When we download a file from the Internet, or if we have saved it for a long time, and we want to verify that it is still original and has not been modified, we usually use the hash. The hash function is used to perform various actions with files, such as verifying that two files are the same and nobody has modified them without permission. Two different files can never have the same hash, and therefore, this is one of the most reliable functions for this type of tasks.
To explain what it is for, let’s set the example of passwords. When we forget a password, websites usually do not send it to us when using the option “Recover password”, but they force us to change it. This is because the web pages never save the password as such (as it would not be safe), but instead keep a hash of it.
So, when we are going to log in, what we send to the web is the hash of the password that we enter. If this matches, let us in. If it is different, it blocks our access.
A hash is a achievement of letters and numbers generated through mathematical operations. This may be different, and have different lengths, depending on the algorithm used. Two examples of text hash would be:
- Hi10Hello: its hash value is: «2405T8BVB6838933c43806038e122433301FA9c08»
- Goodbye10Adios: its hash value would be: «6D102B5A3374702FA667E30B9068194B173FD110»
The same applies to files. Two exactly the same files will have the same hash value, while the slightest change in one of them, even if it is a single bit, will make this hash different.
How HashTools works
Once understood with the previous example, we can already show what this program will be used for and the functions it allows us to perform.
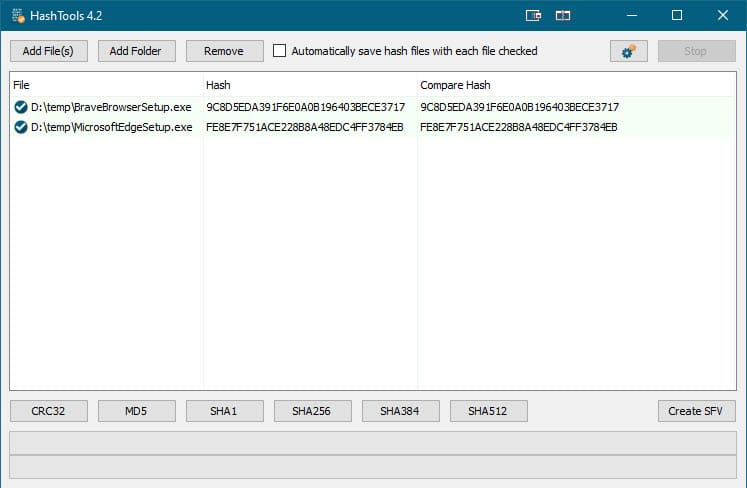
The program is simple, with it we can check the integrity of the files, create different hash functions, among others. Each hash function generates a number of different Bits, and are designed to withstand greater security than others. For example; crc32 throws us a 32-bit code or SHA1 a 128-bit code.
When we compare two files such as Hola.txt and Hola2.txt, with different contents we can see that they launch different codes. If both files did not have content they would throw us the same code.
Depending on the size of the files, and the algorithm we choose, calculating the hash can take more or less time.
Algorithms available in HashTools
With this program we will have the possibility to open and analyze both files and folders. And with that we include images, text, videos and songs, among many others. The algorithms that we can calculate with this program are CRC32, MD5, SHA1, SHA256, SHA384 and SHA512.
In addition, we can ask you to automatically save the hashes of the selected files for later reference.
How to download HashTools
In order to download this program we will only have to go to your website , and install it. Although we also have a portable version, which allows us to test the program, without having all the functionalities.
Steps to follow to download and install HashTools:
We will go to your website, and at the bottom in a blue box, we think a green button “Download now” or “Download Now”

It will redirect us to another web page, where a green button will appear again where we can finally download the installer, which we click to open it and follow the steps.

Safety recommendations when working with hash
Some safety recommendations are:
For the use of important material which we need to be difficult to decipher, we can use the SHA1 function, which is newer and safer than MD5 , which we can consider is already obsolete and would not be reliable.
We can also opt for more secure functions which require more bits, such as SHA256 onwards, everything depends on the user, and for the purpose that is used.