The ping of death is one of the many attacks that we can suffer on the network. As we know, there are many threats that could put our security at risk and compromise the devices we are using. This type of problem is also known as ping flood. We are going to explain what this threat consists of and how it could affect us.
What is ping of death
It should be mentioned that ping of death is one of the oldest attacks on the network . It is a type of denial of service attack. What the attacker does is send a malicious data packet. Once the recipient’s system tries to process it, an error appears which is what causes the computer to crash.
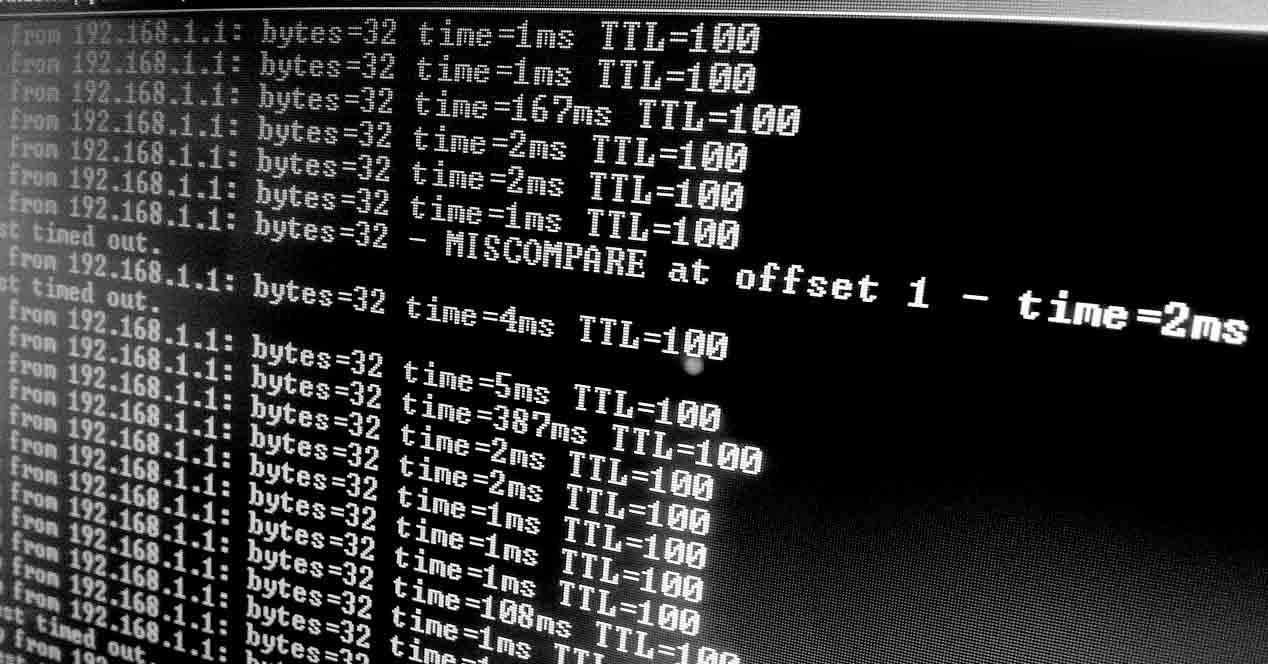
This attack creates an IP diagram that is larger than the maximum authorized size, which is 65,536 bytes . This is sent to a system that has a vulnerable TCP / IP stack and causes the system to hang.
Luckily it should be noted that today most computers are no longer vulnerable to this problem. It is a type of attack that was very present, especially in the 90s. From then on, operating systems corrected this vulnerability.
By sending pings of that size, they prevent teams from responding. A ping flood or ping of death occurs. This can happen if fragments of a ping of that size, larger than 65,536 bytes, are sent. When the computer tries to mount that received packet, all its fragments, a saturation occurs. This results in a system crash.
Vulnerability present in many operating systems
It should be noted that this vulnerability, what is known as ping of death, has been present in all types of operating systems and devices. It is something that has affected different versions of Microsoft Windows, Unix, Linux, Mac and also devices such as printers and routers.
Over time, patches have emerged to correct this problem. In fact, as we have mentioned, as of the end of the 90s this problem has ceased to be present, with few exceptions. Yes it was a much more important problem before that date.
However, although it is not something of this time, we have seen ping of death on a more recent occasion. In fact, in 2013 Microsoft released a security patch for the ICMPv6 protocol , which affected all versions of the popular operating system except for Windows XP and Windows Server 2012. That vulnerability was registered as CVE-2013-3183.
Very easy to apply
The Ping command appeared in the 1980s. It used the ICMP protocol and was used to collect information from a network and to solve certain problems. The point is that, years later, some user realized that it was possible to send multiple ICMP packets larger than 65,536 bytes.
That, as we have seen, could saturate a system and even make it unable to function. The operating systems were not prepared to avoid this. Then any user could ping death and block it.
This could leave unserved many teams in no time. A problem that in the late 90s affected many computers around the world. The operating systems solved this vulnerability and luckily at present it is not something that we should worry about, unless a bug like the one we mentioned in Windows in 2013 appears.
We can therefore say that this type of threat was the origin of the DDoS attacks that we can see today in the network. These more modern and sophisticated attacks can shut down critical web servers. We have seen cases in which they have affected very popular platforms that have millions of users around the world.
To avoid problems of this type, although this one in particular is an exception today, it is best to always keep the equipment updated correctly. On many occasions failures arise that can be exploited by attackers. It is essential to have the latest versions at all times and to be protected.