
How hackers can attack your computer through USB ports
Our computers can suffer many types of attacks. In most cases these are started because we are connected to the Internet and we do not […]

Our computers can suffer many types of attacks. In most cases these are started because we are connected to the Internet and we do not […]

There are certain terms in the computer world that when we hear them cause us all kinds of rejection. Precisely two of them are the […]

The age of hyper connectivity that we are living also has a dark face with cyber espionage or the trafficking of personal data. It is […]

One of the biggest fears on the part of mobile phone users is seeing their data leaked online . Privacy is a critical factor in […]

Waiting for a package on these dates is very common. We do Christmas shopping online and also from various stores or platforms. This means that […]

These holidays are traditional times to give and receive gifts. That is why it is not surprising that purchases increase a lot, both online and […]

Five years ago few people had files in the cloud. With an increasingly digital world, this trend is changing and there are already many users […]

The online infrastructure allows us to enjoy many services that we use on a daily basis. One of the ones we use the most is […]
Log4Shell is the latest vulnerability that brings to mind many administrators who have seen how their servers are vulnerable to remote attacks. It is a […]

Without a doubt, ransomware is one of the most important security threats that exist today. It is a type of malware that seeks to encrypt […]

From two-step verification to removing private information from Amazon, there are several settings that we should enable right now in our Amazon account. There are […]

The security of wireless networks is crucial in a future (and a present) in which they have more and more specific weight among home users, […]
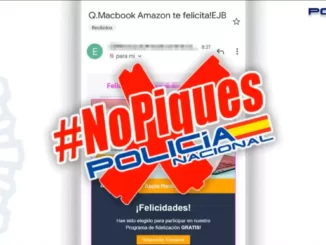
Unfortunately, it is already too common to find scams related to Apple and its products, of which obviously the brand itself or any other is […]

We have become relatively accustomed to the appearance of errors in the technological world that in some way endanger our data, although, nevertheless, in most […]

A group of security researchers from the University of Darmstadt, Brescia, has demonstrated how it is possible to steal passwords and manipulate the traffic of […]
Copyright © 2026 ITIGIC | Privacy Policy | Contact Us | Advertise