One of the terms that has appeared alongside concepts such as ARM, x86, and everything related to the register sets and instructions of a CPU, also known as ISA, is RISC-V. But what do these acronyms mean and why are they on the lips of a lot of people lately? We are going to get you out of doubts about what they mean and how they affect the world of hardware that we use daily.
The concept of free software is based on the following four principles:
- The freedom to run the program as desired. …
- The freedom to study the source code and modify it. …
- The freedom to redistribute copies if you wish – basic requirements. ..
But until recently there was no equivalent in hardware, it is true that the basic elements of digital design such as logic gates, combinational and sequential circuits, etc. If they are not protected by any intellectual property, for years we have seen how it was impossible to create a general purpose processor or an accelerator using a completely free ISA, in the sense that it does not belong to a multinational.
One may think that ARM is free by its open nature, but if you develop a processor or accelerator with their ISA then you find that you have to pay them royalties and have permission from them. In addition, the level of modification that they allow to make on their architectures is limited , especially at the ISA level in which they do not allow any type of variation.
This makes a free ISA necessary, which is not tied to any multinational behind and therefore is completely free to use.
RISC-V history

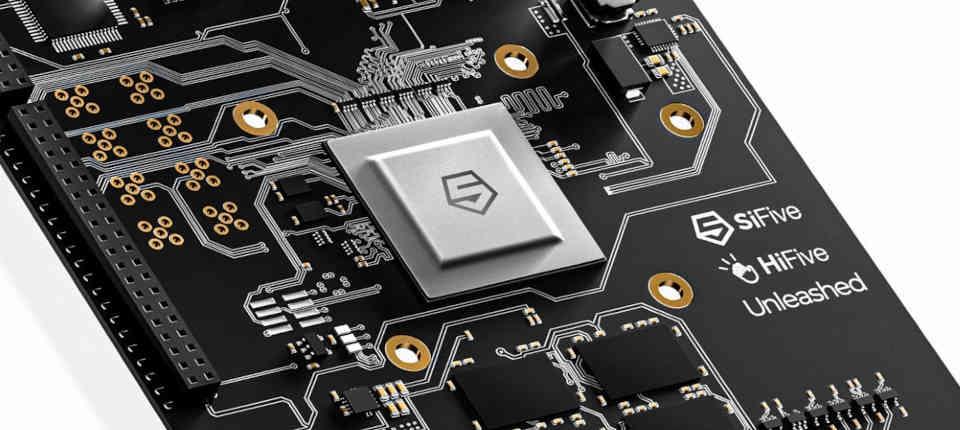
During 2010, the University of Berkeley decided to stop depending on a commercial ISA to create its own, with this the RISC-V project was born, designed to create a set of records and instructions that would not depend on a large multinational.
The project lasted four years, and in 2015 they created the RISC-V Foundation to control the evolution of the ISA that they had initially developed for the projects of their IT department, which is the one that directs how this free hardware standard evolves, especially the base specification and certain extensions.
RISC-V Features
All RISC-V processors must carry the set of registers and base instructions, the standard indicates that these registers and instructions cannot be eliminated in any way since they are essential for the operation of the processor.
The ISA RISC-V has four different base versions:
- RV32i: 47 instructions in total, 32-bit integer arithmetic and 32-bit addressing.
- RV32E : Same as the previous one, but with only 16 records by eliminating the records of the counter type. It is intended for embedded systems.
- RV64i: 59 instructions in total, it is an evolution of the RV32i that adds support for integer calculation and 64-bit addressing.
- RV128i: It is an extension of the RV64i, this time adding instructions and 128-bit addressing.
On the other hand, different extensions can be added:
- M: 8 additional instructions that give the RISC-V processor the ability to multiply and divide integers.
- A : 11 instructions for atomic operations with memory.
- F: 26 instructions, 32-bit floating point support.
- D: 26 instructions, an extension of F that supports 64-bit floating point.
- Q; Extension of D that provides support for 128-bit floating point.
