Currently a very common practice that we usually do with our Internet connection is to download all kinds of files. These files may have been altered, corrupted or have included viruses or malware. To verify the verification of the integrity of these files, the hash or checksums are used, something that we can do for free with the help of some programs developed for this purpose.
Something that most users are unaware of is precisely the possibility of verifying any file by means of hash that it incorporates and that allows us to know if the file has been modified and if it contains any malicious element. That is why today we are going to see what the hash consists of and what programs we can use to check files.

What is file hashing and what is it for?
The hashes or checksums are a mathematical algorithm that is responsible for transforming any arbitrary block of data into a new series of characters with a fixed length. This hash value will always have the same output length, regardless of the length of the input data. In general, each of the files that we download from the Internet are verified with the MD5 / SHA256 hash to make sure that the file is not modified or altered.
One of the main characteristics of Hash is that they are very efficient algorithms and do not require a large dose of computing power to be executed. The results will always be in a fixed-length string, regardless of the size of the input. For example, in the case of SHA-256 its length is 64 characters. In addition, they are irreversible, which makes it more secure, since it is not possible to take a hash and obtain the data that gave rise to it.
That is why, another of the functions for which hashes are used is for encryption and storage of passwords , as well as to protect other confidential data from possible spies. For this we can use different programs that we will see below.
Free program to know the hash of any file
When performing Hash checks to verify the composition of any file, we need a program specially developed for this mission. Next we will see a list of programs that will help us.
Hash Generator, with integration with the contextual menu
We started with a free universal hash generator tool. It is responsible for automating the generation of 15 different types of algorithms or checksums. It is capable of supporting most of the popular hashes such as MD5, SHA, BASE64, LM, NTLM, CRC32, ROT13, RIPEMD, ALDER32, HAVAL, WHIRLPOOL, etc.

This application also allows to generate hash both in a file and in a text input. It has integration with the Shell contextual menu to be able to perform operations quickly, just by clicking on any file with the right button. The generated lists can be saved in an HTML, TEXT, XML and CSV file.
If we want to try Hash Generator we can download it for free from its website . It has a simple interface and is completely portable, so it does not require installation.
OpenHashTab, with support for 14 types of algorithms
This program is responsible for offering compatibility with up to 14 different algorithms that will help us calculate the hashes of the files. Among them is the SHA-1, SHA-256 and SHA-512 or the MD5. It also has support for ten other different algorithms that we can activate or deactivate depending on our needs.
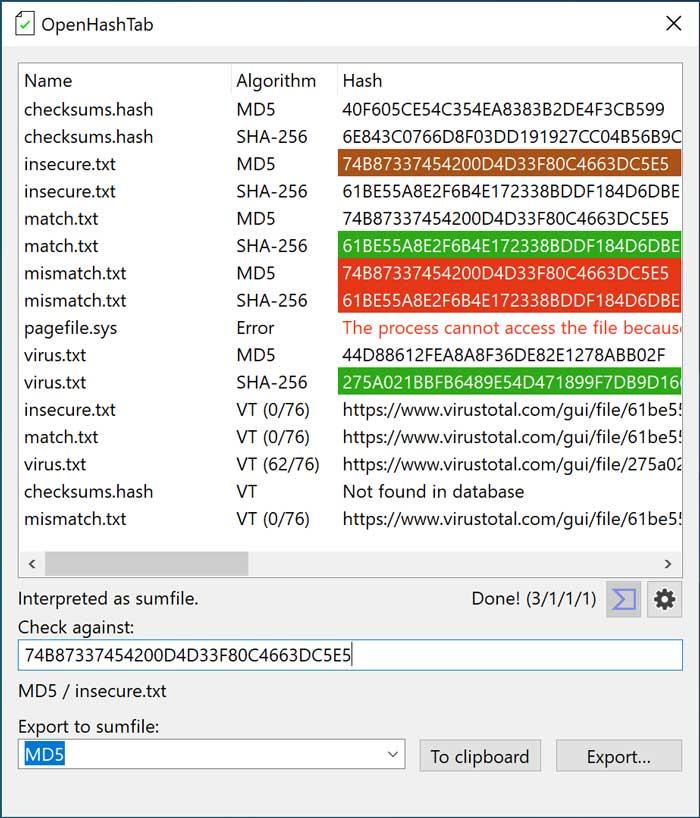
The application allows us to verify the hash values, if the provider of the file provides a hash value to the file, indicating if its value matches that of the file. It will also be possible to export the hash values either in a text file or by copying them to the Windows Clipboard. Instead, its main drawback is that it is in English.
