Cybercriminals are always on the lookout for our account credentials and profit. Their targets generally target Microsoft accounts, social media accounts, and work-related accounts. Today in this article we are going to explain the most common Phishing strategies on social networks Facebook, Instagram, LinkedIn and Twitter, so that you do not fall for them. The first thing we are going to do is explain what Phishing is and a series of basic notions, so that we are not victims of an attack of this type. Then we will focus on the aforementioned platforms and explain the strategies that cybercriminals employ.
What is Phishing and how to avoid being a victim of it
A Phishing attack aims to loot the credentials of our accounts. It all starts when you send a message posing as a legitimate business or organization. In this case, we mean that they pose as legitimate messages from social networks such as Facebook, Twitter, Instagram etc. when they really are not.

That message we receive generally contains a link that directs us to a cybercriminal’s website or to a malicious file. Undoubtedly, we find a case of identity theft from a company in which the victim will think that it is on the official site. The objective of a Phishing attack is that the user, when logging in normally, ends up handing over their account data (username + password) to the cybercriminal.

Phishing strategies used by attackers can be very varied, but here are some measures that can help to avoid them:
- We should not log in from email links.
- Nor do you have to open or download attachments.
- You have to analyze the grammar and appearance of the message. If you have spelling mistakes, and the text looks like it has been translated from other languages and is wrong, be suspicious.
- Check that the link has the correct domain before clicking on it.
- Protect the account with multi-factor authentication.
- Keep our computers conveniently updated with the latest software updates. In addition, measures such as having a good antivirus and antimalware software are highly recommended.
The most common Phishing strategies on Facebook
Facebook is one of the most popular social networks, and also one of the top targets for hackers. We increasingly have better protection methods to protect our accounts, but attackers also continue to work to break down those defense barriers. One of the Phishing strategies most used by cybercriminals with the aim of stealing credentials is social engineering .

In this sense, targeted phishing is gaining importance. In the message that the victims receive, they show their private information such as:
- Name and surname.
- The place where they study or work.
These data to make that message more credible, as you may have deduced yourself, they get from Facebook. Another aspect that we must be aware of is also malicious ads . Facebook has security measures in place to prevent this type of action, although some are occasionally managed. Thanks to these bogus ads, they can allow the download of malware or redirect to sites controlled by attackers, they can allow the download of malware or redirect us to web pages controlled by cybercriminals.
Undoubtedly, another of the most used Phishing strategies on Facebook are the links we receive through Facebook Messenger . Here we must be very attentive and act with caution, measuring our steps very well. In this sense, although Phishing attacks are one of the most used there is more. For example, it could be links that direct us to malicious websites with software designed to infect our computers, or it could also be hoaxes and false advertising.
In addition, we would have to talk about the danger of bots or fake profiles . Thanks to them, attackers could enter comments in our profiles or in the groups that we are. There they can use malicious phishing or other links, use them to collect information or attack us in some way. Finally, one thing we recommend in this article is to enable double authentication on Facebook.
Phishing strategies on Instagram and a practical example
Instagram has become one of the main social networks for many influencers. In fact, some of them can live comfortably making their stories and publications on this popular social network.