- C: 46 instructions that allow you to work with data compressed in 16-bit integers.
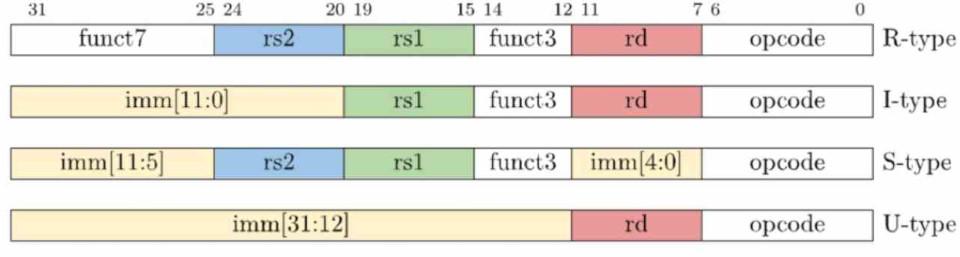
What makes the ISA RISC-V special is the ability to create new instructions for certain specific tasks and add them to the processor you are doing, all you have to do is keep the instruction formats used in the ISA base of the architecture:
These characteristics have also made RISC-V come to be used in different different fields, especially in the world of accelerators or coprocessors, thanks to the fact that engineers can create their own instructions, which makes RISC-V ideal for different types of homework.
RISC-V as ISA for accelerators or coprocessors
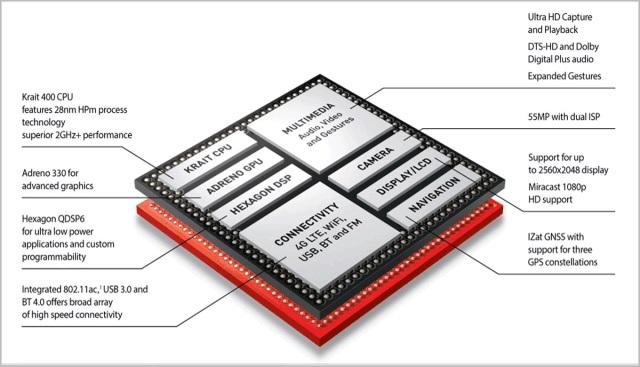
If we look at any modern processor, be it a CPU, a GPU or even a SoC we will see a huge number of accelerators inside that accompany the main processors and that serve to accelerate certain specific tasks.
Typically, each of these accelerators works with a proprietary ISA, which brings with it a series of consequences, but especially with regard to the support and maintenance of these pieces of hardware. When an accelerator or coprocessor uses a proprietary ISA it becomes an opaque box, which complicates the development of drivers that communicate the software with the hardware, especially in the free software community.
The idea of using RISC-V in accelerators or coprocessors has the following objectives:
- Allow the development of software drivers in such a way as to have a better understanding of how the hardware works.
- It facilitates the maintenance of the hardware, as well as the creation of microcode much more efficient.
- It enables anyone to design hardware solutions to their specific hardware system problems, without having to wait for a third party
This has paradoxically caused many multinationals to abandon the ISAS that own their accelerators or co-processors to adopt RISC-V.
RISC-V as CPU

Although all programs speak binary, they do not actually all speak the same language and each of them will interpret the binary code in one way or another. It is for this reason that a program compiled for ARM will not be able to run on x86 and vice versa. Well, RISC-V is one of those languages so it has its own rules regarding the way in which the instructions of its programs have to be written.
If we talk about the software used in both PC and PostPC devices, we find that in the first case all PC applications work only on processors with ISA x86, while the same happens with the second case, but with ARM. This makes it very difficult for any processor with another ISA other than those two, as is the case with RISC-V, to gain a foothold in these markets, if not completely impossible.
But there are specific markets in which hardware is used for specific and therefore highly specialized tasks. In which the software they run is developed along with the hardware. It is those types of projects where compatibility with third-party software is not important where RISC-V is growing exponentially and where its adoption is increasing.