OpenHashTab is an open source and completely free program, which we can download from the following link .
HashMyFiles, calculate MD5 and SHA1 hashes quickly
We now find a small utility that allows us to calculate the MD5 and SHA1 hashes belonging to one or more files on our system. Hashes can be easily copied to the clipboard or saved to a TXT, HTML, or XML file. It can also be launched from the Windows File Explorer context menu to display the MD5 and SHA1 hashes of the selected files or folders, as it supports batch generation.
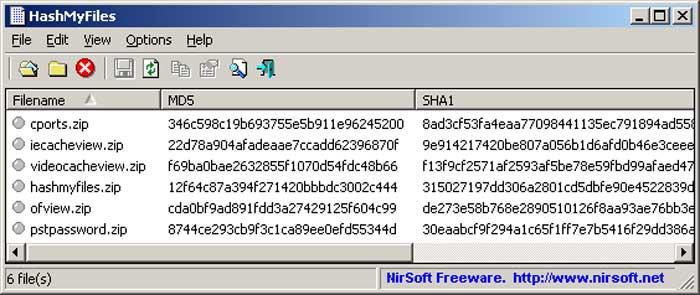
In this way, if we select a folder, the application will be able to show all the hash values of all the files that the selected folder contains. In the case that we execute it on a single file, it will only show us the hashes belonging to that file individually.
HashMyfiles is a completely portable tool so it does not require any type of installation on our hard drive. It is compatible with all versions of Windows both 32-bit and 64-bit. We can download it for free from here .
Hasher Lite, easily verify the integrity of files
This small utility allows us to verify the integrity of the files using a wide range of compatible algorithms: CRC32, MD2, MD4, MD5, SHA1, SHA256, SHA512, RipeMD128, RipeMD160 and ED2K. Each of the processed files will be registered and ready to be exported to different verification file formats such as SFV, MD5SUM, and SHA1SUM.
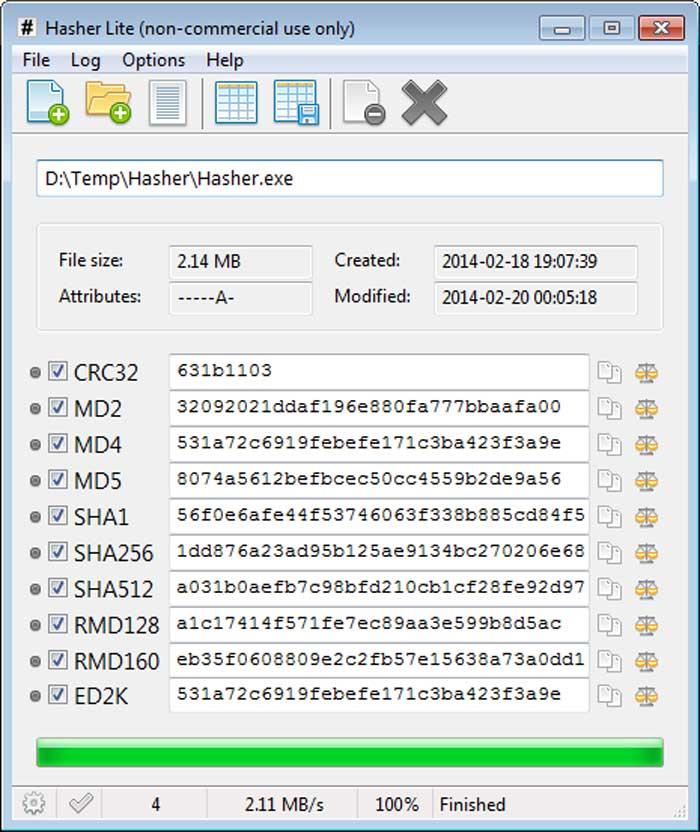
This application supports batch generation, which makes it possible to generate multiple types of hashes simultaneously per file. This task will be possible to carry out in a simple way, thanks to the practical file comparison and hash functions, such as holding down the shift key to make a comparison with the next file, or pressing ctrl to compare two files.
Hasher Lite is free and portable software that does not require installation, and that we can download from its official website.
HashTab, detects any modified or corrupt files
We are facing an application that will allow us to calculate different sums of file integrity, to check if a file has been downloaded correctly from the Internet. For this, it is in charge of comparing it with the signature provided by the main page, detecting if the download has been modified or corrupted. It is also possible to calculate the integrity signatures of the files that we copy to another device to ensure that the data is copied correctly.
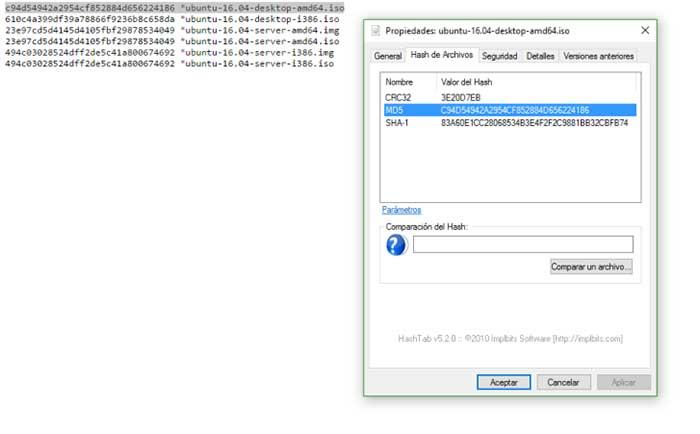
As we have mentioned, its main mission is to verify if the checksum of a file is correct, something that can be done by integrating seamlessly into the Windows context menu. It also allows you to compare checksums of two different files and is compatible with the most used algorithms such as MD5, SHA-1, SHA-3, SHA-256 and SHA-512.
HashTab is a free application for home use, which we can download from this link.
QuickHash, compare files with each other and record their results
This application allows us to calculate the hash of any file on our PC. For this it uses different algorithms such as SHA1, MD5, SHA256, SHA512 and xxHash. It offers us compatibility with text data, files, text email lists and complete file folder trees. Another important option is that it allows us to compare files with each other, or file folders that are based on the hash algorithm and thus record their results.
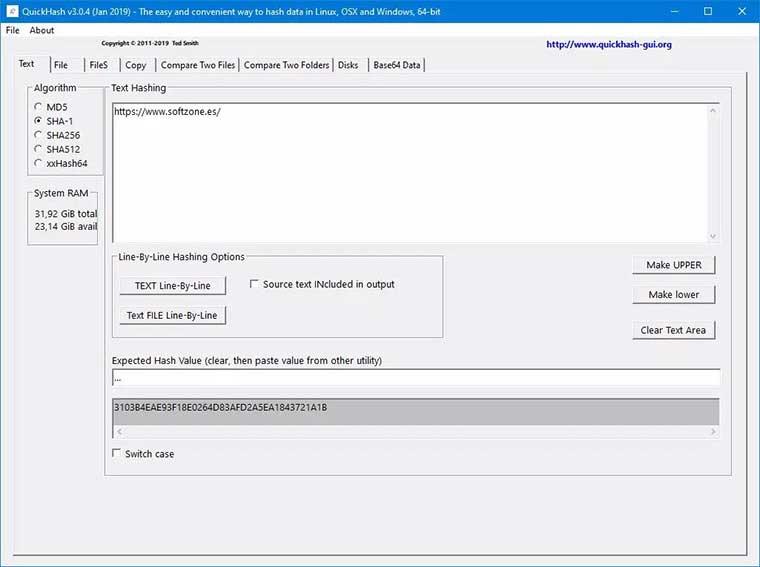
You can also work through a text document line by line, segmenting each one as you go. All the results are displayed in a clear and easy-to-interpret interface, from where we can know all the results we have obtained.
