
4 Network Segmentation Best Practices to Level Up
While the number of cyberattacks skyrockets each passing day, cybersecurity practices also evolve to fight with them. At first, the idea was never to let […]

While the number of cyberattacks skyrockets each passing day, cybersecurity practices also evolve to fight with them. At first, the idea was never to let […]

In the market, the number of video chat apps is thriving. If you want to learn how to create the Chatroulette alternative, you should read […]

Frequently, many hours dedicated to studying do not bring the desired breakthrough in knowledge, becoming a heavy burden instead. This article guides how to make […]

A growing number of users lately are throwing themselves into working on the development of their own games. Although this is at first a task […]

We can say that the router is a key piece to have Internet at home. It is the device to which all the devices will […]

The security measures we use are not always equally valid. In the same way that hackers update their attacks, it is necessary for users to […]

Maintaining privacy when browsing the Internet is a very important factor. However, doubts always arise as to whether our data is really safe or if […]

To find out to what extent a device or a network is secure, we can perform different tests. It is always important to protect the […]

When we connect to the Internet, all applications redirect their traffic through certain ports. While some ports are open by default (for example, 80 for […]
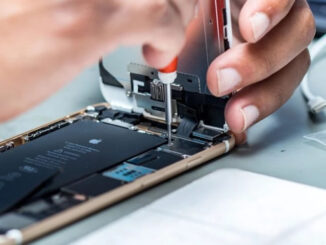
Smartphones have undoubtedly become the most important personal technology for anyone to have today. Not only is it necessary for personal use, but it’s an […]

You can have intruders on your computer with both physical and remote access. Think, for example, when someone has been able to take your PC […]

In the Microsoft operating system, it increasingly includes more options, functions and settings so that the user can configure, customize and manage his system as […]

Having a good wireless connection is an important factor for surfing the Internet. Today we use many devices that are connected in this way and […]

Torrent downloads through their corresponding clients have become commonplace for both end users and companies. As a general rule, large files are shared from here […]

The complexity and demand of most of the programs that we use today extends to almost all sectors of software. On certain occasions we can […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise