
In recent months we have seen how ransomware has created immense chaos in hundreds of companies and government agencies , where much data has ended up encrypted. This data is currently not recoverable, and it may take years for the decryption tool to be created. Fortunately, it seems that this string of attacks has come to an end.
This ransomware has a constant update system, where the REvil group sells access to fully updated files in subscription service format, as if it were a Netflix malware.
REvil: goodbye to your ransomware attacks
REvil had a ” ransomware-as-a-service ” ( RaaS ) system, and was one of the first to start offering this service in April 2019. Its “product” was based on the GandCrab ransomware, which appeared early 2018. In the case of REvil, it is believed that they operated from Russia.
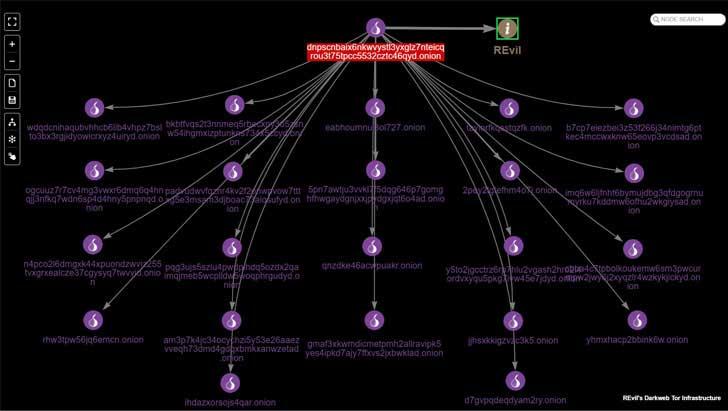
This group has apparently disappeared from the Internet without a trace. REvil had an infrastructure in the Tor network with a total of 23 websites in which they filtered data, carried out extortions, and processed the payments of those who hired their services. They are all gone, showing the “Onionsite not found” error.
The group had been responsible for more than 360 attacks on public and private sector companies in the United States, causing billions of dollars in losses to the country. The group made at least tens of millions of dollars with its activity, since some affected companies paid them the ransoms in bitcoin in order to recover the money, such as the meat company JBS, which paid 11 million dollars.
The end of the group coincidentally comes weeks after Vladimir Putin and Joe Biden spoke about the serious problem posed by ransomware. The closure of REvil has been planned, and its infrastructure has been dismantled, either by the authorities or by the malware operators themselves.
This leaves those who have been infected with the malware without any option to recover the money, since, since the group is dismantled, they do not have the option of sending the payment verification nor will they be able to receive the keys back, so they will have to wait for someone to create decryption tools soon.
The ransomware used in attacks on Spain is Ryuk
In Spain, unfortunately, most of the attacks have been carried out with the Ryuk ransomware, which is maintained by a group other than the one that has disappeared. In addition, Ryuk is the ransomware that has made the most money in ransoms, using infection mechanisms similar to that of REvil .
For this reason, the attacks will not disappear, and it is even to be expected that there will be a rebound in the attacks carried out with Ryuk, since together with Maze, they were until now the most used ransomware trident on the network. We may see a temporary drop in these types of attacks because other groups are scared by possible reprisals, but there is always some group that ends up taking the baton in a system as lucrative as this.