QuickHash is a completely free and open source application that is available for Windows, Linux and macOS. We can download it from here .
MultiHasher, allows checking for malicious files using VirusTotal
We are facing a tool that will help us to verify and generate the hash of a single package. It has up to six different algorithm signatures such as CRC32, MD5, SHA-1, SHA-256, SHA-384, SHA-512. Its use is simple because it is enough to drag and drop any file or folder for the hash or generate one for a text string. To see them, just pass the mouse over it once the calculation has finished.
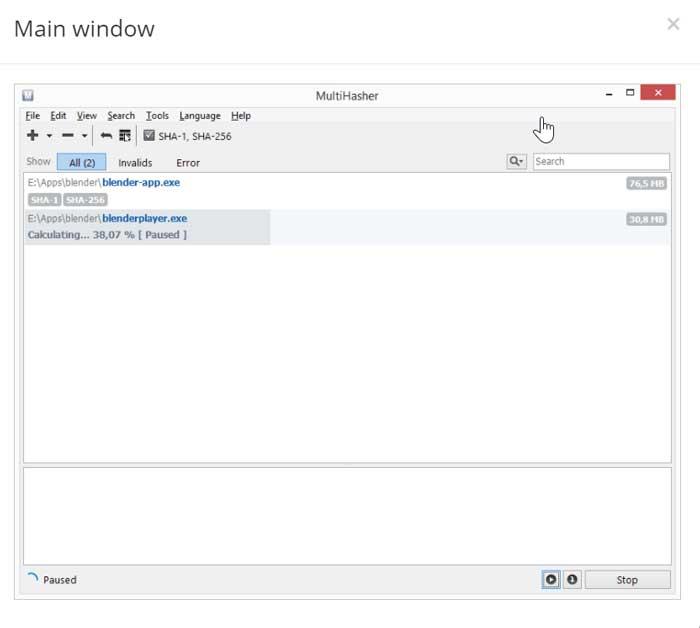
Another feature to highlight is that it allows us to know if a file is infected or not infected with a virus. Since this application is integrated into the malicious file checking database of VirusTotal, the famous multi-scanner. But this is something that we can only do if the file has been previously analyzed.
MultiHasher is a free application for Windows that we can download from this link.
PowerShell, the utility built into Windows for checking hash files
If we do not want to download any program to our computer, we must know that Windows has among its tools an integrated file hash checker. It is a function that we can perform with two default programs that we can find in the PowerSell function.
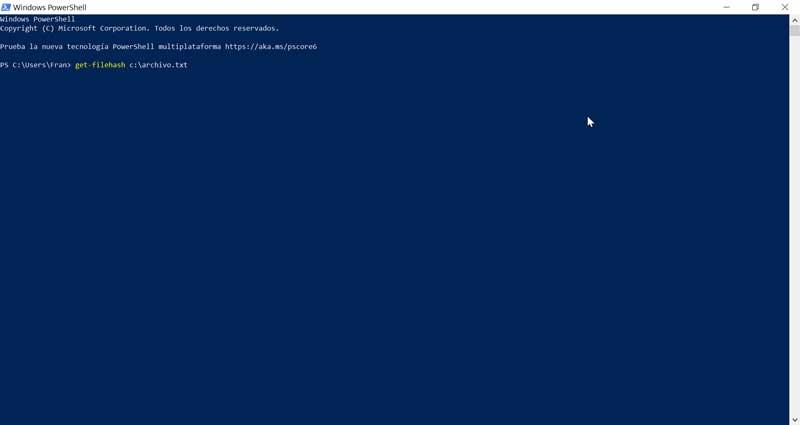
PowerShell’s file hash checking feature supports SHA1, SHA256, SHA384, SHA512, MACTripleDES, MD5, and RIPEMD160, and can be used through Get-filehash and CerUtil. With them we can generate the hash of a file. If we choose to use Get-filehash it will use the SHA-256 algorithm, while if we decide to use CerUtil, it will use the MD5 algorithm. An example would be get-filehash c: / file.txt
In the event that we want to use PowerShell to check the hash of any file, just press the Windows key and then type PowerShell. Its window will appear from where we can use the corresponding command.