A new strain of Android malware targeting customers of online banking and cryptocurrency wallets has been detected in Spain and Italy, just weeks after FluBot was brought down by law. In fact, its discovery occurred while this sophisticated Android malware was being investigated with the ability to take full remote control of the device, which was initially aimed at Spanish banking entities, but later broadened its sights to those of many other countries until it was finally recently dismantled. If you have a Santander or CaixaBank account, beware of this new Android virus.
The information-stealing Trojan, codenamed MaliBot according to F5 Labs, has a large number of features. It can range from stealing credentials and cookies to abusing the Android Accessibility Service to monitor the screen of its victims’ devices and bypass multi-factor authentication (MFA) codes that give logins greater protection. These are some of the possibilities of a virus that can do a lot of damage to its victims.

What is MaliBot and what is known about it?
What is known about MaliBot is that it is disguised as cryptocurrency mining applications , such as The CryptoApp or Mining X, and distributed through fraudulent websites that have been designed precisely to attract potential visitors to download them and that the Trojan can Act. On the other hand, it also uses smishing to spread the malware by accessing the contacts of the infected smartphone and sending SMS messages containing links to the malware. Once downloaded, MaliBot contacts the C2 server to register the infected device and asks the victim to grant access permissions.
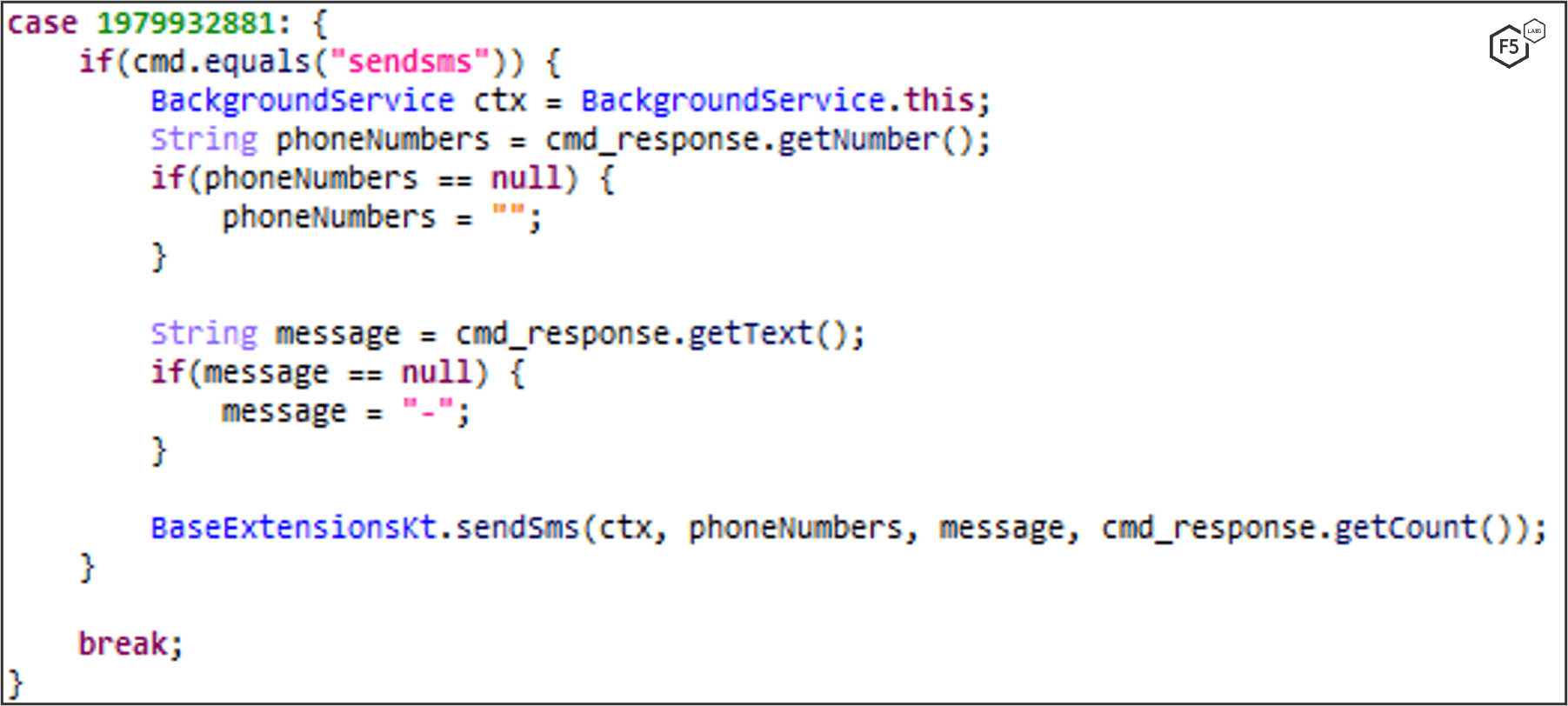
“The MaliBot Command and Control (C2) is in Russia and appears to use the same servers that were used to distribute the Sality malware,” according to F5 Labs researcher Dor Nizar. “It is a heavily modified reworking of the SOVA malware, with different functionalities, targets, C2 servers, domains, and packaging schemes.” For its part, the Sality virus would have been circulating freely since 2003 and would improve over time by adding new features.
