On the 30th, the root certification authority AddTrust External CA Root expired. It had been running for 20 years and this has logically had an impact on many websites. However, it should be borne in mind that it does not greatly affect the daily use of users, with some exceptions that we are going to comment on.
What are root certificates
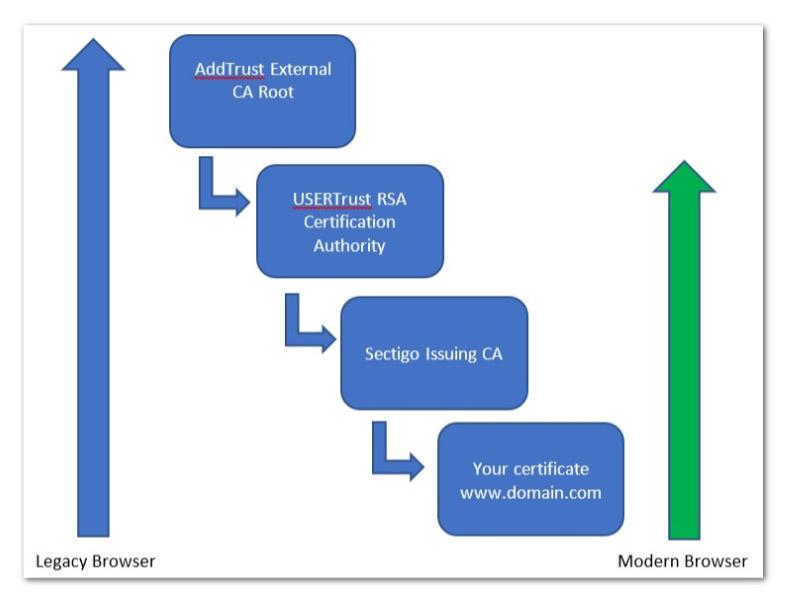
Root certificates are self-signed certificates. This means that the “Issuer” and the “Subject” are the same. A root certificate becomes a trusted root certificate (or trusted CA) by being included by default in the trust stores of software such as a browser or operating system.

These truststores are updated from time to time as part of the software updates of that browser or operating system. The problem is that on older platforms they are only normally updated as part of a full software update. That is, they do not acquire those updates in older versions.
This means that there are devices that do not have updates to include modern root certificates and therefore are not compatible with current standards.
Most of the affected certificates are issued by Sectigo or Comodo . However, it is not something that affects many current users. In other words, it would only affect those that use obsolete systems such as Windows XP and Internet Explorer 6 to navigate. It can affect monitoring systems or scripts more.
We can say that a digital certificate allows a domain and a server to be validated in a secure way and thus avoid major security problems, such as impersonating that domain or having a third site respond to requests on our behalf.
It allows the connection between the browser and the server, once established, to be encrypted between them. This prevents potential intruders from viewing the content, which may have confidential information such as passwords or bank details.
Modern clients and operating systems
It should be noted that all those modern clients and operating systems will not have any problems beyond May 30, which was when the root certificate expired. In this case they have all the newest and most modern Comodo and USERTrust roots that will be available until 2038.
On older devices, the new Sectigo roots would have to be updated and installed. There would be no need to issue or reinstall the certificate.
In short, as we have indicated, the problem will only be present in those who use obsolete operating systems and browsers. Once again the importance of always keeping the latest versions is demonstrated. On many occasions, security problems can arise that put our equipment at risk. It is vital to have the latest patches installed to correct these problems.
From Transparent CDN to solve this problem, they have chosen to redo the server certificates (which does not mean to renew, since they are valid until the expiration date) and thus use the new CA that they have made available from Sectigo and which have not expires until 2038.
We leave you an article where we talk about how the HTTPS certificate works.