Phishing attacks are the order of the day and one of the preferred methods of cybercriminals. We have recently seen how companies used this technique to get employees’ Microsoft accounts and make a profit. Now it has also been known that phishing attacks on social media accounts are on the rise, especially targeting the social media of Twitter and Instagram.
Let’s start by briefly talking about what phishing consists of before getting into how it is affecting social networks.

Brief introduction to phishing
A phishing attack essentially seeks to steal our credentials and passwords. Its form of action consists of sending a message that impersonates the identity of a company or organization. In the case we are dealing with, it would be that of a social network such as Twitter, Instagram etc.

The message they receive may contain a malicious file or simply a link that takes us to a fraudulent website. We are facing a case of identity theft of a company and the victim will believe that it is on the official site. The objective is that the victim, when logging in normally, delivers their account data to the attacker .
Phishing attacks on social media accounts
Cybercriminals have set a new target for themselves and it is none other than our social media accounts. They are using phishing emails that claim to simulate copyright infringements or promises of a bright blue check mark next to their name.
Social media like Twitter, Facebook, Instagram, and TikTok have become an important part of our lives. These attackers know that they are important to us, and they try to snatch them from us and profit.
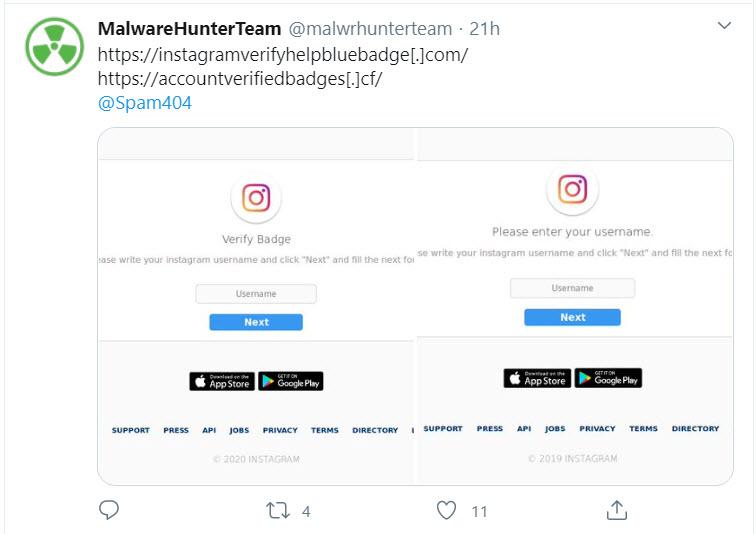
MalwareHunterTeam sounded the alarm
MalwareHunterTeam has been tracking numerous phishing campaigns targeting social media accounts and sharing them on its Twitter account. Here’s a preview of a tweet they posted on their account on the subject.
In this sense, it should be noted that the companies most affected by phishing social media accounts were Twitter, TikTok and Instagram.
Phishing attacks on Twitter, Instagram and TikTok
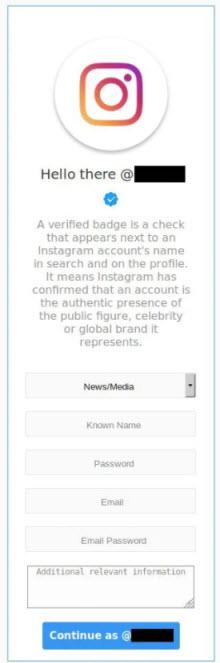
This phishing campaign that has become very popular promises that we will get a badge / badge on social networks such as TikTok, Instagram and Twitter. Users of these social networks are going to be asked to enter their username and password to be verified so that they can obtain their new badge. On Instagram we get a message like this so that we can fill out a form that we will access by clicking Next .
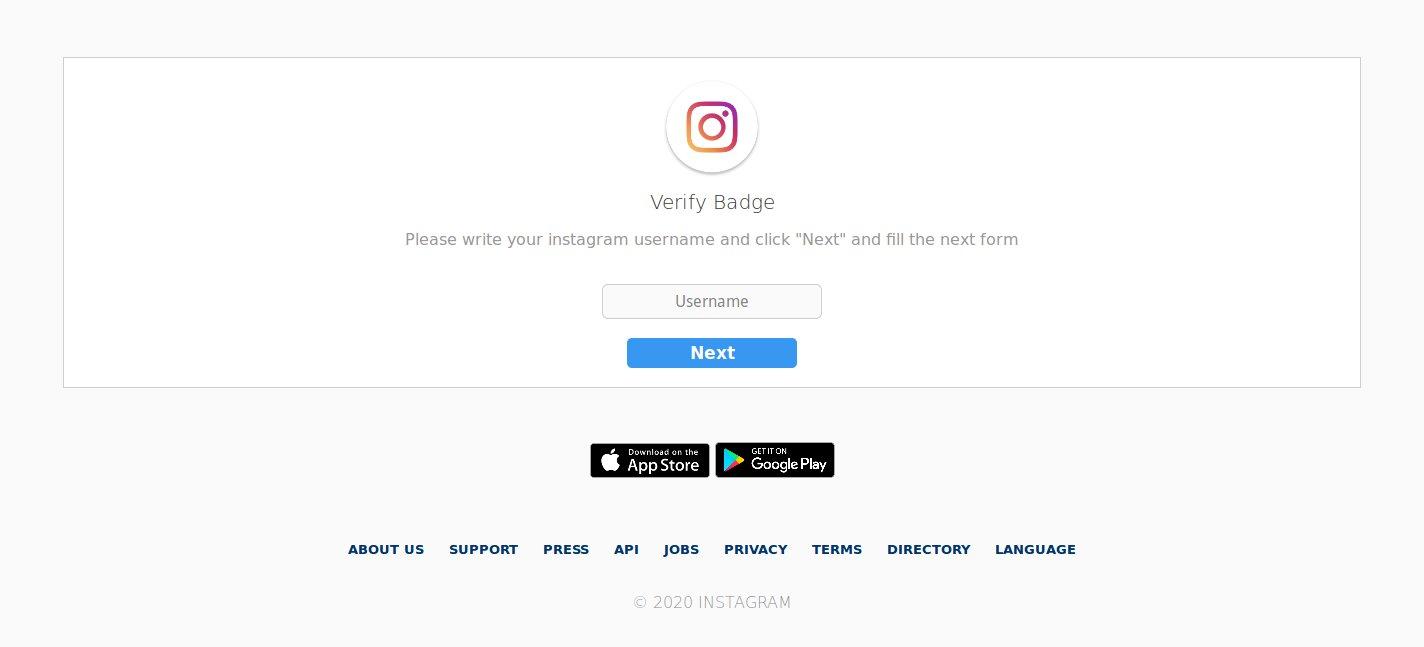
Then in that form we are asked to enter our Instagram username and password.