SOVA (“Owl” in Russian), which was first detected in August 2021, is notable for its ability to perform overlay attacks that work by displaying a fraudulent page using WebView with a link provided by the C2 server if a victim opens a banking app included in your list of active targets. Some of MaliBot’s target banks using this approach include Santander, CaixaBank, UniCredit, and CartaBCC.
Its functions, mode of action and what it is used for
The Android Accessibility Service is a background service that runs on Android devices to help users with disabilities, but you can also use it if you’re comfortable with any of its features or capabilities. It has long been exploited by spyware and Trojans to capture device content and intercept credentials entered by unsuspecting users into other apps.
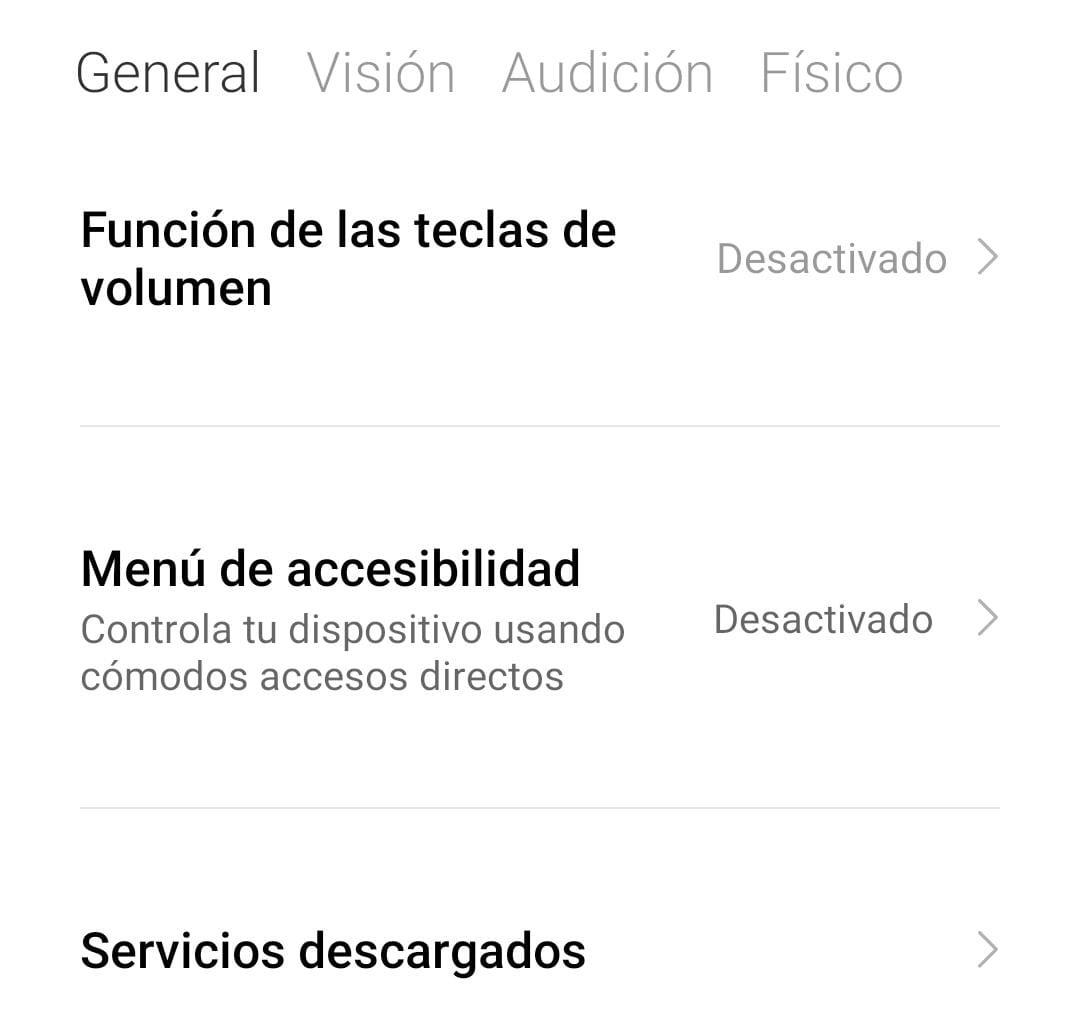
In addition to being able to bypass its victims’ Google account passwords and cookies, the malware is designed to crack 2FA codes from the Google Authenticator app, as well as leak sensitive information such as total balances and seed phrases from the Binance and Trust Wallet apps. Malibot is able to weaponize its Accessibility API access to defeat Google’s two-factor authentication (2FA) methods, even when trying to log into accounts using stolen credentials from a new unknown device.
All of these malware features could be used for much more than credential and cryptocurrency theft . In fact, any app that makes use of WebView is susceptible to stealing your credentials and cookies, even if initially its objectives are specific. So be careful, it can attack you without you realizing it!