Network devices, such as a router, can suffer many attacks. There are many varieties of malware that in one way or another can compromise security. In this article we echo ZHtrap . It is a new malware whose mission is to turn infected computers into honeypots.
ZHtrap, the malware that turns infected computers into honeypots
This threat has been detected by a group of security researchers at 360 Netlab . It is based on the Mirai source code and is compatible with x86, ARM, MIPS, and other CPU architectures. It is a botnet whose mission is to track down routers and other infected UPnP network devices and turn them into honeypots.
When it succeeds in taking over a device, it prevents other malware from re-infecting its bots with the help of a whitelist that only allows already running system processes and thus blocks all attempts to execute new commands.
ZHtrap bots use a Tor command and control server to communicate with other botnet nodes and a Tor proxy to hide malicious traffic. Among the capabilities of this malicious software we can mention that of carrying out DDoS attacks and scanning for new vulnerable devices that it can infect.
But beyond that, ZHtrap also has backdoor functionality that allows additional malicious payloads to be downloaded and executed.
It is based on security vulnerabilities
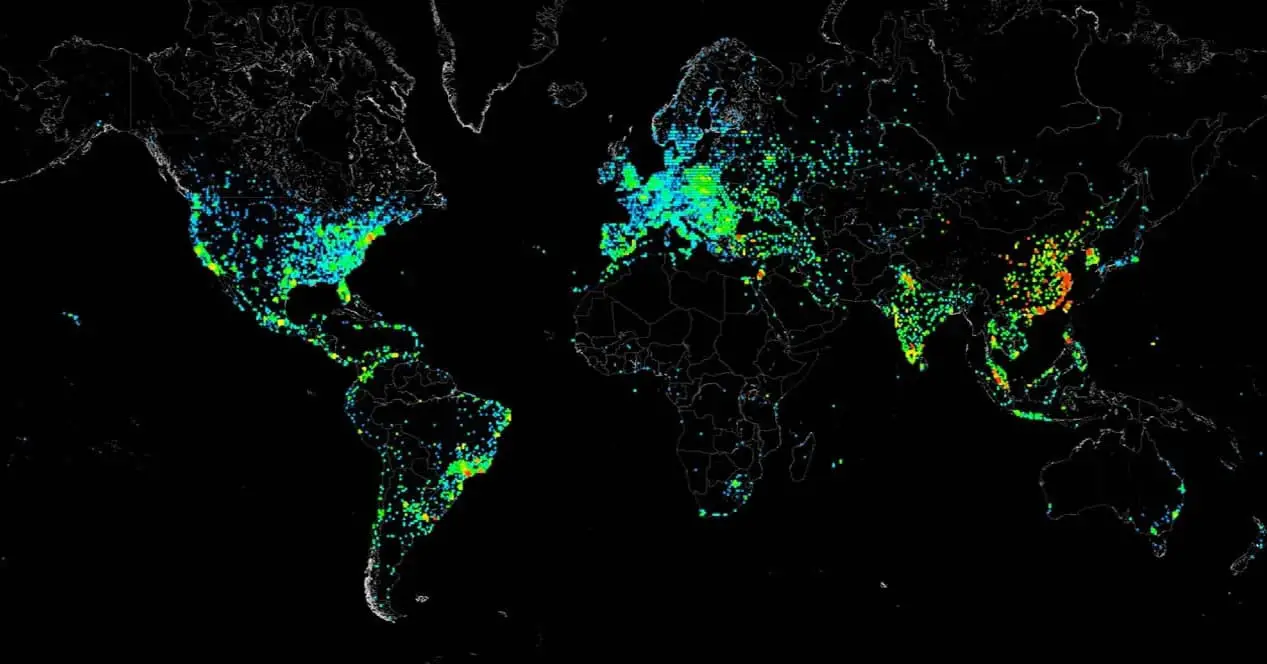
To spread across the network, ZHtrap relies on exploits targeting four security vulnerabilities in Realtek SDK Miniigd UPnP SOAP appliances, MVPower DVR, Netgear DGN1000, and a long list of CCTV-DVR appliances. It also searches for devices with weak Telnet passwords from a list of randomly generated IP addresses collected with the help of the honeypot that it deploys on devices that are already part of that botnet.
Now, the most interesting feature of ZHtrap is how it turns infected devices into honeypots to collect IP addresses from more targets that are likely to be vulnerable and can spread more or are even already infected by other malware.
Once implemented, the ZHtrap honeypot starts listening for a list of 23 ports and sends all the IPs that connect to them to its scanner module as potential targets in its attacks.
According to 360 Netlab, other botnets that we have analyzed before, the most interesting part of ZHtrap is its ability to turn infected devices into a honeypot . They can use these honeypots as a tool to capture attacks, such as collecting scans, exploits, and samples.

How to avoid becoming a victim of ZHtrap and similar threats
It is important to be protected to avoid being victims of the ZHtrap malware and any other similar that could put our computers at risk. For this, it is essential to have the devices updated. We have seen that they take advantage of vulnerabilities that they find on computers and thus can attack them. Preventing botnet attacks and the like should be our priority when using network devices.
Another point that must be taken into account is the importance of creating passwords that are strong and complex. In the case of ZHtrap, although it can occur with other similar threats, they also take advantage of the weak keys that are on those devices. We must always create passwords that have letters (uppercase and lowercase), numbers, and other special symbols. All this in a random way.
In short, we must protect our devices at all times to prevent the entry of intruders. It is something that we must apply at all times, regardless of the type of operating systems or equipment we have.