
Tips to avoid interference on your WiFi
To have a good wireless connection it is essential to avoid interference . There are certain devices that can cause your Wi-Fi to malfunction, with […]

To have a good wireless connection it is essential to avoid interference . There are certain devices that can cause your Wi-Fi to malfunction, with […]

Having security programs is essential to avoid cyber attacks and ensure that systems work well. However, it is equally essential to use them correctly. For […]

When we talk about the software called PuTTY, we are referring to a powerful program that allows us to make remote SSH connections with other […]

If you have a router for many years, you may have to replace that old router with a new one, however, we must differentiate between […]

The Dark Web is a part of the Internet that is hidden from search engines and that we often understand as dangerous and full of […]

In our homes we have more and more devices connected to the Internet. If we think about it carefully, about ten years ago we only […]

Having a good Internet connection is essential nowadays. However, sometimes we can have speed problems or cuts and this happens especially when we browse wireless […]
Largely thanks to the user interface and the integrated functions offered by such an important Excel program, it opens up a wide range of possibilities. […]

There are many types of security threats that we can suffer when browsing the Internet. Many types of viruses and malware that can steal data, […]

The Mac is one of the oldest computers that Apple currently has. Above all, MacBooks caused a great furor, and that is why it is […]

There are many security threats that can put our personal data and device operation at risk. There are viruses that affect performance, keyloggers that steal […]

Normally, when we go to buy a gaming monitor, we look at the number of reviews to make sure that it meets what we are […]
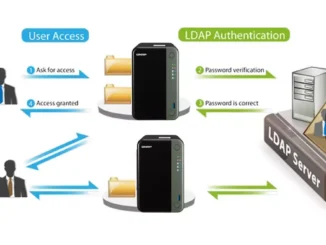
When we have dozens of computers on a network, it is necessary to organize the data correctly and also the credentials of the different users. […]

Shopping online is very common nowadays. We have a wide range of options available to buy practically anything. There are countless online platforms and services. […]

Hackers can have different ways to try to sneak malware and compromise the security of users. Undoubtedly, e-mail is one of the methods they use […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise