There are many threats that circulate daily on the network. And there are many types of malware or viruses that can reach our electronic devices such as computers, tablets or mobile phones. Phishing or smishing attacks are the order of the day. They are techniques with which cybercriminals often impersonate the identity of some companies in order to get hold of our personal data. The truth is that a simple SMS is capable of infecting our Android mobile.
An analysis of phone account verification services (PVA) via SMS has brought to light a malicious platform built on a botnet involving thousands of infected Android phones, once again via an SMS like account validator.

An underground VPA service
SMS PVA services provide users with alternative mobile numbers that they can use to sign up for online services and platforms that help bypass SMS-based authentication and single sign-on mechanisms.
However, special care must be taken. “This type of service can be used by malicious actors to register disposable accounts en masse or create phone-verified accounts for fraud and other criminal activity,” Trend Micro researchers say in a report .
The service named smspva[.]net is made up of Android phones infected with malware that intercepts SMS. The researchers suspect that the mobile phones could have been infected in two ways. First of all, through malware accidentally downloaded by users. Second, through malicious software preloaded on Android devices during manufacturing, which would involve supply chain compromise.
Affected Phones: Inexpensive Android Devices
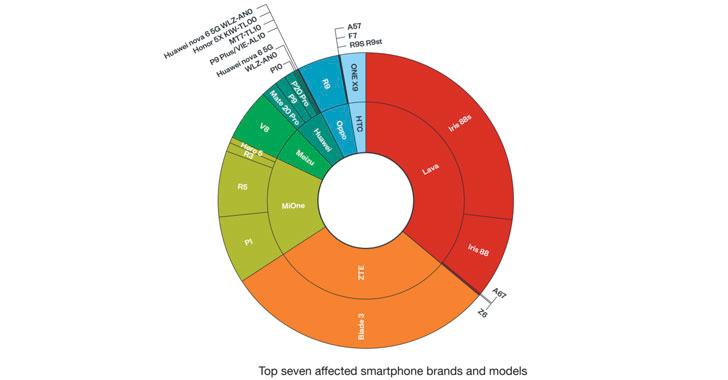
Telemetry data collected by the company reveals that the majority of affected devices are located in Indonesia (47,357), followed by Russia (16,157), Thailand (11,196), India (8,109), France (5,548), Peru (4,915). , Morocco (4,822), South Africa (4,413), Ukraine (2,920), and Malaysia (2,779). Also, they are largely cheap Android phones from manufacturers like Lava, ZTE, Mione, Meizu, Huawei, Oppo and HTC.
This underground service advertises bulk virtual phone numbers for use on various platforms through an API, as well as claiming to have phone numbers spanning over 100 countries.
Affected makes and models
This is plug.dex malware
A guerrilla malware that is designed to analyze the SMS received by the affected Android phone. It compares them to specific search patterns it receives from a remote server and then filters the messages that match those expressions back to the server.
“The malware remains low-profile, collecting only text messages that match the requested application so it can covertly continue this activity for long periods,” the researchers said. “If the PVA SMS service allows its customers to access all messages on infected phones, owners would quickly notice the problem.”
Websites authenticate new accounts by cross-location verification, i.e. using the users IP address during registration. SMS PVA services get around this restriction by using residential proxy servers and VPNs to connect to the desired platform. Also, these services only sell the one-time confirmation codes required at the time of account registration.
The botnet operator uses a multitude of compromised devices to receive, examine, and report SMS verification codes without the owners’ knowledge and consent. Consequently, the botnet provides easy access to thousands of mobile numbers in different countries, allowing criminals to register new accounts en masse and use them for various scams or even engage in coordinated actions by users who are not authentic. Concussively, the researchers state that “the presence of SMS PVA services makes another dent in the integrity of SMS verification as the primary means of account validation.”