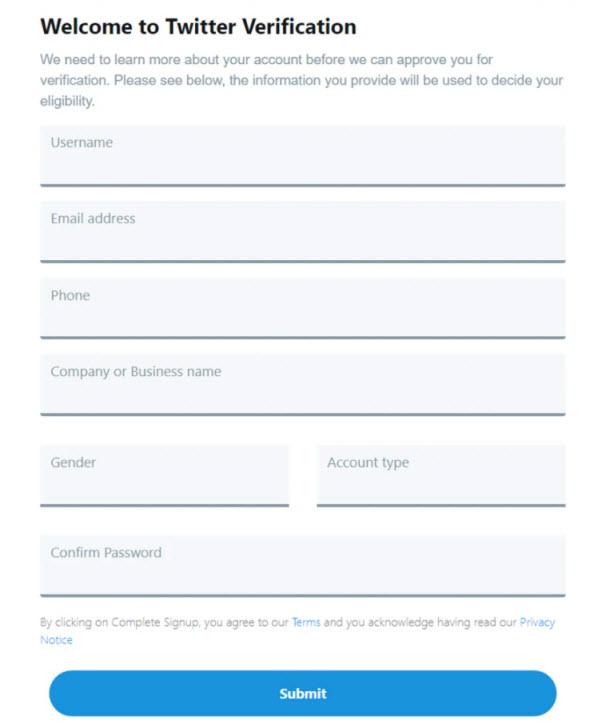
Also on Twitter they seek to obtain the same data: username, password and email.
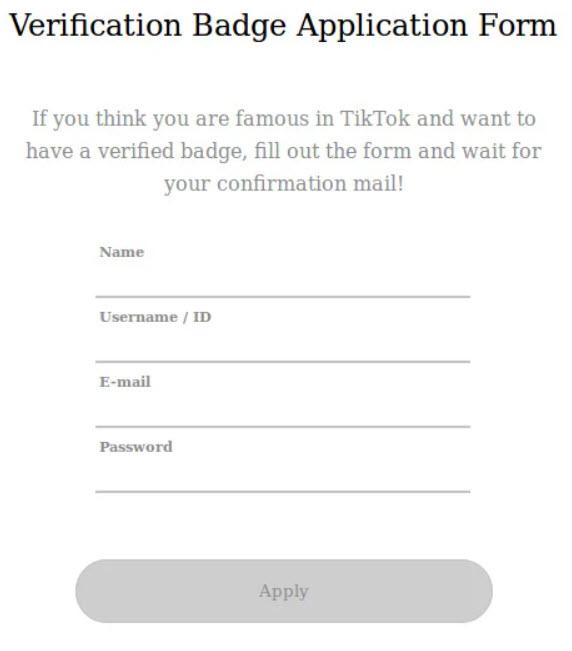
As for Tik Tok , we have this fraudulent form for its users to get their supposed shiny verification Badge or badge.
In case of falling into the trap, the attacker already has everything he needs to access our favorite social media account. It should also be noted that the Instagram phishing page notes the password of your email account. This gives the cybercriminal the ability to access other accounts.
How should I act if I make the mistake of entering my data
These types of frauds are frequent, fatigue or stress can make us not pay enough attention and see our data compromised. If you receive a phishing attack on social media accounts and you have the misfortune to be deceived, you must act quickly.
The first thing we must do is enter your TikTok, Instagram or Twitter account and then after logging in we change our password . In this case, it should be noted that time is vital, the sooner we act the easier it will be that it does not have negative consequences for us.
As we have already mentioned before, in some cases they asked us for our e-mail and password. If that is the case we must also change the password immediately. Also, if possible, enabling two-factor authentication is highly recommended. In this article we have a manual in which we explain how to protect our Google account and enable two-step verification. We recommend you read our tutorials on what is phishing and what types of phishing attacks exist .