quarter of violations still take months or longer to detect. Therefore, we still have a lot of work to do.
Improve visibility of network traffic
IT security operations teams need to improve network monitoring to decrease the dwell time of malware and other malicious software.
Traffic has increased significantly as applications have become multi-layered and more compute intensive. Additionally, networks have become more virtualized to support more virtual machines. This change is making network monitoring difficult.
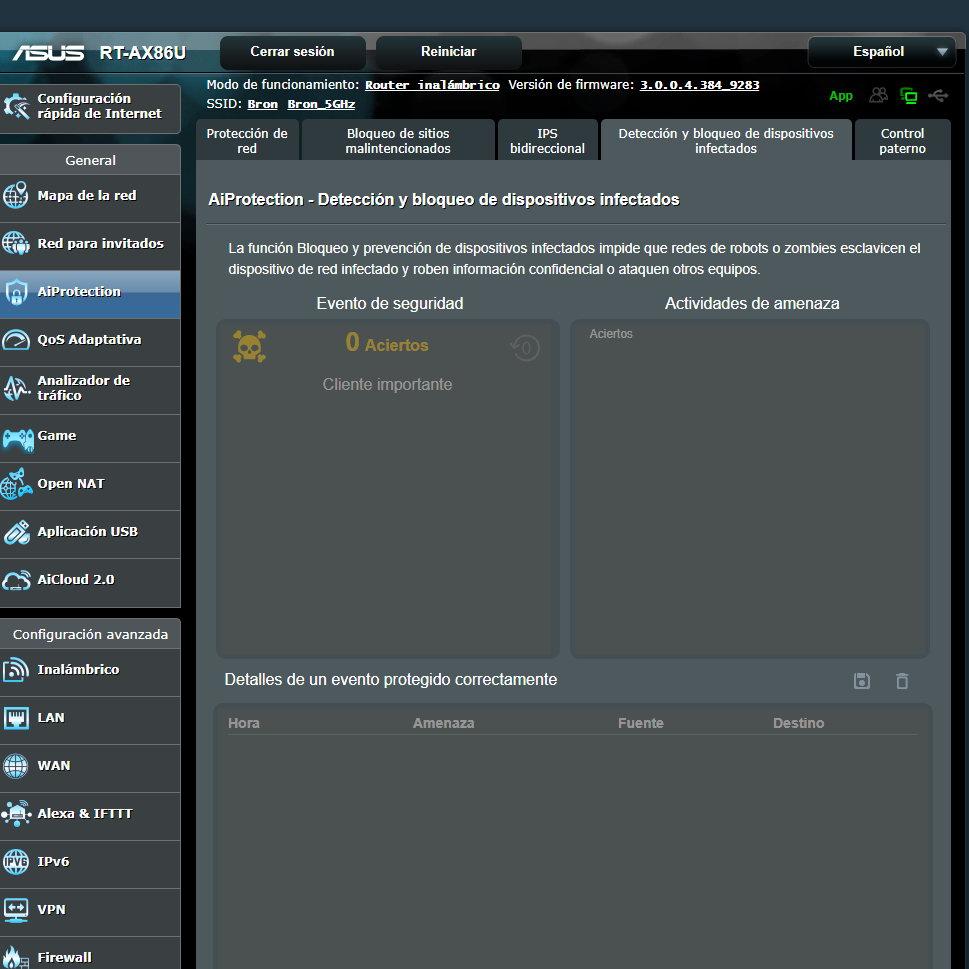
Even we in our home network can also monitor the traffic and see everything that happens in the local network, for example, ASUS has the AiProtection Pro functionality that allows us to stop malware and even has an intrusion prevention system ( IPS).
An important step is to gain access to this traffic as it allows security tools to detect unusual network behavior and alert us to a security breach. Access to this traffic reveals which IP addresses are communicating with each other, and when these connections are made. Thanks to this information, with the security tools based on the behavior, we can generate alerts when there are strange events in the network. Some anomalous behaviors that could be investigated would be:
- Unusual access to the database by an application.
- An FTP download of a lot of data at 4 in the morning.
Therefore, as companies prioritize working in the cloud, a vital goal is to have full access to all network traffic to keep our data safe.
Store data to analyze attacks
A good security policy also consists of having a history of the traffic that passes through our network stored. In the event of a security attack, it is very important to have a series of information, such as, for example, having access to detailed packets and flow data before, during and after a security breach.
Thus, security analysts can more precisely determine the extent of the breach and can also analyze the damage to find out how to prevent it in the future.

If we want to do this, we will need to collect network metadata and packet data from physical, virtual, and cloud-native elements of the network deployed in the data center, branch offices, and multi-cloud environments.
In addition, to collect this information we must have a combination of physical and virtual network probes. We also need packet brokers and capture devices to collect and consolidate data from different corners of the network. In that sense, it is very important that we can capture and store packet data before, during, and after a security alert for subsequent forensic analysis.
Finally, the more accessible these data are and the better organized they are, they will provide us with more valuable information.
Teleworking and security
This year due to the global pandemic of the coronavirus our way of working has changed. Teleworking has advanced greatly and recently a law regulating it has been approved in the Congress of Deputies. Previously, security teams worked with the assumption that most users access resources through the corporate network, and only a small number did so remotely.
Now, most users access applications in the cloud or in the data center over the public Internet. Companies have reacted by easing security restrictions and adopting the necessary security measures. In this sense, it is recommended that communications between employees and the company network be established through a VPN for greater security.
You have to gain visibility in the public cloud
Currently many companies as a consequence of the pandemic have accelerated the transfer of applications to the public cloud to take advantage of its scalability and flexibility. However, the lack of visibility can have a significant financial cost for the company.

Until not long ago, the main public clouds were platforms where you could see the traffic coming in and out of the cloud. The problem was, it doesn’t show what’s going on inside, and IT teams couldn’t monitor for signs of a breach. Fortunately, things are looking up, with some of the major cloud providers already adding features that mirror network traffic to and from a customer’s applications.
In short, detecting and decreasing the dwell time of malware in a hybrid environment requires access to the entire network traffic. Thanks to this, we will be able to detect security breaches earlier and we will be able to analyze the problem to prevent it properly.