Both professionals and people who are just starting out, can be a victim of the Phishing strategies of cyber criminals. One of the most used resources is the one in which we receive a notification that our account has violated copyright . In the message we receive, in addition, the logo and the Instagram header appear and, in addition, the sender has a sending address very similar to the original.
Another point to note is that the attacker offers a short time to fix the problem. They generally leave 24 hours, although in some cases they have been seen to give a period of 48 hours. In cases where the strategy of speed is played, you have to be suspicious. This is used a lot in attacks, both on Instagram accounts, Microsoft and even with banks.
If we click on a link in the message, we will arrive at a very convincing website that, as I mentioned before, does not lack detail since it includes the logo and the rest of the elements of the official website. If we go ahead and follow all the steps, our account data will end up in the attacker’s hands. Now we are going to see a practical example of a Phishing attack on Instagram. The form of action is similar in the rest of the platforms because they use the same method.
One of the Phishing strategies they used was to send a message to Instagram users in which they offered a band or a special badge for our account, which obviously does not exist. The first thing we see is a message like this in order to get the promised badge / badge . Next, what we would have to do is click on Next .
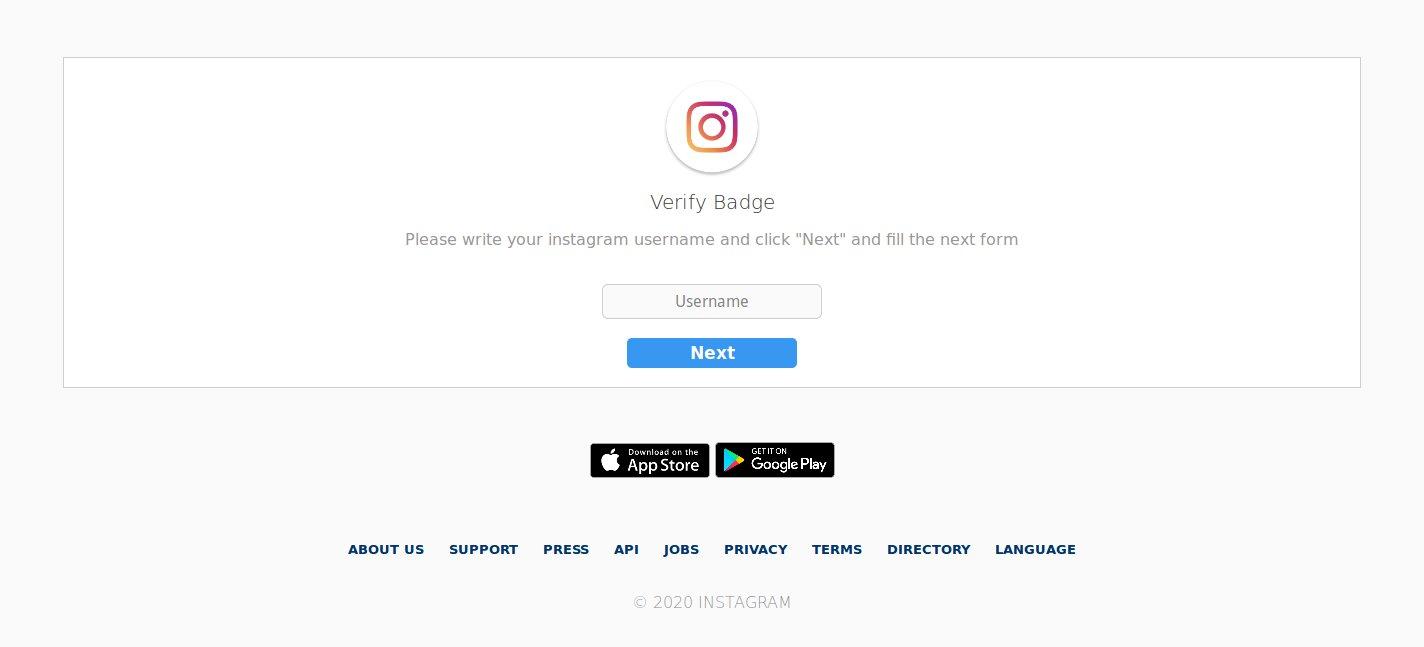
Then, in that form, we are asked to enter our Instagram username and password.
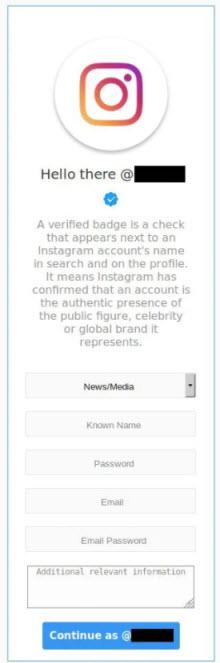
If we do, our account will unfortunately have fallen into the wrong hands.
Phishing on LinkedIn
The LinkedIn platform that many people use to search for a job, improve their current job or search the profile of a candidate for a position, is one of the platforms that has suffered the most from Phishing attacks.
In this case, we receive a message in which we are urged to click on a link, because otherwise, our LinkedIn account will be deactivated . As is usual, if we analyze it in depth, we would find that the sender’s address does not correspond to the domain. We will also discover the lack of personalization of the message and grammatical errors along with the link to a fake site. Lastly, if you complete all the steps to reassure the victim, it usually redirects them to the official LinkedIn website.
Phishing attacks on Twitter
On Twitter, the social network that talks about the most current trends is not spared from Phishing. In that sense, we must also be very attentive to the messages and links on which we click. Here we have an example of Twitter Phishing in which they seek to obtain the usual data: username and password.
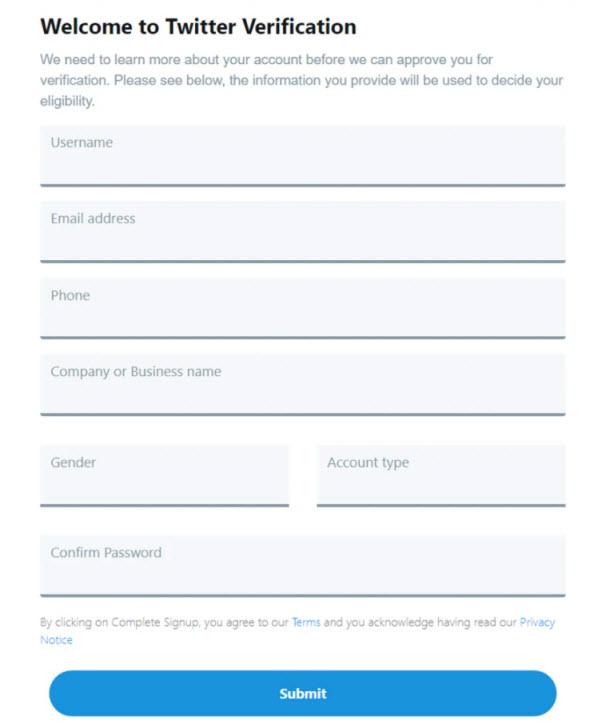
As you can see, in all these platforms they use similar Phishing strategies to steal our accounts.
What should I do if I make a mistake while entering the data
The first thing we must do is enter our Facebook, Instagram, LinkedIn or Twitter account and change the password immediately . In this sense, it should be noted that time is important, the sooner we solve it, the easier it will be that it does not have negative consequences for us. Finally, another thing that could help us is to activate multi-factor authentication if the platform supports it.